Manual:Packet Flow: Difference between revisions
| (18 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
MikroTik RouterOS is designed to be easy to operate in various aspects of network configuration. Therefore creating limitation for individual IP or | {{Versions| v6.0+}} | ||
==Overview== | |||
MikroTik RouterOS is designed to be easy to operate in various aspects of network configuration. Therefore creating limitation for individual IP or NATting internal clients to a public address or Hotspot configuration can be done without the knowledge about how the packets are processed in the router - you just go to corresponding menu and create necessary configuration. | |||
However more complicated tasks, such as traffic prioritization, routing policies, where it is necessary to utilize more than one RouterOS facility, requires knowledge: How these facilities work together? What happens when and why? | However more complicated tasks, such as traffic prioritization, routing policies, where it is necessary to utilize more than one RouterOS facility, requires knowledge: How these facilities work together? What happens when and why? | ||
| Line 5: | Line 9: | ||
To address these questions we created a packet flow diagram. | To address these questions we created a packet flow diagram. | ||
== | ==Diagrams== | ||
For MikroTik RouterOS v6.0 was created detailed diagrams to ease understanding of packet flow. | |||
===Overall Packetflow Diagram=== | |||
[[Image:PacketFlowDiagram_v6_a.svg|Packet Flow Diagram|center]] | |||
===Bridging Diagram=== | |||
{| class="wikitable" | |||
|- | |||
|[[Image:Bridging-Diagram.jpg|450px|Bridging Diagram|center]] | |||
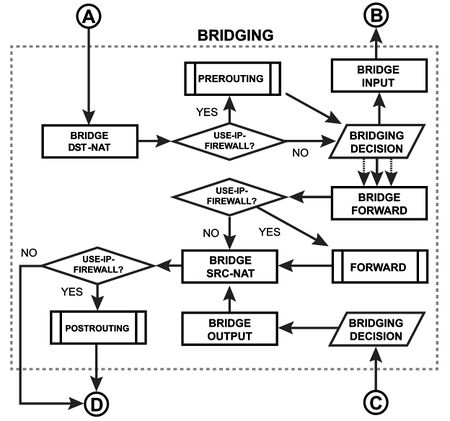
|In this subsection you can inspect how packet are going through the bridge. For example, if you configure <code>/interface bridge settings set use-ip-firewall=yes</code>, then packet will go through the one of three predefined ip firewall chains: prerouting, forward, postrouting. | |||
|} | |||
===MPLS Diagram=== | |||
{| class="wikitable" | |||
|- | |||
|Packet-forwarding decisions are made solely on the contents of this label, without the need to examine the packet itself. Diagram describe [https://wiki.mikrotik.com/wiki/Manual:MPLS MPLS] label movement in RouterOS. | |||
|[[Image:Mpls Diagram.jpg|600px|MPLS Diagram|center]] | |||
|} | |||
===Routing Diagram=== | |||
{| class="wikitable" | |||
|- | |||
|[[Image:Routing Diagram.jpg|450px|Routing Diagram|center]] | |||
|Each routing protocol (except BGP) has it's own internal tables. This is where per-protocol routing decisions are made. BGP does not have internal routing tables and stores complete routing information from all peers in the [https://wiki.mikrotik.com/wiki/Manual:IP/Route#Routing_Information_Base RIB]. RIB contains routes grouped in separate routing tables based on their value of routing-mark. All routes without routing-mark are kept in the main routing table. These tables are used for best route selection. The main table is also used for nexthop lookup. | |||
|} | |||
====Packet Flow Chains==== | |||
This diagram explains in detail each section of the Overall Packetflow Diagram. | |||
[[Image: | |||
[[Image:Pfd.png|Packet Flow Chains|840px|center]] | |||
==Diagram Analaysis== | |||
===Basic Concepts=== | |||
{| class="wikitable" | |||
|- | |||
! Image | |||
! Explanation | |||
|- | |||
|[[Image:Physical_in_interface.png|Input Interface|100px]] | |||
|Starting point in packets way through the router facilities. Packet is received it will start its way from here. | |||
[[Image: | |- | ||
|[[Image:Physical_out_interface.png|Output Interface|100px]] | |||
|Last point in packets way through the router facilities. Just before the packet is actually sent out. | |||
|- | |||
|[[Image:Logical_in_interface.png|Input Interface|100px]] | |||
|Intermediate interface where packet continues to process through the device after decapsulation | |||
|- | |||
|[[Image:Logical_out_interface.png |Output Interface|100px]] | |||
|Intermediate interface where packet continue to process through the device before encapsulation | |||
|- | |||
|[[Image:local_process-_in.jpg|Local Process IN|100px]] | |||
|Last point in packets way <b>to</b> router itself, after this packet is discarded | |||
|- | |||
|[[Image:local_process-_out.jpg|Local Process OUT|100px]] | |||
|Starting point for packets generated by router itself | |||
|} | |||
[[Image:local_process-_out.jpg|Local Process OUT|100px]] | |||
===Configurable Facilities=== | ===Configurable Facilities=== | ||
| Line 40: | Line 75: | ||
Each and every facilities in this section corresponds with one particular menu in RouterOS. Users are able to access those menu and configure these facilities directly | Each and every facilities in this section corresponds with one particular menu in RouterOS. Users are able to access those menu and configure these facilities directly | ||
{| class="wikitable" | |||
[[Image:connection_tracking.jpg|Connection Tracking|100px]] | |- | ||
! Image | |||
[[Image:Filter_input.jpg|Filter Input|100px]] | ! RouterOS CLI | ||
[[Image:Filter_forward.jpg|Filter Forward|100px]] | |- | ||
[[Image:Filter_output.jpg|Filter Output|100px]] | | [[Image:connection_tracking.jpg|Connection Tracking|100px]] | ||
| <code>/ip firewall connection tracking</code> | |||
[[Image:src_nat.jpg|Source NAT|100px]] | |- | ||
[[Image:dst_nat.jpg|Destination NAT|100px]] | | [[Image:Filter_input.jpg|Filter Input|100px]] | ||
| <code>/ip firewall filter</code> | |||
[[Image:mangle_prerouting.jpg|Mangle Prerouting|100px]] | |- | ||
[[Image:mangle_input.jpg|Mangle Input|100px]] | | [[Image:Filter_forward.jpg|Filter Forward|100px]] | ||
[[Image:mangle_forward.jpg|Mangle Forward|100px]] | | <code>/ip firewall filter</code> | ||
[[Image:mangle_output.jpg|Mangle Output|100px]] | |- | ||
[[Image:mangle_postrouting.jpg|Mangle Postrouting|100px]] | | [[Image:Filter_output.jpg|Filter Output|100px]] | ||
| <code>/ip firewall filter</code> | |||
[[Image:global_in.jpg|Global-in HTB|100px]] | |- | ||
[[Image:global_out.jpg|Global-Out HTB|100px]] | | [[Image:src_nat.jpg|Source NAT|100px]] | ||
[[Image:Interface HTB.jpg|Interface HTB|100px]] | | <code>/ip firewall nat</code> | ||
|- | |||
[[Image:IPsec_policy.jpg|IPSec_Policy|100px]] | | [[Image:dst_nat.jpg|Destination NAT|100px]] | ||
| <code>/ip firewall nat</code> | |||
[[Image:accounting.jpg|Accounting|100px]] | |- | ||
|[[Image:mangle_prerouting.jpg|Mangle Prerouting|100px]] | |||
[[Image:use_ip_firewall.jpg|Use IP Firewall|100px]] | |<code>/ip firewall mangle</code> | ||
|- | |||
[[Image:bridge_input.jpg|Bridge Input|100px]] | |[[Image:mangle_input.jpg|Mangle Input|100px]] | ||
[[Image:Bridge_forward.jpg|Bridge Forward|100px]] | |<code>/ip firewall mangle</code> | ||
[[Image:Bridge_output.jpg|Bridge Output|100px]] | |- | ||
|[[Image:mangle_forward.jpg|Mangle Forward|100px]] | |||
[[Image:Bridge_dst_nat.jpg|Bridge Destination NAT|100px]] | |<code>/ip firewall mangle</code> | ||
[[Image:Bridge_src_nat.jpg|Bridge Source NAT|100px]] | |- | ||
|[[Image:mangle_output.jpg|Mangle Output|100px]] | |||
|<code>/ip firewall mangle</code> | |||
|- | |||
|[[Image:mangle_postrouting.jpg|Mangle Postrouting|100px]] | |||
|<code>/ip firewall mangle</code> | |||
|- | |||
|[[Image:global_in.jpg|Global-in HTB|100px]] | |||
| <code>/queue simple</code> and <code>/queue tree</code> | |||
|- | |||
| [[Image:global_out.jpg|Global-Out HTB|100px]] | |||
| <code>/queue simple</code> and <code>/queue tree</code> | |||
|- | |||
| [[Image:Interface HTB.jpg|Interface HTB|100px]] | |||
| <code>/queue simple</code> and <code>/queue tree</code> | |||
|- | |||
| [[Image:IPsec_policy.jpg|IPSec_Policy|100px]] | |||
| <code>/ip ipsec policy</code> | |||
|- | |||
| [[Image:accounting.jpg|Accounting|100px]] | |||
| <code>/ip accounting</code> | |||
|- | |||
|[[Image:use_ip_firewall.jpg|Use IP Firewall|100px]] | |||
|<code>/interface bridge settings</code> | |||
|- | |||
|[[Image:bridge_input.jpg|Bridge Input|100px]] | |||
|<code>/interface bridge filter</code> | |||
|- | |||
|[[Image:Bridge_forward.jpg|Bridge Forward|100px]] | |||
|<code>/interface bridge filter</code> | |||
|- | |||
|[[Image:Bridge_output.jpg|Bridge Output|100px]] | |||
|<code>/interface bridge filter</code> | |||
|- | |||
|[[Image:Bridge_dst_nat.jpg|Bridge Destination NAT|100px]] | |||
|<code>/interface bridge nat</code> | |||
|- | |||
|[[Image:Bridge_src_nat.jpg|Bridge Source NAT|100px]] | |||
|<code>/interface bridge nat</code> | |||
|} | |||
===Automated processes and decisions === | ===Automated processes and decisions === | ||
[[Image:In-interface-bridge.jpg|In-interface Bridge|100px]] | {| class="wikitable" | ||
|- | |||
[[Image: | !Image | ||
!Description | |||
[[Image:Bridge Desicion.jpg|Bridge Decision|100px]] | |- | ||
|[[Image:In-interface-bridge.jpg|In-interface Bridge|100px]] | |||
[[Image:bridge_decision.jpg|Bridge Decision|100px]] | |Check if the ''actual input interface'' is a port for bridge OR checks if ''input interface'' is bridge | ||
|- | |||
[[Image:routing_decision.JPG|Routing Decision|100px]] | |[[Image:HOTSPOT_in.png|Hotspot In|100px]] | ||
|Allow to capture traffic witch otherwise would be discarded by connection tracking - this way our Hotspot feature are able to provide connectivity even if networks settings are in complete mess | |||
[[Image:routing_adjustment.jpg|Routing Adjustment|100px]] | |- | ||
|[[Image:Bridge Desicion.jpg|Bridge Decision|100px]] | |||
[[Image:TTL | |Bridge goes through the MAC address table in order to find a match to destination MAC address of packet. When match is found - packet will be send out via corresponding bridge port. In case of no match - multiple copies of packet will be created and packet will be sent out via all bridge ports | ||
|- | |||
[[Image: | |[[Image:bridge_decision.jpg|Bridge Decision|100px]] | ||
|This is a workaround, allows to use "out-bridge-port" before actual bridge decision. | |||
[[Image:out_interface_bridge.jpg|Out-interface Bridge|100px]] | |- | ||
|[[Image:routing_decision.JPG|Routing Decision|100px]] | |||
[[Image: | |Router goes through the route n order to find a match to destination IP address of packet. When match is found - packet will be send out via corresponding port or to the router itself . In case of no match - packet will be discarded. | ||
|- | |||
|[[Image:routing_adjustment.jpg|Routing Adjustment|100px]] | |||
|This is a workaround that allows to set-up policy routing in mangle chain output | |||
|- | |||
|[[Image:TTL.png|TTL Adjustment|100px]] | |||
|Indicates exact place where Time To Live (TTL) of the routed packet is reduced by 1. If it become 0 packet will be discarded | |||
|- | |||
|[[Image:IPSEC_decryption.png|IPSec_Decryption|100px]] | |||
|Self explanatory | |||
|- | |||
|[[Image:IPSEC_encryption.png|IPSec_Encryption|100px]] | |||
|Self explanatory | |||
|- | |||
|[[Image:out_interface_bridge.jpg|Out-interface Bridge|100px]] | |||
|Check if the ''actual output interface'' is a port for bridge OR checks if ''output interface'' is bridge | |||
|- | |||
|[[Image:Hotspot_out2.png|Hotspot Out|100px]] | |||
|Undo all that was done by hotspot-in for the packets that is going back to client. | |||
|} | |||
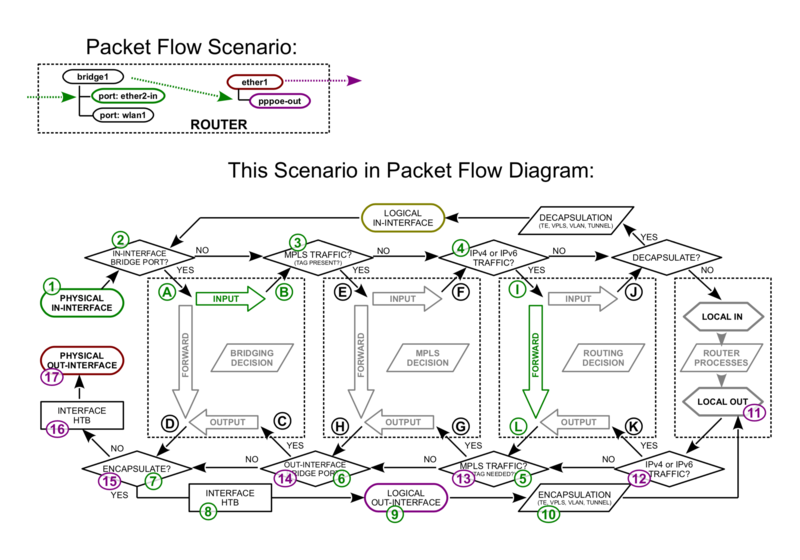
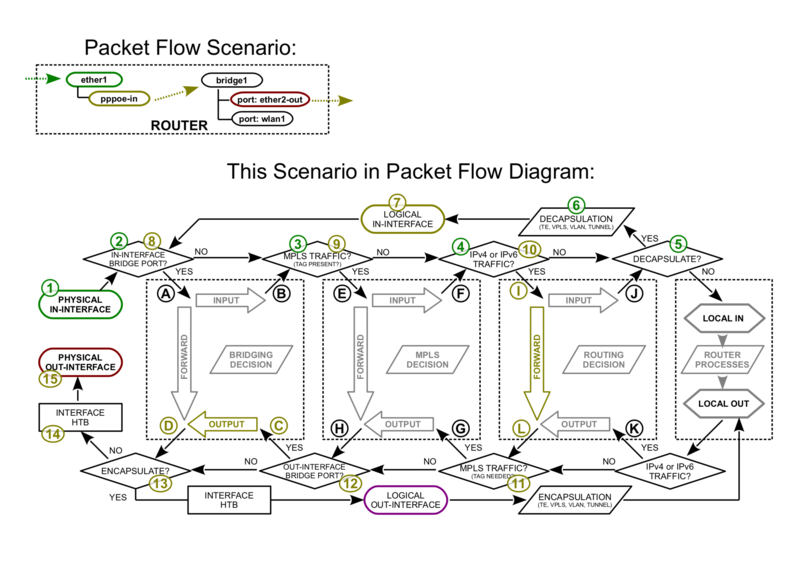
==Examples== | ==Examples== | ||
In this subsection you can overview different protocol packet processing in RouterOS. | |||
[[ | ===Bridge port in with PPPoE-out=== | ||
[[ | [[File:Packetflow6-a.png|Example 1|800px|center]] | ||
===PPPoE-in with bridge port out=== | |||
[[File:Packetflow6-b.png|Example 2|800px|center]] | |||
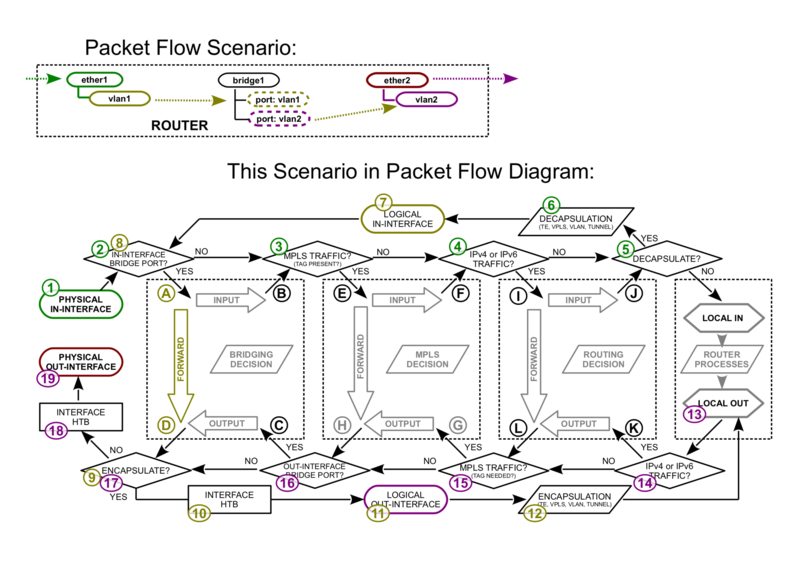
===Vlan Untagging/Tagging in the bridge interface=== | |||
[[File:Packetflow6-c.png|Example 3|800px|center]] | |||
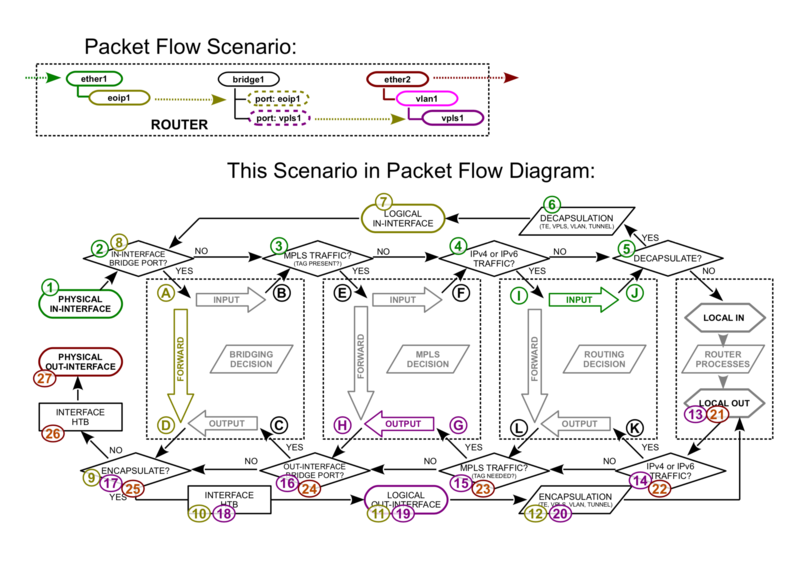
===EoIP with VPLS out=== | |||
[[File:Packetflow6-d.png|Example 4|800px|center]] | |||
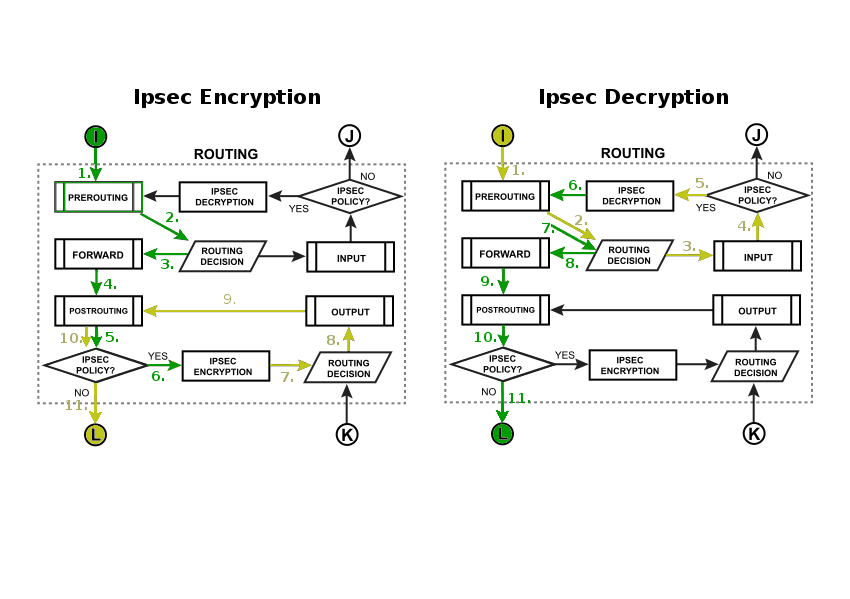
===IPsec Encryption/Decryption=== | |||
[https://wiki.mikrotik.com/wiki/Manual:IP/IPsec Internet Protocol Security (IPsec)] is a set of protocols defined by the Internet Engineering Task Force (IETF) to secure packet exchange over unprotected IP/IPv6 networks such as Internet. | |||
[[Image:IpsecFlow.png|Example 5|center]] | |||
Latest revision as of 13:30, 8 January 2019
Overview
MikroTik RouterOS is designed to be easy to operate in various aspects of network configuration. Therefore creating limitation for individual IP or NATting internal clients to a public address or Hotspot configuration can be done without the knowledge about how the packets are processed in the router - you just go to corresponding menu and create necessary configuration.
However more complicated tasks, such as traffic prioritization, routing policies, where it is necessary to utilize more than one RouterOS facility, requires knowledge: How these facilities work together? What happens when and why?
To address these questions we created a packet flow diagram.
Diagrams
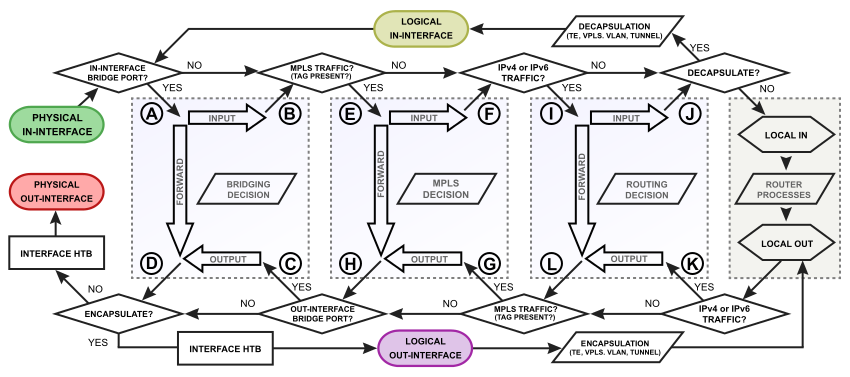
For MikroTik RouterOS v6.0 was created detailed diagrams to ease understanding of packet flow.
Overall Packetflow Diagram
Bridging Diagram
MPLS Diagram
| Packet-forwarding decisions are made solely on the contents of this label, without the need to examine the packet itself. Diagram describe MPLS label movement in RouterOS. | 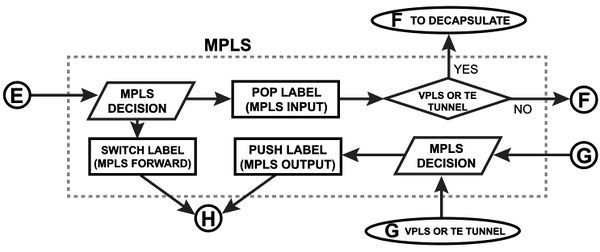 |
Routing Diagram
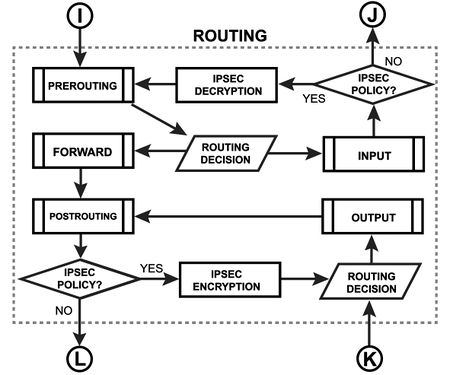 |
Each routing protocol (except BGP) has it's own internal tables. This is where per-protocol routing decisions are made. BGP does not have internal routing tables and stores complete routing information from all peers in the RIB. RIB contains routes grouped in separate routing tables based on their value of routing-mark. All routes without routing-mark are kept in the main routing table. These tables are used for best route selection. The main table is also used for nexthop lookup. |
Packet Flow Chains
This diagram explains in detail each section of the Overall Packetflow Diagram.
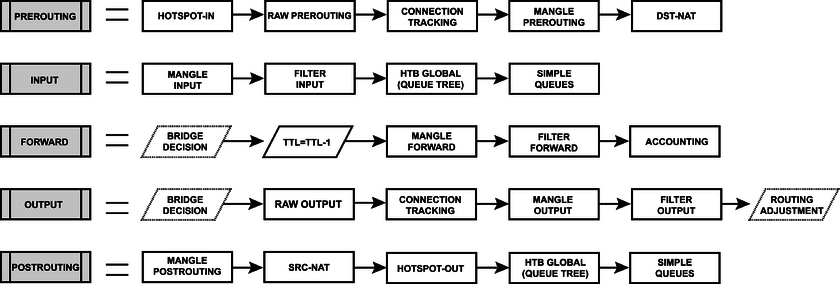
Diagram Analaysis
Basic Concepts
Configurable Facilities
Each and every facilities in this section corresponds with one particular menu in RouterOS. Users are able to access those menu and configure these facilities directly
Automated processes and decisions
Examples
In this subsection you can overview different protocol packet processing in RouterOS.
Bridge port in with PPPoE-out
PPPoE-in with bridge port out
Vlan Untagging/Tagging in the bridge interface
EoIP with VPLS out
IPsec Encryption/Decryption
Internet Protocol Security (IPsec) is a set of protocols defined by the Internet Engineering Task Force (IETF) to secure packet exchange over unprotected IP/IPv6 networks such as Internet.