Manual:IP/IPsec: Difference between revisions
No edit summary |
|||
| (39 intermediate revisions by 5 users not shown) | |||
| Line 1: | Line 1: | ||
{{Versions | v6.0 +}} | {{Versions | v6.0 +}} | ||
{{Warning | Article is migrated to our new manual: https://help.mikrotik.com/docs/display/ROS/IPsec }} | |||
==Summary== | ==Summary== | ||
| Line 232: | Line 234: | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/netmetal_ac2 RBD23UGS-5HPacD2HnD-NM (NetMetal ac²)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/audience RBD25G-5HPacQD2HPnD (Audience)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/audience_lte6_kit RBD25GR-5HPacQD2HPnD&R11e-LTE6 (Audience LTE6 kit)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/hap_ac2 RBD52G-5HacD2HnD (hAP ac<sup>2</sup>)] *</td> | <tr><td>[https://mikrotik.com/product/hap_ac2 RBD52G-5HacD2HnD (hAP ac<sup>2</sup>)] *</td> | ||
| Line 238: | Line 258: | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/hap_ac3_lte6_kit RBD53GR-5HacD2HnD&R11e-LTE6 (hAP ac<sup>3</sup> LTE6 kit)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/chateau_lte12 RBD53G-5HacD2HnD-TC&EG12-EA (Chateau LTE12)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/disc_lite5_ac RBDiscG-5acD (DISC Lite5 ac)] *</td> | <tr><td>[https://mikrotik.com/product/disc_lite5_ac RBDiscG-5acD (DISC Lite5 ac)] *</td> | ||
| Line 256: | Line 288: | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/lhg_xl_52_ac RBLHGG-5HPacD2HPnD-XL (LHG XL 52 ac)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/lhg_xl_5_ac RBLHGG-5acD-XL (LHG XL 5 ac)] *</td> | <tr><td>[https://mikrotik.com/product/lhg_xl_5_ac RBLHGG-5acD-XL (LHG XL 5 ac)] *</td> | ||
| Line 269: | Line 307: | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/ | <tr><td>[https://mikrotik.com/product/ltap RBLtAP-2HnD (LtAP)] ****</td> | ||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
| Line 275: | Line 313: | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/ | <tr><td>[https://mikrotik.com/product/ltap_lte_kit RBLtAP-2HnD&R11e-LTE (LtAP LTE kit)] ****</td> | ||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
| Line 281: | Line 319: | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/sxtsq_5_ac RBSXTsqG-5acD (SXTsq 5 ac)] *</td> | <tr><td>[https://mikrotik.com/product/ltap_4g_kit RBLtAP-2HnD&R11e-4G (LtAP 4G kit)] ****</td> | ||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/ltap_lte6_kit RBLtAP-2HnD&R11e-LTE6 (LtAP LTE6 kit)] ****</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/m11g RBM11G] ****</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/rbm33g RBM33G] ****</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/sxtsq_5_ac RBSXTsqG-5acD (SXTsq 5 ac)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
| Line 299: | Line 361: | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/ | <tr><td>[https://mikrotik.com/product/wap_r_ac RBwAPGR-5HacD2HnD (wAP R ac)] *</td> | ||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
| Line 305: | Line 367: | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/ | <tr><td>[https://mikrotik.com/product/wap_ac_lte_kit RBwAPGR-5HacD2HnD&R11e-LTE (wAP ac LTE kit)] *</td> | ||
<!-- DES and 3DES --><td style="background-color: | <!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color: | <!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color: | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | <!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | ||
<tr><td>[https://mikrotik.com/product/hex_s RB760iGS (hEX S)] ****</td> | <tr><td>[https://mikrotik.com/product/wap_ac_4g_kit RBwAPGR-5HacD2HnD&R11e-4G (wAP ac 4G kit)] *</td> | ||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/wap_ac_lte6_kit RBwAPGR-5HacD2HnD&R11e-LTE6 (wAP ac LTE6 kit)] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/rb450gx4 RB450Gx4] *</td> | |||
<!-- DES and 3DES --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/RB750Gr3 RB750Gr3 (hEX)] ****</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | |||
<!-- AES-GCM --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td></tr> | |||
<tr><td>[https://mikrotik.com/product/hex_s RB760iGS (hEX S)] ****</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
| Line 324: | Line 410: | ||
<tr><td>[https://mikrotik.com/product/RB1100AHx2 RB1100AHx2]</td> | <tr><td>[https://mikrotik.com/product/RB1100AHx2 RB1100AHx2]</td> | ||
<!-- DES and 3DES --><td style="background-color: | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightpink">no</td> | ||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | ||
<!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | <!-- AES-CTR --><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td><td style="background-color:lightpink">no</td> | ||
| Line 348: | Line 434: | ||
<tr><td>[https://mikrotik.com/product/rb4011igs_rm RB4011iGS+RM] and [https://mikrotik.com/product/rb4011igs_5hacq2hnd_in RB4011iGS+5HacQ2HnD-IN]</td> | <tr><td>[https://mikrotik.com/product/rb4011igs_rm RB4011iGS+RM] and [https://mikrotik.com/product/rb4011igs_5hacq2hnd_in RB4011iGS+5HacQ2HnD-IN]</td> | ||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | |||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | |||
<!-- AES-CTR --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | |||
<!-- AES-GCM --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td></tr> | |||
<tr><td>[https://mikrotik.com/product/ccr2004_1g_12s_2xs CCR2004-1G-12S+2XS]</td> | |||
<!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | <!-- DES and 3DES --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | ||
<!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | <!-- AES-CBC --><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td><td style="background-color:lightgreen">yes</td> | ||
| Line 418: | Line 510: | ||
|type=IP/IPv6 prefix | |type=IP/IPv6 prefix | ||
|default=0.0.0.0/32 | |default=0.0.0.0/32 | ||
|desc=Destination address to be matched in packets. | |desc=Destination address to be matched in packets. Applicable when tunnel mode (<var>tunnel=yes</var>) or template (<var>template=yes</var>) is used. | ||
}} | }} | ||
| Line 451: | Line 543: | ||
* <var>require</var> - drop packet and acquire SA; | * <var>require</var> - drop packet and acquire SA; | ||
* <var>unique</var> - drop packet and acquire a unique SA that is only used with this particular policy. It is used in setups where multiple clients can sit behind one public IP address (clients behind NAT). | * <var>unique</var> - drop packet and acquire a unique SA that is only used with this particular policy. It is used in setups where multiple clients can sit behind one public IP address (clients behind NAT). | ||
}} | |||
{{Mr-arg-table | |||
|arg=peer | |||
|type=string | |||
|default= | |||
|desc=Name of the [[#Peers | peer]] on which the policy applies. | |||
}} | }} | ||
| Line 457: | Line 556: | ||
|type=string | |type=string | ||
|default=default | |default=default | ||
|desc=Name of the [[# | |desc=Name of the [[#Proposals| proposal template]] that will be sent by IKE daemon to establish SAs for this policy. | ||
}} | }} | ||
| Line 468: | Line 567: | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg=src-address | |||
|arg=src-address | |||
|type=ip/ipv6 prefix | |type=ip/ipv6 prefix | ||
|default=0.0.0.0/32 | |default=0.0.0.0/32 | ||
|desc=Source address to be matched in packets. | |desc=Source address to be matched in packets. Applicable when tunnel mode (<var>tunnel=yes</var>) or template (<var>template=yes</var>) is used. | ||
}} | }} | ||
| Line 559: | Line 644: | ||
}} | }} | ||
{{Mr-arg- | {{Mr-arg-table | ||
|arg= | |arg=sa-dst-address | ||
|type= | |type=ip/ipv6 address | ||
|desc= | |default=:: | ||
|desc=SA destination IP/IPv6 address (remote peer). | |||
}} | |||
{{Mr-arg-table-end | |||
|arg=sa-src-address | |||
|type=ip/ipv6 address | |||
|default=:: | |||
|desc=SA source IP/IPv6 address (local peer). | |||
}} | }} | ||
| Line 742: | Line 835: | ||
}} | }} | ||
== | ==Proposals== | ||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec proposal</code></p> | <p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec proposal</code></p> | ||
| Line 870: | Line 963: | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg=comment | |||
|type=string | |||
|default= | |||
|arg=comment | |||
|type=string | |||
|default= | |||
|desc=Short description of the peer. | |desc=Short description of the peer. | ||
}} | }} | ||
| Line 913: | Line 978: | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg=exchange-mode | |arg=exchange-mode | ||
|type=aggressive {{!}} base {{!}} main | |type=aggressive {{!}} base {{!}} main {{!}} ike2 | ||
|default=main | |default=main | ||
|desc=Different ISAKMP phase 1 exchange modes according to RFC 2408 | |desc=Different ISAKMP phase 1 exchange modes according to RFC 2408. | ||
'''main | '''main''' mode relaxes rfc2409 section 5.4, to allow pre-shared-key authentication in main mode. <var>ike2</var> mode enables Ikev2 RFC 7296. Parameters that are ignored by IKEv2 <var>proposal-check</var>, <var>compatibility-options</var>, <var>lifebytes</var>, <var>dpd-maximum-failures</var>, <var>nat-traversal</var>. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=local-address | ||
|type= | |type=IP/IPv6 Address | ||
|default= | |default= | ||
|desc= | |desc=Routers local address on which Phase 1 should be bounded to. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=name | ||
|type=string | |type=string | ||
|default= | |default= | ||
|desc= | |desc= | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg=passive | |||
|type=yes {{!}} no | |||
|default=no | |||
|arg=passive | |||
|type=yes {{!}} no | |||
|default=no | |||
|desc=When passive mode is enabled will wait for remote peer to initiate IKE connection. Enabled passive mode also indicates that peer is xauth responder, and disabled passive mode - xauth initiator. When passive mode is disabled peer will try to establish not only phase1, but also phase2 automatically, if policies are configured or created during phase1. | |desc=When passive mode is enabled will wait for remote peer to initiate IKE connection. Enabled passive mode also indicates that peer is xauth responder, and disabled passive mode - xauth initiator. When passive mode is disabled peer will try to establish not only phase1, but also phase2 automatically, if policies are configured or created during phase1. | ||
}} | }} | ||
| Line 997: | Line 1,016: | ||
|type=string | |type=string | ||
|default=default | |default=default | ||
|desc=Name of the [[# | |desc=Name of the [[#Profiles| profile template]] that will be used during IKE negotiation. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table-end | ||
|arg=send-initial-contact | |||
|arg=send-initial-contact | |||
|type=yes {{!}} no | |type=yes {{!}} no | ||
|default=yes | |default=yes | ||
|desc=Specifies whether to send "initial contact" IKE packet or wait for remote side, this packet should trigger removal of old peer SAs for current source address. | |desc=Specifies whether to send "initial contact" IKE packet or wait for remote side, this packet should trigger removal of old peer SAs for current source address. | ||
Usually in road warrior setups clients are initiators and this parameter should be set to no. Initial contact is not sent if modecfg or xauth is enabled for ikev1. | Usually in road warrior setups clients are initiators and this parameter should be set to no. Initial contact is not sent if modecfg or xauth is enabled for ikev1. | ||
}} | }} | ||
| Line 1,060: | Line 1,050: | ||
==Identities== | |||
== | |||
Identities are configuration parameters that are specific to the remote peer. Main purpose of an identity is to handle authentication and verify peer's integrity. | |||
'''Properties''' | '''Properties''' | ||
| Line 1,077: | Line 1,062: | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=auth-method | ||
|type= | |type=digital-signature {{!}} eap {{!}} eap-radius {{!}} pre-shared-key {{!}} pre-shared-key-xauth {{!}} rsa-key {{!}} rsa-signature-hybrid | ||
|default= | |default=pre-shared-key | ||
|desc=[[# | |desc=Authentication method: | ||
* <var>digital-signature</var> - authenticate using a pair of RSA certificates; | |||
* <var>eap</var> - IKEv2 EAP authentication for initiator (peer with netmask of /32). Must be used together with <var>eap-methods</var>; | |||
* <var>eap-radius</var> - IKEv2 EAP RADIUS passthrough authentication for responder (RFC 3579). Server certificate in this case is required. If server certificate is not specified then only clients supporting EAP-only (RFC 5998) will be able to connect. Note that EAP method should be compatible with EAP-only; | |||
* <var>pre-shared-key</var> - authenticate by a password (pre-shared secret) string shared between the peers (not recommended since offline attack on pre-shared key is possible); | |||
* <var>rsa-key</var> - authenticate using a RSA key imported in [[#Keys | keys]] menu. Only supported in IKEv1; | |||
* <var>pre-shared-key-xauth</var> - authenticate by a password (pre-shared secret) string shared between the peers + XAuth username and password. Only supported in IKEv1; | |||
* <var>rsa-signature-hybrid</var> - responder certificate authentication with initiator XAuth. Only supported in IKEv1. | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=certificate | ||
|type= | |type=string | ||
|default= | |default= | ||
|desc= | |desc=Name of a certificate listed in [[M:System/Certificates | System/Certificates]] (signing packets; the certificate must have private key). Applicable if digital signature authentication method (<var>auth-method=digital-signature</var>) or EAP (<var>auth-method=eap</var>) is used. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=comment | ||
|type= | |type=string | ||
|default= | |default= | ||
|desc= | |desc=Short description of the identity. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=disabled | ||
|type= | |type=yes {{!}} no | ||
|default= | |default=no | ||
|desc= | |desc=Whether identity is used to match remote peer. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=eap-methods | ||
|type= | |type=eap-mschapv2 {{!}} eap-peap {{!}} eap-tls {{!}} eap-ttls | ||
|default= | |default=eap-tls | ||
|desc= | |desc=All EAP methods requires whole certificate chain including intermediate and root CA certificates to be present in [[M:System/Certificates | System/Certificates]] menu. Also <var>username</var> and <var>password</var> (if required by authentication server) must be specified. Multiple EAP methods may be specified and will be used in specified order. Currently supported EAP methods: | ||
* <var>eap-mschapv2</var>; | |||
* <var>eap-peap</var> - also known as PEAPv0/EAP-MSCHAPv2; | |||
* <var>eap-tls</var> - requires additional client certificate specified under <var>certificate</var> parameter; | |||
* <var>eap-ttls</var>. | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=generate-policy | ||
|type= | |type=no {{!}} port-override {{!}} port-strict | ||
|default= | |default=no | ||
|desc= | |desc=Allow this peer to establish SA for non-existing policies. Such policies are created dynamically for the lifetime of SA. Automatic policies allows, for example, to create IPsec secured [[M:Interface/L2TP | L2TP]] tunnels, or any other setup where remote peer's IP address is not known at the configuration time. | ||
* <var>no</var> - do not generate policies; | |||
* <var>port-override</var> - generate policies and force policy to use '''any''' port (old behavior); | |||
* <var>port-strict</var> - use ports from peer's proposal, which should match peer's policy. | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=key | ||
|type= | |type=string | ||
|default= | |default= | ||
|desc= | |desc=Name of the private key from [[#Keys | keys]] menu. Applicable if RSA key authentication method (<var>auth-method=rsa-key</var>) is used. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=match-by | ||
|type= | |type=remote-id {{!}} certificate | ||
|default= | |default=remote-id | ||
|desc= | |desc=Defines the logic used for peer's identity validation. | ||
* <var>remote-id</var> - will verify the peer's ID according to <var>remote-id</var> setting. | |||
* <var>certificate</var> will verify the peer's certificate with what is specified under <var>remote-certificate</var> setting. | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=mode-config | ||
|type= | |type=none {{!}} *request-only {{!}} string | ||
|default= | |default=none | ||
|desc= | |desc=Name of the configuration parameters from [[#Mode_Configs | mode-config]] menu. When parameter is set mode-config is enabled. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=my-id | ||
|type= | |type=auto {{!}} address {{!}} fqdn {{!}} user-fqdn {{!}} key-id | ||
|default= | |default=auto | ||
|desc= | |desc=On initiator, this controls what ID_i is sent to the responder. On responder, this controls what ID_r is sent to the initiator. In IKEv2, responder also expects this ID in received ID_r from initiator. | ||
* <var> | * <var>auto</var> - tries to use correct ID automatically; | ||
* <var> | * <var>address</var> - IP address is used as ID; | ||
* <var> | * <var>fqdn</var> - fully qualified domain name; | ||
* <var> | * <var>key-id</var> - use the specified key ID for the identity; | ||
* <var>user fqdn</var> - specifies a fully-qualified username string, for example, "user@domain.com". | |||
}} | }} | ||
== | {{Mr-arg-table | ||
|arg=notrack-chain | |||
|type=string | |||
|default= | |||
|desc=Adds [[M:IP/Firewall/Raw | IP/Firewall/Raw]] rules matching IPsec policy to specified chain. Use together with <var>generate-policy</var>. | |||
}} | |||
{{Mr-arg-table | |||
|arg=password | |||
|type=string | |||
|default= | |||
|desc=XAuth or EAP password. Applicable if pre-shared key with XAuth authentication method (<var>auth-method=pre-shared-key-xauth</var>) or EAP (<var>auth-method=eap</var>) is used. | |||
}} | |||
{{Mr-arg-table | |||
|arg=peer | |||
|type=string | |||
|default= | |||
|desc=Name of the [[#Peers | peer]] on which the identity applies. | |||
}} | |||
{{Mr-arg-table | |||
|arg=policy-template-group | |||
|type=none {{!}} string | |||
|default=default | |||
|desc=If <var>generate-policy</var> is enabled, traffic selectors are checked against templates from the same [[#Groups | group]]. If none of the templates match, Phase 2 SA will not be established. | |||
}} | |||
{{Mr-arg-table- | {{Mr-arg-table | ||
| | |arg=remote-certificate | ||
|desc= | |type=string | ||
|default= | |||
|desc=Name of a certificate (listed in [[M:System/Certificates | System/Certificates]]) for authenticating the remote side (validating packets; no private key required). If <var>remote-certificate</var> is not specified then received certificate from remote peer is used and checked against CA in certificate menu. Proper CA must be imported in certificate store. If <var>remote-certificate</var> and <var>match-by=certificate</var> is specified, only the specific client certificate will be matched. Applicable if digital signature authentication method (<var>auth-method=digital-signature</var>) is used. | |||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=remote-id | ||
|type= | |type=auto {{!}} fqdn {{!}} user-fqdn {{!}} key-id {{!}} ignore | ||
|desc= | |default=auto | ||
|desc=This parameter controls what ID value to expect from the remote peer. Note that all types except for <var>ignore</var> will verify remote peer's ID with received certificate. In case when the peer sends certificate name as its ID, it is checked against the certificate, else the ID is checked against Subject Alt. Name. | |||
* <var>auto</var> - accept all ID's; | |||
* <var>fqdn</var> - fully qualified domain name. Only supported in IKEv2; | |||
* <var>user fqdn</var> - a fully-qualified username string, for example, "user@domain.com". Only supported in IKEv2; | |||
* <var>key-id</var> - specific key ID for the identity. Only supported in IKEv2; | |||
* <var>ignore</var> - do not verify received ID with certificate (dangerous). | |||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=remote-key | ||
|type= | |type=string | ||
|desc= | |default= | ||
|desc=Name of the public key from [[#Keys | keys]] menu. Applicable if RSA key authentication method (<var>auth-method=rsa-key</var>) is used. | |||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=secret | ||
|type= | |type=string | ||
|desc= | |default= | ||
|desc=Secret string. If it starts with '0x', it is parsed as a hexadecimal value. Applicable if pre-shared key authentication method (<var>auth-method=pre-shared-key</var> and <var>auth-method=pre-shared-key-xauth</var>) is used. | |||
}} | }} | ||
{{Mr-arg- | {{Mr-arg-table-end | ||
|arg= | |arg=username | ||
|type= | |type=string | ||
|desc= | |default= | ||
|desc=XAuth or EAP username. Applicable if pre-shared key with XAuth authentication method (<var>auth-method=pre-shared-key-xauth</var>) or EAP (<var>auth-method=eap</var>) is used. | |||
}} | }} | ||
{{Mr-arg | |||
'''Read only properties''' | |||
| | |||
|desc= | {{Mr-arg-table-h | ||
|prop=Property | |||
|desc=Description | |||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table-end | ||
|arg= | |arg=dynamic | ||
|type=yes {{!}} no | |type=yes {{!}} no | ||
|desc=Whether | |default= | ||
|desc=Whether this is a dynamically added entry by different service (e.g L2TP). | |||
}} | }} | ||
==Profiles== | |||
Profiles defines a set of parameters that will be used for IKE negotiation during Phase 1. These parameters may be common with other peer configurations. | |||
'''Properties''' | |||
''' | |||
{{Mr-arg-table-h | {{Mr-arg-table-h | ||
| Line 1,226: | Line 1,247: | ||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=dh-group | ||
|type= | |type=modp768 {{!}} modp1024 {{!}} ec2n155 {{!}} ec2n185 {{!}} modp1536 {{!}} modp2048 {{!}} modp3072 {{!}} modp4096 {{!}} modp6144 {{!}} modp8192 {{!}} ecp256 {{!}} ecp384 {{!}} ecp521 | ||
|desc= | |default=modp1024,modp2048 | ||
|desc=[[#Diffie-Hellman Groups | Diffie-Hellman group]] (cipher strength) | |||
}} | }} | ||
== | {{Mr-arg-table | ||
|arg=dpd-interval | |||
|type=time {{!}} disable-dpd | |||
|default=2m | |||
|desc=Dead peer detection interval. If set to <var>disable-dpd</var>, dead peer detection will not be used. | |||
}} | |||
{{Mr-arg-table | |||
|arg=dpd-maximum-failures | |||
|type=integer: 1..100 | |||
|default=5 | |||
|desc=Maximum count of failures until peer is considered to be dead. Applicable if DPD is enabled. | |||
{{Mr-arg-table- | |||
| | |||
|desc= | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=enc-algorithm | ||
|type= | |type=3des {{!}} aes-128 {{!}} aes-192 {{!}} aes-256 {{!}} blowfish {{!}} camellia-128 {{!}} camellia-192 {{!}} camellia-256 {{!}} des | ||
|default= | |default=aes-128 | ||
|desc= | |desc=List of encryption algorithms that will be used by the peer. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=hash-algorithm | ||
|type= | |type=md5 {{!}} sha1 {{!}} sha256 {{!}} sha512 | ||
|default= | |default=sha1 | ||
|desc= | |desc=Hashing algorithm. SHA (Secure Hash Algorithm) is stronger, but slower. MD5 uses 128-bit key, sha1-160bit key. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=lifebytes | ||
|type= | |type=Integer: 0..4294967295 | ||
|default= | |default=0 | ||
|desc= | |desc=Phase 1 lifebytes is used only as administrative value which is added to proposal. Used in cases if remote peer requires specific lifebytes value to establish phase 1. | ||
}} | |||
{{Mr-arg-table | |||
|arg=lifetime | |||
|type=time | |||
|default=1d | |||
|desc=Phase 1 lifetime: specifies how long the SA will be valid. | |||
}} | }} | ||
| Line 1,275: | Line 1,304: | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg= | |arg=nat-traversal | ||
|type=yes {{!}} no | |type=yes {{!}} no | ||
|default= | |default=yes | ||
|desc= | |desc=Use Linux NAT-T mechanism to solve IPsec incompatibility with NAT routers inbetween IPsec peers. This can only be used with ESP protocol (AH is not supported by design, as it signs the complete packet, including IP header, which is changed by NAT, rendering AH signature invalid). The method encapsulates IPsec ESP traffic into UDP streams in order to overcome some minor issues that made ESP incompatible with NAT. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table-end | ||
|arg= | |arg=proposal-check | ||
|type= | |type=claim {{!}} exact {{!}} obey {{!}} strict | ||
|default= | |default=obey | ||
|desc= | |desc=Phase 2 lifetime check logic: | ||
* <var>claim</var> - take shortest of proposed and configured lifetimes and notify initiator about it | |||
* <var>exact</var> - require lifetimes to be the same | |||
* <var>obey</var> - accept whatever is sent by an initiator | |||
* <var>strict</var> - if proposed lifetime is longer than the default then reject proposal otherwise accept proposed lifetime | |||
}} | }} | ||
==Active Peers== | |||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec active-peers</code></p> | |||
This menu provides various statistics about remote peers that currently have established phase 1 connection. | |||
| Line 1,317: | Line 1,335: | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=dynamic-address | ||
|type= | |type=ip/ipv6 address | ||
| | |desc=Dynamically assigned IP address by [[#Mode_configs | mode config]] | ||
| | |||
}} | }} | ||
{{ | {{Mr-arg-ro-table | ||
|arg=last-seen | |||
|type=time | |||
|desc=Duration since last message received by this peer. | |||
}} | |||
= | |||
| | |||
|desc= | |||
}} | |||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=local-address | ||
|type= | |type=ip/ipv6 address | ||
|desc= | |desc=Local address on the router used by this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=natt-peer | ||
|type=yes {{!}} no | |type=yes {{!}} no | ||
|desc=Whether | |desc=Whether NAT-T is used for this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=ph2-total | ||
|type= | |type=integer | ||
|desc= | |desc=Total amount of active IPsec security associations. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=remote-address | ||
|type= | |type=ip/ipv6 address | ||
|desc= | |desc=Remote peer's ip/ipv6 address. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=responder | ||
|type= | |type=yes {{!}} no | ||
|desc= | |desc=Whether the connection is initiated by remote peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=rx-bytes | ||
|type= | |type=integer | ||
|desc= | |desc=Total amount of bytes received from this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=rx-packets | ||
|type= | |type=integer | ||
|desc= | |desc=Total amount of packets received from this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=side | ||
|type= | |type=initiator {{!}} responder | ||
|desc= | |desc=Shows which side initiated the Phase1 negotiation. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=state | ||
|type= | |type=string | ||
|desc= | |desc=State of phase 1 negotiation with the peer. For example when phase1 and phase 2 are negotiated it will show state "established". | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=tx-bytes | ||
|type= | |type=integer | ||
|desc= | |desc=Total amount of bytes transmitted to this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table | ||
|arg= | |arg=tx-packets | ||
|type= | |type=integer | ||
|desc= | |desc=Total amount of packets transmitted to this peer. | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table-end | ||
|arg= | |arg=uptime | ||
|type= | |type=time | ||
|desc= | |desc=How long peers are in established state. | ||
}} | }} | ||
{{Mr-arg | |||
'''Commands''' | |||
| | |||
|desc= | {{Mr-arg-table-h | ||
|prop=Property | |||
|desc=Description | |||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table-end | ||
|arg= | |arg=kill-connections | ||
|type= | |type= | ||
|desc= | |desc=Manually disconnects all remote peers. | ||
}} | }} | ||
==Mode configs== | |||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec mode-config</code></p> | |||
ISAKMP and IKEv2 configuration attributes are configured in this menu. | |||
''' | '''Properties''' | ||
{{Mr-arg-table-h | {{Mr-arg-table-h | ||
| Line 1,456: | Line 1,447: | ||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=address-pool | ||
|type= | |type=none {{!}} string | ||
|desc= | |default= | ||
|desc=Name of the address pool from which responder will try to assign address if mode-config is enabled. | |||
}} | }} | ||
== | {{Mr-arg-table | ||
|arg=address-prefix-length | |||
|type=integer [1..32] | |||
|default= | |||
|desc=Prefix length (netmask) of assigned address from the pool. | |||
}} | |||
{{Mr-arg-table | |||
|arg=comment | |||
|type=string | |||
|default= | |||
|desc= | |||
{{Mr-arg-table | |||
| | |||
|desc= | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-table | ||
|arg=name | |arg=name | ||
|type=string | |type=string | ||
| Line 1,483: | Line 1,475: | ||
}} | }} | ||
{{Mr-arg-table | |||
|arg=responder | |||
|type=yes {{!}} no | |||
|default=no | |||
|desc=Specifies whether the configuration will work as an initiator (client) or responder (server). Initiator will request for mode-config parameters from responder. | |||
}} | |||
{{Mr-arg-table | |||
|arg=split-include | |||
{{Mr-arg-table- | |type=list of IP prefix | ||
| | |default= | ||
|desc= | |desc=List of subnets in CIDR format, which to tunnel. Subnets will be sent to the peer using CISCO UNITY extension, remote peer will create specific dynamic policies. | ||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=src-address-list | ||
|type= | |type=address list | ||
|desc= | |default= | ||
|desc=Specifying an address list will generate dynamic source NAT rules. This parameter is only available with <var>responder=no</var>. [[#RoadWarrior_client_with_NAT | RoadWarrior client with NAT]] | |||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table | ||
|arg= | |arg=static-dns | ||
|type= | |type=list of IP | ||
|desc= | |default= | ||
|desc=Manually specified DNS server's IP address to be sent to the client. | |||
}} | }} | ||
{{Mr-arg | {{Mr-arg-table-end | ||
|arg= | |arg=system-dns | ||
|type=yes {{!}} no | |type=yes {{!}} no | ||
|desc= | |default= | ||
|desc=When this option is enabled DNS addresses will be taken from <code>/ip dns</code>. | |||
}} | }} | ||
''' | '''Read only properties''' | ||
{{Mr-arg-table-h | {{Mr-arg-table-h | ||
| Line 1,517: | Line 1,518: | ||
}} | }} | ||
{{Mr-arg-ro-table | {{Mr-arg-ro-table-end | ||
|arg= | |arg=default | ||
|type= | |type=yes {{!}} no | ||
|desc= | |default= | ||
|desc=Whether this is a default system entry. | |||
}} | }} | ||
{{ | {{ Note | Not all IKE implementations support multiple split networks provided by split-include option. }} | ||
| | |||
{{ Note | If RouterOS client is initiator, it will always send CISCO UNITY extension, and RouterOS supports only split-include from this extension.}} | |||
| | |||
}} | {{ Note | It is not possible to use system-dns and static-dns at the same time.}} | ||
==Installed SAs== | |||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec installed-sa</code></p> | |||
This menu provides information about installed security associations including the keys. | |||
'''Read only properties''' | |||
{{Mr-arg-table-h | {{Mr-arg-table-h | ||
| Line 1,547: | Line 1,545: | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-ro-table | ||
|arg= | |arg=AH | ||
|type= | |type=yes {{!}} no | ||
|desc=Whether AH protocol is used by this SA. | |||
|desc= | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-ro-table | ||
|arg= | |arg=ESP | ||
|type= | |type=yes {{!}} no | ||
|desc=Whether ESP protocol is used by this SA. | |||
|desc= | |||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-ro-table | ||
|arg= | |arg=add-lifetime | ||
|type= | |type=time/time | ||
| | |desc=Added lifetime for the SA in format soft/hard: | ||
* soft - time period after which ike will try to establish new SA; | |||
* hard - time period after which SA is deleted. | |||
}} | }} | ||
=== | {{Mr-arg-ro-table | ||
|arg=addtime | |||
|type=time | |||
|desc=Date and time when this SA was added. | |||
}} | |||
{{Mr-arg-ro-table | |||
{{Mr-arg-table- | |arg=auth-algorithm | ||
| | |type=md5 {{!}} null {{!}} sha1 {{!}} ... | ||
|desc= | |desc=Currently used authentication algorithm. | ||
}} | }} | ||
{{Mr-arg-table | {{Mr-arg-ro-table | ||
|arg= | |arg=auth-key | ||
|type= | |type=string | ||
|desc=Used authentication key. | |||
|desc= | |||
}} | }} | ||
{{ | {{Mr-arg-ro-table | ||
|arg=current-bytes | |||
|type=64-bit integer | |||
|desc=Number of bytes seen by this SA. | |||
}} | |||
== | {{Mr-arg-ro-table | ||
|arg=dst-address | |||
|type=IP | |||
|desc=Destination address of this SA. | |||
}} | |||
=== | {{Mr-arg-ro-table | ||
|arg=enc-algorithm | |||
|type=des {{!}} 3des {{!}} aes-cbc {{!}} ... | |||
|desc=Currently used encryption algorithm. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=enc-key | |||
|type=string | |||
|desc=Used encryption key. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=enc-key-size | |||
|type=number | |||
|desc=Used encryption key length. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=expires-in | |||
|type=yes {{!}} no | |||
|desc=Time left until rekeying. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=hw-aead | |||
|type=yes {{!}} no | |||
|desc=Whether this SA is [[#Hardware_acceleration | hardware accelerated]]. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=replay | |||
|type=integer | |||
|desc=Size of replay window in bytes. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=spi | |||
|type=string | |||
|desc=Security Parameter Index identification tag | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=src-address | |||
|type=IP | |||
|desc=Source address of this SA. | |||
}} | |||
{{Mr-arg-ro-table-end | |||
|arg=state | |||
|type=string | |||
|desc=Shows the current state of the SA ("mature", "dying" etc) | |||
}} | |||
'''Commands''' | |||
{{Mr-arg-table-h | |||
|prop=Property | |||
|desc=Description | |||
}} | |||
{{Mr-arg-ro-table-end | |||
|arg=flush | |||
|type= | |||
|desc=Manually removes all installed security associations. | |||
}} | |||
== | ==Keys== | ||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec key</code></p> | |||
This menu lists all imported public andprivate keys, that can be used for peer authentication. Menu has several commands to work with keys. | |||
'''Properties''' | |||
{{Mr-arg-table-h | |||
|prop=Property | |||
|desc=Description | |||
}} | |||
{{Mr-arg-table-end | |||
|arg=name | |||
|type=string | |||
|default= | |||
|desc= | |||
}} | |||
'''Read only properties''' | |||
{{Mr-arg-table-h | |||
|prop=Property | |||
|desc=Description | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=key-size | |||
|type=1024 {{!}} 2048 {{!}} 4096 | |||
|desc=Size of this key. | |||
}} | |||
=== | {{Mr-arg-ro-table | ||
|arg=private-key | |||
|type=yes {{!}} no | |||
|desc=Whether this is a private key. | |||
}} | |||
{{Mr-arg-ro-table-end | |||
|arg=rsa | |||
|type=yes {{!}} no | |||
|desc=Whether this is a RSA key. | |||
}} | |||
'''Commands''' | |||
{{Mr-arg-table-h | |||
|prop=Property | |||
|desc=Description | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=export-pub-key | |||
|type=file-name; key | |||
|desc=Export public key to file from one of existing private keys. | |||
}} | |||
{{Mr-arg-ro-table | |||
|arg=generate-key | |||
|type=key-size; name | |||
|desc=Generate private key. Takes two parameters, name of newly generated key and key size 1024,2048 and 4096. | |||
}} | |||
=== | {{Mr-arg-ro-table-end | ||
|arg=import | |||
|type=file-name; name | |||
|desc=Import key from file. | |||
}} | |||
==Settings== | |||
<p id="shbox"><b>Sub-menu:</b> <code>/ip ipsec settings</code></p> | |||
{{Mr-arg-table-h | |||
|prop=Property | |||
|desc=Description | |||
}} | |||
{{Mr-arg-table | |||
|arg=accounting | |||
|type=yes {{!}} no | |||
|default= | |||
|desc=Whether to send RADIUS accounting requests to RADIUS server. Applicable if EAP Radius (<var>auth-method=eap-radius</var>) or pre-shared key with XAuth authentication method (<var>auth-method=pre-shared-key-xauth</var>) is used. | |||
}} | |||
{{Mr-arg-table | |||
|arg=interim-update | |||
|type=time | |||
|default= | |||
|desc=Interval between each consecutive RADIUS accounting Interim update. Accounting must be enabled. | |||
}} | |||
{{Mr-arg-table-end | |||
|arg=xauth-use-radius | |||
|type=yes {{!}} no | |||
|default= | |||
|desc=Whether to use [[Manual:RADIUS_Client | Radius client]] for XAuth users or not. | |||
}} | |||
==Application Guides== | |||
=== | ===RoadWarrior client with NAT=== | ||
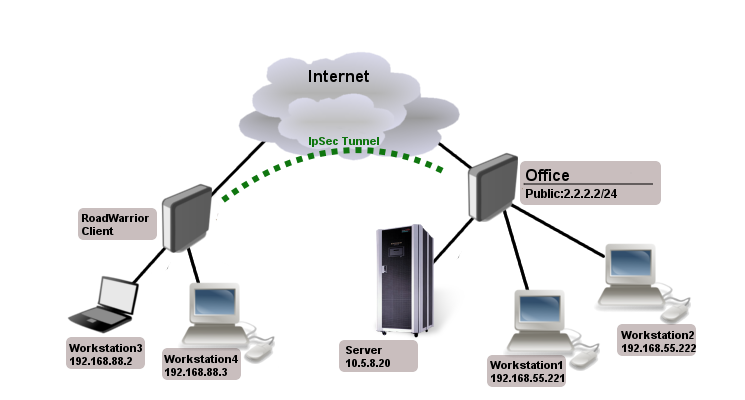
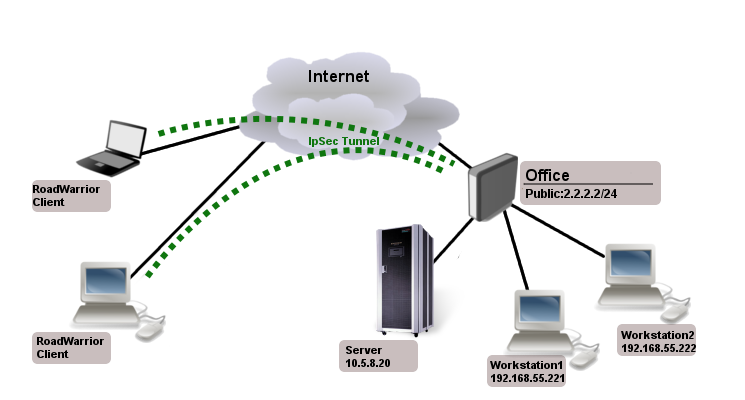
Consider setup as illustrated below. RouterOS acts as a RoadWarrior client connected to Office allowing access to its internal resources. | |||
[[file:Ipsec-road-warrior-client.png]] | |||
Tunnel is established, local mode-config IP address is received and a set of dynamic policies are generated. | |||
<pre> | <pre> | ||
[admin@pair_r1] > | [admin@pair_r1] > ip ipsec policy print | ||
Flags: X - disabled | Flags: T - template, X - disabled, D - dynamic, I - invalid, A - active, * - default | ||
0 | 0 T * group=default src-address=::/0 dst-address=::/0 protocol=all proposal=default template=yes | ||
1 | 1 DA src-address=192.168.77.254/32 src-port=any dst-address=10.5.8.0/24 dst-port=any protocol=all | ||
action=encrypt level=unique ipsec-protocols=esp tunnel=yes sa-src-address=10.155.107.8 | |||
sa-dst-address=10.155.107.9 proposal=default ph2-count=1 | |||
2 | 2 DA src-address=192.168.77.254/32 src-port=any dst-address=192.168.55.0/24 dst-port=any protocol=all | ||
action=encrypt level=unique ipsec-protocols=esp tunnel=yes sa-src-address=10.155.107.8 | |||
sa-dst-address=10.155.107.9 proposal=default ph2-count=1 | |||
</pre> | |||
Currently only packets with source address of 192.168.77.254/32 will match the IPsec policies. For local network to be able to reach remote subnets, it is necessary to change the source address of local hosts to the dynamically assigned mode config IP address. It is possible to generate source NAT rules dynamically. This can be done by creating a new address list which contains of all local networks that NAT rule should be applied. In our case, it is 192.168.88.0/24. | |||
<pre> | |||
/ip firewall address-list add address=192.168.88.0/24 list=local-RW | |||
</pre> | |||
By specifying the address list under mode-config initiator configuration, a set of source NAT rules will be dynamically generated. | |||
<pre> | <pre> | ||
/ip ipsec | /ip ipsec mode-config set [ find name="request-only" ] src-address-list=local-RW | ||
</pre> | </pre> | ||
When the IPsec tunnel is established, we can see the dynamically created source NAT rules for each network. Now every host in 192.168.88.0/24 is able to access Office's internal resources. | |||
<pre> | <pre> | ||
[admin@pair_r1] > ip firewall nat print | |||
Flags: X - disabled, I - invalid, D - dynamic | |||
0 D ;;; ipsec mode-config | |||
chain=srcnat action=src-nat to-addresses=192.168.77.254 dst-address=192.168.55.0/24 src-address-list=local-RW | |||
1 D ;;; ipsec mode-config | |||
chain=srcnat action=src-nat to-addresses=192.168.77.254 dst-address=10.5.8.0/24 src-address-list=local-RW | |||
</pre> | </pre> | ||
=== | ===Simple mutual PSK XAuth configuration=== | ||
Server side configuration: | |||
<pre> | <pre> | ||
/ip ipsec peer | |||
add address=2.2.2.1 auth-method=pre-shared-key-xauth secret="123" passive=yes | |||
/ip ipsec user | |||
add name=test password=345 | |||
</pre> | </pre> | ||
Client side configuration: | |||
<pre> | <pre> | ||
/ip ipsec peer | /ip ipsec peer | ||
add address= | add address=2.2.2.2 auth-method=pre-shared-key-xauth secret="123" \ | ||
xauth-login=test xauth-password=345 | |||
</pre> | </pre> | ||
< | {{Note | On server side it is mandatory to set <var>passive</var> to '''yes''' when XAuth is used. }} | ||
</ | |||
== | ===Allow only IPsec encapsulated traffic=== | ||
There are some scenarios where for security reasons you would like to drop access from/to specific networks if incoming/outgoing packets are not encrypted. For example, if we have L2TP/IPsec setup we would want to drop non encrypted L2TP connection attempts. | |||
There are several ways how to achieve this: | |||
* Using IPsec policy matcher in firewall; | |||
* Using generic IPsec policy with <var>action</var> set to '''drop''' and lower priority (can be used in Road Warrior setups where dynamic policies are generated); | |||
* By setting DSCP or priority in mangle and matching the same values in firewall after decapsulation. | |||
====IPsec policy matcher==== | |||
Lets set up IPsec policy matcher to accept all packets that matched any of IPsec policies and drop the rest: | |||
<pre> | <pre> | ||
add chain=input comment="ipsec policy matcher" in-interface=WAN \ | |||
add | ipsec-policy=in,ipsec | ||
add action=drop chain=input comment="drop all" in-interface=WAN log=yes | |||
</pre> | </pre> | ||
IPsec policy matcher takes two parameters '''direction,policy'''. We used incoming direction and IPsec policy. IPsec policy option allows us to inspect packets after decapsulation, so for example if we want to allow only gre encapsulated packet from specific source address and drop the rest we could set up following rules: | |||
<pre> | <pre> | ||
add chain=input comment="ipsec policy matcher" in-interface=WAN \ | |||
ipsec-policy=in,ipsec protocol=gre src=address=192.168.33.1 | |||
add action=drop chain=input comment="drop all" in-interface=WAN log=yes | |||
</pre> | </pre> | ||
For L2TP rule set would be: | |||
<pre> | <pre> | ||
add chain=input comment="ipsec policy matcher" in-interface=WAN \ | |||
ipsec-policy=in,ipsec protocol=udp dst-port=1701 | |||
add action=drop chain=input protocol=udp dst-port=1701 comment="drop l2tp" in-interface=WAN log=yes | |||
</pre> | </pre> | ||
==== | ====Using generic IPsec policy==== | ||
The trick of this method is to add default policy with action drop. Lets assume we are running L2TP/IPsec server on public 1.1.1.1 address and we want to drop all non encrypted L2TP: | |||
<pre> | <pre> | ||
/ip ipsec | /ip ipsec policy | ||
add address= | add src-address=1.1.1.1 dst-address=0.0.0.0/0 sa-src-address=1.1.1.1 \ | ||
protocol=udp src-port=1701 tunnel=yes action=discard | |||
</pre> | </pre> | ||
Now router will drop any L2TP unencrypted incoming traffic, but after successful L2TP/IPsec connection dynamic policy is created with higher priority than it is on default static rule and packets matching that dynamic rule can be forwarded. | |||
{{ Note | Policy order is important! For this to work, make sure the static drop policy is below the dynamic policies. Move it below the policy template if necessary. }} | |||
<pre> | <pre> | ||
[admin@ | [admin@rack2_10g1] /ip ipsec policy> print | ||
Flags: X - disabled, * - default | Flags: T - template, X - disabled, D - dynamic, I - inactive, * - default | ||
0 | 0 T * group=default src-address=::/0 dst-address=::/0 protocol=all | ||
proposal=default template=yes | |||
1 D src-address=1.1.1.1/32 src-port=1701 dst-address=10.5.130.71/32 | |||
dst-port=any protocol=udp action=encrypt level=require | |||
ipsec-protocols=esp tunnel=no sa-src-address=1.1.1.1 | |||
sa-dst-address=10.5.130.71 | |||
2 src-address=1.1.1.1/32 src-port=1701 dst-address=0.0.0.0/0 | |||
dst-port=any protocol=udp action=discard level=unique | |||
ipsec-protocols=esp tunnel=yes sa-src-address=1.1.1.1 | |||
sa-src-address= | sa-dst-address=0.0.0.0 proposal=default manual-sa=none | ||
</pre> | </pre> | ||
=== | ===Manually specifying local-address parameter under Peer configuration=== | ||
====Using different routing table==== | |||
IPsec, as any other service in RouterOS, uses main routing table regardless what <var>local-address</var> parameter is used for Peer configuration. It is necessary to apply routing marks to both IKE and IPSec traffic. | |||
Consider the following example. There are two default routes - one in main routing table and another in routing table "backup". It is necessary to use the backup link for IPsec site to site tunnel. | |||
<pre> | <pre> | ||
/ip | [admin@pair_r1] > /ip route print detail | ||
Flags: X - disabled, A - active, D - dynamic, C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, B - blackhole, U - unreachable, P - prohibit | |||
0 A S dst-address=0.0.0.0/0 gateway=10.155.107.1 gateway-status=10.155.107.1 reachable via ether1 distance=1 scope=30 target-scope=10 routing-mark=backup | |||
1 A S dst-address=0.0.0.0/0 gateway=172.22.2.115 gateway-status=172.22.2.115 reachable via ether2 distance=1 scope=30 target-scope=10 | |||
2 ADC dst-address=10.155.107.0/25 pref-src=10.155.107.8 gateway=ether1 gateway-status=ether1 reachable distance=0 scope=10 | |||
3 ADC dst-address=172.22.2.0/24 pref-src=172.22.2.114 gateway=ether2 gateway-status=ether2 reachable distance=0 scope=10 | |||
4 ADC dst-address=192.168.1.0/24 pref-src=192.168.1.1 gateway=bridge-local gateway-status=ether2 reachable distance=0 scope=10 | |||
[admin@pair_r1] > /ip firewall nat print | |||
Flags: X - disabled, I - invalid, D - dynamic | |||
/ip firewall | 0 chain=srcnat action=masquerade out-interface=ether1 log=no log-prefix="" | ||
1 chain=srcnat action=masquerade out-interface=ether2 log=no log-prefix="" | |||
</pre> | </pre> | ||
IPsec peer and policy configurations are created using the backup link's source address, as well as NAT bypass rule for IPsec tunnel traffic. | |||
<pre> | |||
/ip ipsec peer | |||
add address=10.155.130.136/32 local-address=10.155.107.8 secret=test | |||
/ip ipsec policy | |||
add sa-src-address=10.155.107.8 src-address=192.168.1.0/24 dst-address=172.16.0.0/24 sa-dst-address=10.155.130.136 tunnel=yes | |||
/ip firewall nat | |||
add action=accept chain=srcnat src-address=192.168.1.0/24 dst-address=172.16.0.0/24 place-before=0 | |||
</pre> | |||
Currently, we see "phase1 negotiation failed due to time up" errors in the log. It is because IPsec tries to reach the remote peer using the main routing table with incorrect source address. It is necessary to mark UDP/500, UDP/4500 and ipsec-esp packets using Mangle. | |||
<pre> | <pre> | ||
/ | /ip firewall mangle | ||
add | add action=mark-connection chain=output connection-mark=no-mark dst-address=10.155.130.136 dst-port=500,4500 \ | ||
new-connection-mark=ipsec passthrough=yes protocol=udp | |||
add | add action=mark-connection chain=output connection-mark=no-mark dst-address=10.155.130.136 new-connection-mark=ipsec \ | ||
passthrough=yes protocol=ipsec-esp | |||
add action=mark-routing chain=output connection-mark=ipsec new-routing-mark=backup passthrough=no | |||
</pre> | </pre> | ||
====Using same routing table with multiple IP addresses==== | |||
Consider the following example. There are multiple IP addresses from the same subnet on the public interface. Masquerade rule is configured on out-interface. It is necessary to use one of the IP addresses explicitly. | |||
<pre> | <pre> | ||
/ip | [admin@pair_r1] > /ip address print | ||
/ip | Flags: X - disabled, I - invalid, D - dynamic | ||
# ADDRESS NETWORK INTERFACE | |||
0 192.168.1.1/24 192.168.1.0 bridge-local | |||
1 172.22.2.1/24 172.22.2.0 ether1 | |||
/ | 2 172.22.2.2/24 172.22.2.0 ether1 | ||
3 172.22.2.3/24 172.22.2.0 ether1 | |||
[admin@pair_r1] > /ip route print | |||
Flags: X - disabled, A - active, D - dynamic, C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, B - blackhole, U - unreachable, P - prohibit | |||
# DST-ADDRESS PREF-SRC GATEWAY DISTANCE | |||
1 A S 0.0.0.0/0 172.22.2.115 1 | |||
3 ADC 172.22.2.0/24 172.22.2.1 ether1 0 | |||
4 ADC 192.168.1.0/24 192.168.1.1 bridge-local 0 | |||
[admin@pair_r1] /ip firewall nat> print | |||
Flags: X - disabled, I - invalid, D - dynamic | |||
0 chain=srcnat action=masquerade out-interface=ether1 log=no log-prefix="" | |||
</pre> | </pre> | ||
IPsec peer and policy configuration is created using one of the public IP addresses. | |||
<pre> | <pre> | ||
/ip ipsec peer | /ip ipsec peer | ||
add | add address=10.155.130.136/32 local-address=172.22.2.3 secret=test | ||
/ip ipsec policy | |||
add sa-src-address=172.22.2.3 src-address=192.168.1.0/24 dst-address=172.16.0.0/24 sa-dst-address=10.155.130.136 tunnel=yes | |||
/ip firewall nat | |||
add action=accept chain=srcnat src-address=192.168.1.0/24 dst-address=172.16.0.0/24 place-before=0 | |||
</pre> | </pre> | ||
Currently the phase 1 connection uses a different source address than we specified and "phase1 negotiation failed due to time up" errors are shown in the logs. This is because masquerade is changing the source address of the connection to match pref-src address of the connected route. Solution is to exclude connections from the public IP address from being masqueraded. | |||
<pre> | <pre> | ||
/ip | /ip firewall nat | ||
add action=accept chain=srcnat protocol=udp src-port=500,4500 place-before=0 | |||
</pre> | </pre> | ||
==Application Examples== | |||
===Site to Site IPsec tunnel=== | |||
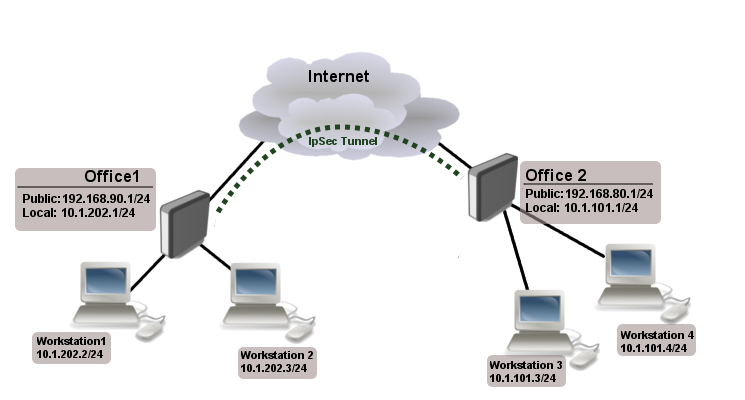
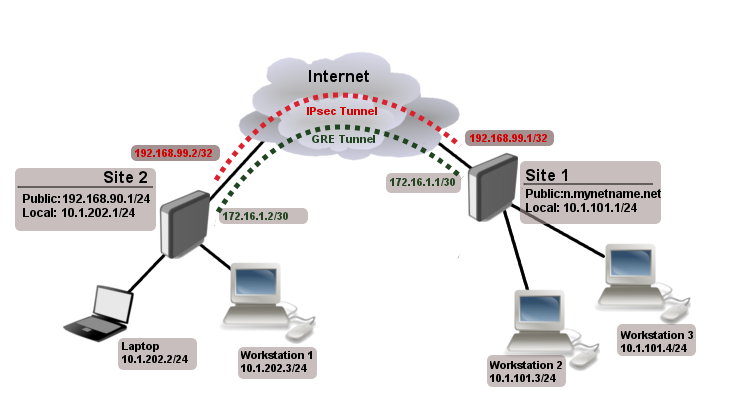
Consider setup as illustrated below. Two remote office routers are connected to internet and office workstations are behind NAT. Each office has its own local subnet, 10.1.202.0/24 for Office1 and 10.1.101.0/24 for Office2. Both remote offices needs secure tunnel to local networks behind routers. | |||
[[file:site-to-site-ipsec-example.png]] | |||
==== | ====Site 1 configuration==== | ||
Start off by creating new Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] entries using stronger or weaker encryption parameters that suits your needs. It is advised to create separate entries for each menu so that they are unique for each [[#Peers | peer]] in case it is necessary to adjust any of the settings in the future. These parameters must match between the sites or else the connection will not establish. | |||
<pre> | <pre> | ||
/ | /ip ipsec profile | ||
add | add dh-group=modp2048 enc-algorithm=aes-128 name=ike1-site2 | ||
/ip ipsec proposal | |||
add enc-algorithms=aes-128-cbc name=ike1-site2 pfs-group=modp2048 | |||
</pre> | </pre> | ||
< | Continue by configuring a [[#Peers | peer]]. Specify the <var>address</var> of the remote router. This address should be reachable through UDP/500 and UDP/4500 ports, so make sure appropriate actions are taken regarding the router's firewall. Specify the <var>name</var> for this peer as well as the newly created <var>profile</var>. | ||
<pre> | <pre> | ||
/ | /ip ipsec peer | ||
add address=192.168.80.1/32 name=ike1-site2 profile=ike1-site2 | |||
</pre> | </pre> | ||
The next step is to create an [[#Identities | identity]]. For a basic pre-shared key secured tunnel, there is nothing much to set except for a '''strong''' <var>secret</var> and the <var>peer</var> to which this identity applies. | |||
<pre> | <pre> | ||
/ | /ip ipsec identity | ||
add peer=ike1-site2 secret=thisisnotasecurepsk | |||
</pre> | </pre> | ||
{{Warning | If security matters, consider using IKEv2 and a different <var>auth-method</var>. }} | |||
Lastly, create a [[#Policies | policy]] which controls the networks/hosts between whom traffic should be encrypted. | |||
<pre> | <pre> | ||
/ | /ip ipsec policy | ||
add src-address=10.1.202.0/24 src-port=any dst-address=10.1.101.0/24 dst-port=any \ | |||
tunnel=yes action=encrypt proposal=ike1-site2 peer=ike1-site2 | |||
</pre> | </pre> | ||
====Site 2 configuration==== | |||
===== | |||
Office 2 configuration is almost identical as Office 1 with proper IP address configuration. Start off by creating new Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] entries. | |||
<pre> | <pre> | ||
/ | /ip ipsec profile | ||
add dh-group=modp2048 enc-algorithm=aes-128 name=ike1-site1 | |||
/ip ipsec proposal | |||
add enc-algorithms=aes-128-cbc name=ike1-site1 pfs-group=modp2048 | |||
</pre> | </pre> | ||
Next is the [[#Peers | peer]] and [[#Identities | identity]]. | |||
<pre> | <pre> | ||
/ | /ip ipsec peer | ||
add address=192.168.90.1/32 name=ike1-site1 profile=ike1-site1 | |||
/ip ipsec identity | |||
add peer=ike1-site1 secret=thisisnotasecurepsk | |||
</pre> | </pre> | ||
When it is done, create a [[#Policies | policy]]: | |||
<pre> | <pre> | ||
/ip ipsec | /ip ipsec policy | ||
add address= | add src-address=10.1.101.0/24 src-port=any dst-address=10.1.202.0/24 dst-port=any \ | ||
tunnel=yes action=encrypt proposal=ike1-site1 peer=ike1-site1 | |||
</pre> | </pre> | ||
At this point, the tunnel should be established and two IPsec Security Associations should be created on both routers: | |||
<pre> | <pre> | ||
/ip ipsec | /ip ipsec | ||
active-peers print | |||
installed-sa print | installed-sa print | ||
</pre> | </pre> | ||
==== | ====NAT and Fasttrack Bypass==== | ||
At this point if you try to send traffic over the IPsec tunnel, it will not work, packets will be lost. This is because both routers have NAT rules (masquerade) that is changing source address before packet is encrypted. Router is unable to encrypt the packet, because source address do not match address specified in policy configuration. For more information see [[M:Packet_Flow#IPsec_encryption | IPsec packet flow example]]. | |||
[[ | To fix this we need to set up [[M:IP/Firewall/NAT | IP/Firewall/NAT]] bypass rule. | ||
Office 1 router: | |||
<pre> | <pre> | ||
/ip firewall | /ip firewall nat | ||
add chain=srcnat action=accept place-before=0 \ | |||
src-address=10.1.202.0/24 dst-address=10.1.101.0/24 | |||
</pre> | </pre> | ||
Office 2 router: | |||
<pre> | <pre> | ||
/ip | /ip firewall nat | ||
add chain=srcnat action=accept place-before=0 \ | |||
src-address=10.1.101.0/24 dst-address=10.1.202.0/24 | |||
</pre> | </pre> | ||
{{Note | If | {{Note | If you previously tried to establish an IP connection before NAT bypass rule was added, you have to clear connection table from existing connection or restart both routers. }} | ||
It is very important that bypass rule is placed at the top of all other NAT rules. | |||
Another issue is if you have [[M:IP/Fasttrack | IP/Fasttrack]] enabled, packet bypasses IPsec policies. So we need to add accept rule before FastTrack. | |||
<pre> | <pre> | ||
/ip firewall filter | |||
add chain=forward action=accept place-before=1 | |||
src-address=10.1.101.0/24 dst-address=10.1.202.0/24 connection-state=established,related | |||
add chain=forward action=accept place-before=1 | |||
src-address=10.1.202.0/24 dst-address=10.1.101.0/24 connection-state=established,related | |||
</pre> | </pre> | ||
However, this can add significant load to router's CPU if there is a fair amount of tunnels and significant traffic on each tunnel. | |||
Solution is to use [[M:IP/Firewall/Raw | IP/Firewall/Raw]] to bypass connection tracking, that way eliminating need of filter rules listed above and reducing load on CPU by approximately 30%. | |||
<pre> | |||
/ip firewall raw | |||
add action=notrack chain=prerouting src-address=10.1.101.0/24 dst-address=10.1.202.0/24 | |||
add action=notrack chain=prerouting src-address=10.1.202.0/24 dst-address=10.1.101.0/24 | |||
</pre> | |||
===Road Warrior setup using IKEv2 with RSA authentication=== | |||
This example explains how to establish a secure IPsec connection between a device connected to the Internet (road warrior client) and a device running RouterOS acting as a server. | |||
[[ | [[file:ipsec-road-warrior.png]] | ||
====RouterOS server configuration==== | |||
Before configuring IPsec, it is required to set up certificates. It is possible to use a separate Certificate Authority for certificate management, however in this example, self signed certificates are generated in RouterOS [[Manual:System/Certificates | System/Certificates]] menu. Some certificate requirements should be met to connect various devices to the server: | |||
* Common name should contain IP or DNS name of the server; | |||
* SAN (subject alternative name) should have IP or DNS of the server; | |||
* EKU (extended key usage) tls-server and tls-client are required. | |||
Considering all requirements above, generate CA and server certificates: | |||
< | <pre> | ||
/certificate | |||
add common-name=ca name=ca | |||
sign ca ca-crl-host=2.2.2.2 | |||
add common-name=2.2.2.2 subject-alt-name=IP:2.2.2.2 key-usage=tls-server name=server1 | |||
sign server1 ca=ca | |||
</pre> | |||
</ | |||
Now that valid certificates are created on the router, add new Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] entries with <var>pfs-group=none</var>. | |||
=== | <pre> | ||
/ip ipsec profile | |||
add name=ike2 | |||
/ip ipsec proposal | |||
add name=ike2 pfs-group=none | |||
</pre> | |||
[[#Mode_configs | Mode config]] is used for address distribution from [[Manual:IP/Pools | IP/Pools]]. | |||
<pre> | |||
/ip pool | |||
add name=ike2-pool ranges=192.168.77.2-192.168.77.254 | |||
/ip ipsec mode-config | |||
add address-pool=ike2-pool address-prefix-length=32 name=ike2-conf | |||
</pre> | |||
Since that the policy template must be adjusted to allow only specific network [[#Policies | policies]], it is advised to create a separate policy [[#Groups | group]] and template. | |||
<pre> | |||
/ip ipsec policy group | |||
add name=ike2-policies | |||
/ip ipsec policy | |||
add dst-address=192.168.77.0/24 group=ike2-policies proposal=ike2 src-address=0.0.0.0/0 template=yes | |||
</pre> | |||
Create a new IPsec [[#Peers | peer]] entry which will listen to all incoming IKEv2 requests. | |||
< | <pre> | ||
/ip ipsec peer | |||
add exchange-mode=ike2 name=ike2 passive=yes profile=ike2 | |||
</pre> | |||
</ | |||
=====Identity configuration===== | |||
[[#Identities | Identity]] menu allows to match specific remote peers and assign different configuration for each one of them. First, create a default identity, that will accept all peers, but will verify the peer's identity with its certificate. | |||
<pre> | |||
/ip ipsec identity | |||
add auth-method=digital-signature certificate=server1 generate-policy=port-strict mode-config=ike2-conf peer=ike2 policy-template-group=ike2-policies | |||
</pre> | |||
{{Note | If peer's ID (ID_i) is not matching with the certificate it sends, the identity lookup will fail. See <var>remote-id</var> in [[#Identities | identities]] section. }} | |||
For example, we want to assign different [[#Mode_configs | mode config]] for user "A", who uses certificate "rw-client1" to authenticate itself to the server. First of all, make sure a new mode config is created and ready to be applied for the specific user. | |||
<pre> | |||
/ip ipsec mode-config | |||
add address=192.168.66.2 address-prefix-length=32 name=usr_A split-include=192.168.55.0/24 system-dns=no | |||
</pre> | |||
It is possible apply this configuration for user "A" by using <var>match-by=certificate</var> parameter and specifying his certificate with <var>remote-certificate</var>. | |||
<pre> | |||
/ip ipsec identity | |||
add auth-method=digital-signature certificate=server1 generate-policy=port-strict match-by=certificate mode-config=usr_A peer=ike2 policy-template-group=ike2-policies remote-certificate=rw-client1 | |||
</pre> | |||
=====Split tunnel configuration===== | |||
[[ | Split tunneling is a method which allows road warrior clients to only access a specific secured network and at the same time send the rest of the traffic based on their internal routing table (as opposed to sending all traffic over the tunnel). To configure split tunneling, changes to [[#Mode_configs | mode config]] parameters are needed. | ||
For example we will allow our road warrior clients to only access 10.5.8.0/24 network. | |||
<pre> | |||
/ip ipsec mode-conf | |||
set [find name="rw-conf"] split-include=10.5.8.0/24 | |||
</pre> | |||
< | It is also possible to send specific DNS server for the client to use. By default <var>system-dns=yes</var> is used, which sends DNS servers that are configured on the router itself in [[Manual:IP/DNS | IP/DNS]]. We can force the client to use different DNS server by using the <var>static-dns</var> parameter. | ||
<pre> | |||
/ip ipsec mode-conf | |||
set [find name="rw-conf"] system-dns=no static-dns=10.5.8.1 | |||
</pre> | |||
< | |||
</ | |||
While it is possible to adjust IPsec policy template to only allow road warrior clients to generate [[#Policies | policies]] to network configured by <var>split-include</var> parameter, this can cause compatibility issues with different vendor implementations (see [[#Known_limitations | known limitations]]). Instead of adjusting the policy template, allow access to secured network in [[Manual:IP/Firewall/Filter | IP/Firewall/Filter]] and drop everything else. | |||
< | <pre> | ||
/ip firewall filter | |||
add action=drop chain=forward src-address=192.168.77.0/24 dst-address=!10.5.8.0/24 | |||
</pre> | |||
</ | |||
{{Warning | Split networking is not a security measure. The client (initiator) can still request a different Phase 2 traffic selector. }} | |||
=====Generating client certificates===== | |||
To generate a new certificate for the client and sign it with previously created CA. | |||
=== | <pre> | ||
/certificate | |||
add common-name=rw-client1 name=rw-client1 key-usage=tls-client | |||
sign rw-client1 ca=ca | |||
</pre> | |||
<b>PKCS12 format</b> is accepted by most of client implementations, so when exporting the certificate, make sure PKCS12 is specified. | |||
<pre> | |||
/certificate | |||
export-certificate rw-client1 export-passphrase=1234567890 type=pkcs12 | |||
</pre> | |||
A file named <i>cert_export_rw-client1.p12</i> is now located in the routers [[Manual:System/File | System/File]] section. This file should be securely transported to the client device. | |||
Typically PKCS12 bundle contains also CA certificate, but some vendors may not install this CA, so self-signed CA certificate must be exported separately using PEM format. | |||
< | <pre> | ||
/certificate | |||
export-certificate ca type=pem | |||
</pre> | |||
A file named <i>cert_export_ca.crt</i> is now located in the routers [[Manual:System/File | System/File]] section. This file should also be securely transported to the client device. | |||
< | |||
<b>PEM</b> is another certificate format for use in client software that do not support PKCS12. Principle is pretty much the same. | |||
< | <pre> | ||
/certificate | |||
export-certificate ca | |||
</ | export-certificate rw-client1 export-passphrase=1234567890 | ||
</pre> | |||
< | |||
Three files are now located in the routers Files section: <i>cert_export_ca.crt</i>, <i>cert_export_rw-client1.crt</i> and <i>cert_export_rw-client1.key</i> which should be securely transported to the client device. | |||
=====Known limitations===== | |||
< | |||
Here is a list of known limitations by popular client software IKEv2 implementations. | |||
* Windows will always ignore networks received by <var>split-include</var> and request policy with destination 0.0.0.0/0 (TSr). When IPsec-SA is generated, Windows requests DHCP option 249 to which RouterOS will respond with configured <var>split-include</var> networks automatically. | |||
< | |||
* Both Apple macOS and iOS will only accept the first <var>split-include</var> network. | |||
< | |||
* Both Apple macOS and iOS will use the DNS servers from <var>system-dns</var> and <var>static-dns</var> parameters only when 0.0.0.0/0 <var>split-include</var> is used. | |||
</ | |||
= | * While some implementations can make use of different PFS group for phase 2, it is advised to use <var>pfs-group=none</var> under [[#Proposals | proposals]] to avoid any compatibility issues. | ||
==== RouterOS client configuration ==== | |||
Import a PKCS12 format certificate in RouterOS. | |||
<pre> | <pre> | ||
/certificate import file-name=cert_export_RouterOS_client.p12 passphrase=1234567890 | |||
</pre> | </pre> | ||
There should now be the self-signed CA certificate and the client certificate in Certificate menu. Find out the name of the client certificate. | |||
<pre> | <pre> | ||
/certificate print | |||
</pre> | </pre> | ||
<b>cert_export_RouterOS_client.p12_0</b> is the client certificate. | |||
It is advised to create a separate Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] configurations to not interfere with any existing IPsec configuration. | |||
<pre> | <pre> | ||
/ip ipsec profile | |||
add name=ike2-rw | |||
/ip ipsec proposal | |||
add name=ike2-rw pfs-group=none | |||
</pre> | </pre> | ||
While it is possible to use the default [[#Policies | policy]] template for policy generation, it is better to create a new policy [[#Groups | group]] and template to separate this configuration from any other IPsec configuration. | |||
<pre> | |||
/ip ipsec policy group | |||
add name=ike2-rw | |||
/ip ipsec policy | |||
add group=ike2-rw proposal=ike2-rw template=yes | |||
</pre> | |||
Create a new [[#Mode_configs | mode config]] entry with <var>responder=no</var> that will request configuration parameters from the server. | |||
<pre> | |||
/ip ipsec mode-config | |||
add name=ike2-rw responder=no | |||
</pre> | |||
[[ | Lastly, create [[#Peers | peer]] and [[#Identities | identity]] configurations. | ||
<pre> | |||
/ip ipsec peer | |||
add address=2.2.2.2/32 exchange-mode=ike2 name=ike2-rw-client | |||
/ip ipsec identity | |||
add auth-method=digital-signature certificate=cert_export_RouterOS_client.p12_0 generate-policy=port-strict mode-config=ike2-rw peer=ike2-rw-client policy-template-group=ike2-rw | |||
</pre> | |||
Verify that the connection is successfully established. | |||
<pre> | |||
/ip ipsec | |||
active-peers print | |||
installed-sa print | |||
</pre> | |||
===== Enabling dynamic source NAT rule generation ===== | |||
If we look at the generated dynamic [[#Policies | policies]], we see that only traffic with a specific (received by [[#Mode_configs | mode config]]) source address will be sent through the tunnel. But a router in most cases will need to route a specific device or network through the tunnel. In such case we can use source NAT to change the source address of packets to match the mode config address. Since the mode config address is dynamic, it is impossible to create static source NAT rule. In RouterOS it is possible to generate dynamic source NAT rules for mode config clients. | |||
[[file:Ipsec-road-warrior-client.png]] | |||
For example, we have a local network 192.168.88.0/24 behind the router and we want all traffic from this network to be sent over the tunnel. First of all, we have to make a new [[M:IP/Firewall/Address_list | IP/Firewall/Address list]] which consists of our local network. | |||
<pre> | <pre> | ||
/ip | /ip firewall address-list | ||
add | add address=192.168.88.0/24 list=local | ||
</pre> | </pre> | ||
When it is done, we can assign newly created [[M:IP/Firewall/Address_list | IP/Firewall/Address list]] to [[#Mode_configs | mode config]] configuration. | |||
<pre> | <pre> | ||
/ip ipsec mode-config | /ip ipsec mode-config | ||
set [ find name=ike2-rw ] src-address-list=local | |||
</pre> | </pre> | ||
Verify correct source NAT rule is dynamically generated when the tunnel is established. | |||
<pre> | <pre> | ||
/ip ipsec | [admin@MikroTik] > /ip firewall nat print | ||
Flags: X - disabled, I - invalid, D - dynamic | |||
0 D ;;; ipsec mode-config | |||
chain=srcnat action=src-nat to-addresses=192.168.77.254 src-address-list=local dst-address-list=!local | |||
</pre> | |||
{{Warning | Make sure dynamic [[#Mode_configs | mode config]] address is not a part of local network. }} | |||
==== Windows client configuration ==== | |||
Open PKCS12 format certificate file on the Windows computer. Install the certificate by following the instructions. Make sure you select Local Machine store location. | |||
[[File:Ike2v2_cert_win.png | 1300px]] | |||
You can now proceed to Network and Internet settings -> VPN and add a new configuration. Fill in the Connection name, Server name or address parameters. Select IKEv2 under VPN type. When it is done, it is necessary to select "Use machine certificates". This can be done in Network and Sharing Center by clicking the Properties menu for the VPN connection. The setting is located under Security tab. | |||
[[File:Ike2v2_conf_win.png | 1300px]] | |||
Currently Windows 10 is compatible with the following Phase 1 ([[#Profiles | profiles]]) and Phase 2 ([[#Proposals | proposals]]) proposal sets: | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 1</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>DH Group</th> | |||
< | </tr> | ||
/ | <tr><td>SHA1</td><td>3DES</td><td>modp1024</td></tr> | ||
<tr><td>SHA256</td><td>3DES</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>modp1024</td></tr> | |||
</ | <tr><td>SHA256</td><td>AES-128-CBC</td><td>modp1024</td></tr> | ||
<tr><td>SHA1</td><td>AES-192-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA256</td><td>AES-192-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>AES-256-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-GCM</td><td>modp1024</td></tr> | |||
<tr><td>SHA256</td><td>AES-128-GCM</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>AES-256-GCM</td><td>modp1024</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-GCM</td><td>modp1024</td></tr> | |||
</table> | |||
=== | <table class="styled_table" style="width:50%"> | ||
<tr> | |||
<th colspan=3>Phase 2</th> | |||
</tr> | |||
<tr> | |||
< | <th>Hash Algorithm</th><th>Encryption Algorithm</th><th>PFS Group</th> | ||
/ | </tr> | ||
<tr><td>SHA1</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>3DES</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>DES</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>none</td><td>none</td></tr> | |||
</table> | |||
==== macOS client configuration ==== | |||
Open PKCS12 format certificate file on the macOS computer and install the certificate in "System" keychain. It is necessary to mark the CA certificate as trusted manually since it is self-signed. Locate the certificate macOS Keychain Access app under System tab and mark it as Always Trust. | |||
[[File:Ikev2_cert_macos.png | 900px]] | |||
You can now proceed to System Preferences -> Network and add a new configuration by clicking the + button. Select Interface: VPN, VPN Type: IKEv2 and name your connection. Remote ID must be set equal to common-name or subjAltName of server's certificate. Local ID can be left blank. Under Authentication Settings select None and choose the client certificate. You can now test the connectivity. | |||
[[File:Ikev2_conf_macos.png | 900px]] | |||
==== | Currently macOS is compatible with the following Phase 1 ([[#Profiles | profiles]]) and Phase 2 ([[#Proposals | proposals]]) proposal sets: | ||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 1</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>DH Group</th> | |||
</tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>modp2048</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>ecp256</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>modp1536</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>3DES</td><td>modp1024</td></tr> | |||
</table> | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 2</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>PFS Group</th> | |||
</tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>3DES</td><td>none</td></tr> | |||
</table> | |||
=== | ==== iOS client configuration ==== | ||
Typically PKCS12 bundle contains also CA certificate, but iOS does not install this CA, so self-signed CA certificate must be installed separately using PEM format. Open these files on the iOS device and install both certificates by following the instructions. It is necessary to mark the self-signed CA certificate as trusted on the iOS device. This can be done in Settings -> General -> About -> Certificate Trust Settings menu. When it is done, check whether both certificates are marked as "verified" under Settings -> General -> Profiles menu. | |||
[[File:Ikev2_cert_ios.PNG | 900px]] | |||
<pre> | You can now proceed to Settings -> General -> VPN menu and add a new configuration. Remote ID must be set equal to common-name or subjAltName of server's certificate. Local ID can be left blank. | ||
/interface l2tp-server server | |||
set enabled=yes use-ipsec=required ipsec-secret=mySecret default-profile=default | [[File:Ikev2_conf_ios.PNG | 450px]] | ||
</pre> | |||
Currently iOS is compatible with the following Phase 1 ([[#Profiles | profiles]]) and Phase 2 ([[#Proposals | proposals]]) proposal sets: | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 1</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>DH Group</th> | |||
</tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>modp2048</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>ecp256</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>modp1536</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>modp1024</td></tr> | |||
<tr><td>SHA1</td><td>3DES</td><td>modp1024</td></tr> | |||
</table> | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 2</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>PFS Group</th> | |||
</tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>3DES</td><td>none</td></tr> | |||
</table> | |||
{{Note | If you are connected to the VPN over WiFi, the iOS device can go into sleep mode and disconnect from the network.}} | |||
==== Android (strongSwan) client configuration ==== | |||
Currently there is no IKEv2 native support in Android, however it is possible to use strongSwan from Google Play Store which brings IKEv2 to Android. StrongSwan accepts PKCS12 format certificates, so before setting up the VPN connection in strongSwan, make sure you download the PKCS12 bundle to your Android device. When it is done, create a new VPN profile in strongSwan, type in the server IP and choose "IKEv2 Certificate" as VPN Type. When selecting a User certificate, press Install and follow the certificate extract procedure by specifying the PKCS12 bundle. Save the profile and test the connection by pressing on the VPN profile. | |||
[[file:Ikev2_conf_android.png | 1080px]] | |||
It is possible to specify custom encryption settings in strongSwan by ticking the "Show advanced settings" checkbox. Currently strongSwan by default is compatible with the following Phase 1 ([[#Profiles | profiles]]) and Phase 2 ([[#Proposals | proposals]]) proposal sets: | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 1</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>DH Group</th> | |||
</tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>modp2048</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>ecp256</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>ecp384</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>ecp521</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>modp3072</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>modp4096</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>modp6144</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-CBC</td><td>modp8192</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>modp2048</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>ecp256</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>ecp384</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>ecp521</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>modp3072</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>modp4096</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>modp6144</td></tr> | |||
<tr><td>SHA*</td><td>AES-*-GCM</td><td>modp8192</td></tr> | |||
</table> | |||
<table class="styled_table" style="width:50%"> | |||
<tr> | |||
<th colspan=3>Phase 2</th> | |||
</tr> | |||
<tr> | |||
<th>Hash Algorithm</th><th>Encryption Algorithm</th><th>PFS Group</th> | |||
</tr> | |||
<tr><td>none</td><td>AES-256-GCM</td><td>none</td></tr> | |||
<tr><td>none</td><td>AES-128-GCM</td><td>none</td></tr> | |||
<tr><td>SHA256</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA512</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-256-CBC</td><td>none</td></tr> | |||
<tr><td>SHA256</td><td>AES-192-CBC</td><td>none</td></tr> | |||
<tr><td>SHA512</td><td>AES-192-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-192-CBC</td><td>none</td></tr> | |||
<tr><td>SHA256</td><td>AES-128-CBC</td><td>none</td></tr> | |||
<tr><td>SHA512</td><td>AES-128-CBC</td><td>none</td></tr> | |||
<tr><td>SHA1</td><td>AES-128-CBC</td><td>none</td></tr> | |||
</table> | |||
==== Linux (strongSwan) client configuration ==== | |||
Download the PKCS12 certificate bundle and move it to /etc/ipsec.d/private directory. | |||
Add exported passphrase for the private key to /etc/ipsec.secrets file where "strongSwan_client.p12" is the file name and "1234567890" is the passphrase. | |||
<pre> | |||
: P12 strongSwan_client.p12 "1234567890" | |||
</pre> | |||
Add a new connection to /etc/ipsec.conf file | |||
<pre> | |||
conn "ikev2" | |||
keyexchange=ikev2 | |||
ike=aes128-sha1-modp2048 | |||
esp=aes128-sha1 | |||
leftsourceip=%modeconfig | |||
leftcert=strongSwan_client.p12 | |||
leftfirewall=yes | |||
right=2.2.2.2 | |||
rightid="CN=2.2.2.2" | |||
rightsubnet=0.0.0.0/0 | |||
auto=add | |||
</pre> | |||
You can now restart (or start) the ipsec daemon and initialize the connection | |||
<pre> | |||
$ ipsec restart | |||
$ ipsec up ikev2 | |||
</pre> | |||
===Road Warrior setup with Mode Conf=== | |||
Consider setup where worker need to access other co-workers (workstations) and local office server remotely. | |||
Office has two subnets: | |||
* 192.168.55.0/24 for workstations | |||
* 192.168.66.0/24 network that must not be reachable by RoadWarrior clients | |||
* 10.5.8.0/24 for servers | |||
And access to those networks should be secure. | |||
[[file:ipsec-road-warrior.png]] | |||
Typically in RoadWarrior setups as this it is impossible to know from which address user will connect, so we need to set up <var>generate-policy</var> parameter on the server side. However this leads to other problems, client can generate any policy and access any network in the office. Even set 0.0.0.0/0 and deny internet access to office workers. | |||
'''Mode Conf''', '''policy group''' and '''policy templates''' will allow us to overcome these problems. | |||
====IPsec Server Config==== | |||
At first we need a pool from which RoadWarrior will will get an address. Typically in office you set up DHCP server for local workstations, the same DHCP pool can be used. | |||
<pre> | |||
/ip pool | |||
add name=ipsec-RW ranges=192.168.77.2-192.168.77.254 | |||
</pre> | |||
Next we need to set up what settings to send to the client using Mode Conf. | |||
<pre> | |||
/ip ipsec mode-config | |||
add address-pool=ipsec-RW name=RW-cfg split-include=\ | |||
10.5.8.0/24,192.168.55.0/24 | |||
</pre> | |||
As you can see we specified from which pool to give out address and two allowed subnets. | |||
Now to allow only specific source/destination address in generated policies we will use policy group and create policy templates: | |||
<pre> | |||
/ip ipsec policy group | |||
add name=RoadWarrior | |||
/ip ipsec policy | |||
add dst-address=192.168.77.0/24 group=RoadWarrior src-address=10.5.8.0/24 \ | |||
template=yes | |||
add dst-address=192.168.77.0/24 group=RoadWarrior src-address=192.168.55.0/24 \ | |||
template=yes | |||
</pre> | |||
Now we just add xauth users and peer with enabled Mode Conf and policy group. | |||
<pre> | |||
/ip ipsec user | |||
add name=user1 password=123 | |||
add name=user2 password=234 | |||
/ip ipsec peer | |||
add auth-method=pre-shared-key-xauth generate-policy=port-strict mode-config=RW-cfg \ | |||
policy-template-group=RoadWarrior secret=123 passive=yes | |||
</pre> | |||
==== Apple iOS (iPhone/iPad) Client ==== | |||
For iOS devices to be able to connect, '''proposal''' changes are needed: | |||
* does not work with 3des encryption algorithm, '''aes-128/256''' works | |||
* auth algorithm must be '''sha1''' | |||
* PFS group must be '''none''' | |||
* lifetime must be '''8 hours''' | |||
Example of valid proposal configuration for iOS devices: | |||
<pre> | |||
/ip ipsec proposal | |||
set default enc-algorithms=aes-128-cbc,aes-256-cbc lifetime=8h \ | |||
pfs-group=none | |||
</pre> | |||
{{ Note | Iphone does not work with split-include 0.0.0.0/0. If you set 0.0.0.0/0 for older clients traffic will not be sent over the tunnel, for newer ios clients tunnel will not be established.}} | |||
==== Android Client Notes ==== | |||
Android devices are trying to add policy with destination 0.0.0.0/0, so you have to make sure that correct policy template is added. | |||
In our case we need to add: | |||
<pre> | |||
/ip ipsec policy | |||
add group=RoadWarrior dst-address=192.168.77.0/24 src-address=0.0.0.0/0 template=yes | |||
</pre> | |||
====RouterOS Client Config==== | |||
<pre> | |||
/ip ipsec peer | |||
add address=2.2.2.2 auth-method=pre-shared-key-xauth generate-policy=port-strict secret=123 \ | |||
xauth-login=user1 xauth-password=123 mode-config=request-only | |||
</pre> | |||
====Shrew Client Config==== | |||
<pre> | |||
n:version:2 | |||
n:network-ike-port:500 | |||
n:network-mtu-size:1380 | |||
n:network-natt-port:4500 | |||
n:network-natt-rate:15 | |||
n:network-frag-size:540 | |||
n:network-dpd-enable:0 | |||
n:client-banner-enable:0 | |||
n:network-notify-enable:0 | |||
n:client-wins-used:0 | |||
n:client-wins-auto:1 | |||
n:client-dns-used:1 | |||
n:client-dns-auto:0 | |||
n:client-splitdns-used:1 | |||
n:client-splitdns-auto:0 | |||
n:phase1-dhgroup:2 | |||
n:phase1-life-secs:86400 | |||
n:phase1-life-kbytes:0 | |||
n:vendor-chkpt-enable:0 | |||
n:phase2-life-secs:300 | |||
n:phase2-life-kbytes:0 | |||
n:policy-nailed:1 | |||
n:policy-list-auto:1 | |||
n:client-addr-auto:1 | |||
s:network-host:2.2.2.2 | |||
s:client-auto-mode:pull | |||
s:client-iface:virtual | |||
s:network-natt-mode:disable | |||
s:network-frag-mode:disable | |||
s:auth-method:mutual-psk-xauth | |||
s:ident-client-type:address | |||
s:ident-server-type:address | |||
b:auth-mutual-psk:MTIz | |||
s:phase1-exchange:main | |||
s:phase1-cipher:3des | |||
s:phase1-hash:md5 | |||
s:phase2-transform:esp-3des | |||
s:phase2-hmac:sha1 | |||
s:ipcomp-transform:disabled | |||
n:phase2-pfsgroup:2 | |||
s:policy-level:require | |||
</pre> | |||
===Basic L2TP/IPsec setup=== | |||
This example demonstrates how to easily setup L2TP/IPsec server on RouterOS for road warrior connections (works with Windows, Android, iOS, macOS and other vendor L2TP/IPsec implementations). | |||
====RouterOS server configuration==== | |||
First step is to enable L2TP server: | |||
<pre> | |||
/interface l2tp-server server | |||
set enabled=yes use-ipsec=required ipsec-secret=mySecret default-profile=default | |||
</pre> | |||
<var>use-ipsec</var> is set to <b>required</b> to make sure that only IPsec encapsulated L2TP connections are accepted. | <var>use-ipsec</var> is set to <b>required</b> to make sure that only IPsec encapsulated L2TP connections are accepted. | ||
Now what it does is enables L2TP server and creates dynamic IPsec peer with specified secret. | Now what it does is enables L2TP server and creates dynamic IPsec peer with specified secret. | ||
<pre> | <pre> | ||
[admin@MikroTik] /ip ipsec peer> print | [admin@MikroTik] /ip ipsec peer> print | ||
0 D address=0.0.0.0/0 local-address=0.0.0.0 passive=yes port=500 | 0 D address=0.0.0.0/0 local-address=0.0.0.0 passive=yes port=500 | ||
auth-method=pre-shared-key secret="123" generate-policy=port-strict | auth-method=pre-shared-key secret="123" generate-policy=port-strict | ||
exchange-mode=main-l2tp send-initial-contact=yes nat-traversal=yes | exchange-mode=main-l2tp send-initial-contact=yes nat-traversal=yes | ||
hash-algorithm=sha1 enc-algorithm=3des,aes-128,aes-192,aes-256 | hash-algorithm=sha1 enc-algorithm=3des,aes-128,aes-192,aes-256 | ||
dh-group=modp1024 lifetime=1d dpd-interval=2m dpd-maximum-failures=5 | dh-group=modp1024 lifetime=1d dpd-interval=2m dpd-maximum-failures=5 | ||
</pre> | </pre> | ||
{{Note | Care must be taken if static IPsec peer configuration exists. }} | {{Note | Care must be taken if static IPsec peer configuration exists. }} | ||
Next step is to create VPN pool and add some users. | Next step is to create VPN pool and add some users. | ||
<pre> | <pre> | ||
/ip pool add name=vpn-pool range=192.168.99.2-192.168.99.100 | /ip pool add name=vpn-pool range=192.168.99.2-192.168.99.100 | ||
/ppp profile | /ppp profile | ||
set default local-address=192.168.99.1 remote-address=vpn-pool | set default local-address=192.168.99.1 remote-address=vpn-pool | ||
/ppp secret | |||
add name=user1 password=123 | |||
add name=user2 password=234 | |||
</pre> | |||
Now router is ready to accept L2TP/IPsec client connections. | |||
====RouterOS client configuration==== | |||
For RouterOS to work as L2TP/IPsec client, it is as simple as adding a new L2TP client. | |||
<pre> | |||
/interface l2tp-client | |||
add connect-to=1.1.1.1 disabled=no ipsec-secret=mySecret name=l2tp-out1 \ | |||
password=123 use-ipsec=yes user=user1 | |||
</pre> | |||
It will automatically create dynamic IPsec peer and policy configuration. | |||
===Site to Site GRE tunnel over IPsec (IKEv2) using DNS=== | |||
This example explains how it is possible to establish a secure and encrypted GRE tunnel between two RouterOS devices when one or both sites do not have a static IP address. Before making this configuration possible, it is necessary to have a DNS name assigned to one of the devices which will act as a responder (server). For simplicity, we will use RouterOS built in DDNS service [[Manual:IP/Cloud | IP/Cloud]]. | |||
[[file:Site-to-site-gre-over-ipsec-example.png]] | |||
====Site 1 (server) configuration==== | |||
This is the side that will listen to incoming connections and act as a responder. We will use [[#Mode_configs | mode config]] to provide an IP address for the second site, but first create a loopback (blank) bridge and assign an IP address to it that will be used later for GRE tunnel establishment. | |||
<pre> | |||
/interface bridge | |||
add name=loopback | |||
/ip address | |||
add address=192.168.99.1 interface=loopback | |||
</pre> | |||
Continuing with the IPsec configuration, start off by creating new Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] entries using stronger or weaker encryption parameters that suits your needs. Note that this configuration example will listen to all incoming IKEv2 requests, meaning the profile configuration will be shared between all other configurations (e.g. RoadWarrior). | |||
<pre> | |||
/ip ipsec profile | |||
add dh-group=ecp256,modp2048,modp1024 enc-algorithm=aes-256,aes-192,aes-128 name=ike2 | |||
/ip ipsec proposal | |||
add auth-algorithms=null enc-algorithms=aes-128-gcm name=ike2-gre pfs-group=none | |||
</pre> | |||
Next, create new [[#Mode_configs | mode config]] entry with <var>responder=yes</var>. This will provide an IP configuration for the other site as well as the host (loopback address) for policy generation. | |||
<pre> | |||
/ip ipsec mode-config | |||
add address=192.168.99.2 address-prefix-length=32 name=ike2-gre split-include=192.168.99.1/32 system-dns=no | |||
</pre> | |||
It is advised to create a new [[#Groups | policy group]] to separate this configuration from any existing or future IPsec configuration. | |||
<pre> | |||
/ip ipsec policy group | |||
add name=ike2-gre | |||
</pre> | |||
Now it is time to set up a new [[#Policies | policy]] template that will match the remote peers new dynamic address and the loopback address. | |||
<pre> | |||
/ip ipsec policy | |||
add dst-address=192.168.99.2/32 group=ike2-gre proposal=ike2-gre src-address=192.168.99.1/32 template=yes | |||
</pre> | |||
The next step is to create [[#Peers | peer]] configuration that will listen for all IKEv2 requests. If you already have such entry, you can skip this step. | |||
<pre> | |||
/ip ipsec peer | |||
add exchange-mode=ike2 name=ike2 passive=yes profile=ike2 | |||
</pre> | |||
Lastly, set up an [[#Identities | identity]] that will match our remote peer by pre-shared-key authentication with specific <var>secret</var>. | |||
<pre> | |||
/ip ipsec identity | |||
add generate-policy=port-strict mode-config=ike2-gre peer=ike2 policy-template-group=ike2-gre secret=test | |||
</pre> | |||
The server side is now configured and listening to all IKEv2 requests. Please make sure the firewall is not blocking UDP/4500 port. | |||
The last step is to create the GRE interface itself. This can also be done later when IPsec connection is established from the client side. | |||
<pre> | |||
/interface gre | |||
add local-address=192.168.99.1 name=gre-tunnel1 remote-address=192.168.99.2 | |||
</pre> | |||
====Site 2 (client) configuration==== | |||
Similarly to server configuration, start off by creating new Phase 1 [[#Profiles | profile]] and Phase 2 [[#Proposals | proposal]] configurations. Since this side will be the initiator, we can use more specific profile configuration to control which exact encryption parameters are used, just make sure they overlap with what is configured on the server side. | |||
<pre> | |||
/ip ipsec profile | |||
add dh-group=ecp256 enc-algorithm=aes-256 name=ike2-gre | |||
/ip ipsec proposal | |||
add auth-algorithms=null enc-algorithms=aes-128-gcm name=ike2-gre pfs-group=none | |||
</pre> | |||
Next, create new [[#Mode_configs | mode config]] entry with <var>responder=no</var>. This will make sure the peer requests IP and split-network configuration from the server. | |||
<pre> | |||
/ip ipsec mode-config | |||
add name=ike2-gre responder=no | |||
</pre> | |||
It is also advised to create a new [[#Groups | policy group]] to separate this configuration from any existing or future IPsec configuration. | |||
<pre> | |||
/ip ipsec policy group | |||
add name=ike2-gre | |||
</pre> | |||
Create a new [[#Policies | policy]] template on the client side as well. | |||
<pre> | |||
/ip ipsec policy | |||
add dst-address=192.168.99.1/32 group=ike2-gre proposal=ike2-gre src-address=192.168.99.2/32 template=yes | |||
</pre> | |||
Move on to [[#Peers | peer]] configuration. Now we can specify the DNS name for the server under <var>address</var> parameter. Obviously, you can use an IP address as well. | |||
<pre> | |||
/ip ipsec peer | |||
add address=n.mynetname.net exchange-mode=ike2 name=p1.ez profile=ike2-gre | |||
</pre> | |||
Lastly, create an [[#Identities | identity]] for our newly created peer. | |||
<pre> | |||
/ip ipsec identity | |||
add generate-policy=port-strict mode-config=ike2-gre peer=p1.ez policy-template-group=ike2-gre secret=test | |||
</pre> | |||
If everything was done properly, there should be a new dynamic policy present. | |||
<pre> | |||
/ip ipsec policy print | |||
Flags: T - template, X - disabled, D - dynamic, I - invalid, A - active, * - default | |||
0 T * group=default src-address=::/0 dst-address=::/0 protocol=all proposal=default template=yes | |||
1 T group=ike2-gre src-address=192.168.99.2/32 dst-address=192.168.99.1/32 protocol=all proposal=ike2-gre template=yes | |||
/ | 2 DA src-address=192.168.99.2/32 src-port=any dst-address=192.168.99.1/32 dst-port=any protocol=all action=encrypt level=unique ipsec-protocols=esp | ||
tunnel=yes sa-src-address=172.17.2.1 sa-dst-address=172.17.2.2 proposal=ike2-gre ph2-count=1 | |||
</pre> | </pre> | ||
A secure tunnel is now established between both sites which will encrypt all traffic between 192.168.99.2 <=> 192.168.99.1 addresses. We can use these addresses to create a GRE tunnel. | |||
= | |||
<pre> | <pre> | ||
/interface | /interface gre | ||
add | add local-address=192.168.99.2 name=gre-tunnel1 remote-address=192.168.99.1 | ||
</pre> | </pre> | ||
===IKEv2 EAP between NordVPN and RouterOS=== | |||
=== | |||
[[IKEv2_EAP_between_NordVPN_and_RouterOS | Example available here]] | |||
==Troubleshooting/FAQ== | ==Troubleshooting/FAQ== | ||
Latest revision as of 13:34, 1 April 2021

Warning: Article is migrated to our new manual: https://help.mikrotik.com/docs/display/ROS/IPsec
Summary
Sub-menu: /ip ipsec
Package required: security
Internet Protocol Security (IPsec) is a set of protocols defined by the Internet Engineering Task Force (IETF) to secure packet exchange over unprotected IP/IPv6 networks such as Internet.
IPsec protocol suite can be divided in following groups:
- Internet Key Exchange (IKE) protocols. Dynamically generates and distributes cryptographic keys for AH and ESP.
- Authentication Header (AH) RFC 4302
- Encapsulating Security Payload (ESP) RFC 4303
Internet Key Exchange Protocol (IKE)
The Internet Key Exchange (IKE) is a protocol that provides authenticated keying material for Internet Security Association and Key Management Protocol (ISAKMP) framework. There are other key exchange schemes that work with ISAKMP, but IKE is the most widely used one. Together they provide means for authentication of hosts and automatic management of security associations (SA).
Most of the time IKE daemon is doing nothing. There are two possible situations when it is activated:
There is some traffic caught by a policy rule which needs to become encrypted or authenticated, but the policy doesn't have any SAs. The policy notifies IKE daemon about that, and IKE daemon initiates connection to remote host. IKE daemon responds to remote connection. In both cases, peers establish connection and execute 2 phases:
- Phase 1 - The peers agree upon algorithms they will use in the following IKE messages and authenticate. The keying material used to derive keys for all SAs and to protect following ISAKMP exchanges between hosts is generated also. This phase should match following settings:
- authentication method
- DH group
- encryption algorithm
- exchange mode
- hash alorithm
- NAT-T
- DPD and lifetime (optional)
- Phase 2 - The peers establish one or more SAs that will be used by IPsec to encrypt data. All SAs established by IKE daemon will have lifetime values (either limiting time, after which SA will become invalid, or amount of data that can be encrypted by this SA, or both). This phase should match following settings:
- Ipsec protocol
- mode (tunnel or transport)
- authentication method
- PFS (DH) group
- lifetime

Note: There are two lifetime values - soft and hard. When SA reaches it's soft lifetime treshold, the IKE daemon receives a notice and starts another phase 2 exchange to replace this SA with fresh one. If SA reaches hard lifetime, it is discarded.

Warning: Phase 1 is not re-keyed if DPD is disabled when lifetime expires, only phase 2 is re-keyed. To force phase 1 re-key, enable DPD.

Warning: PSK authentication was known to be vulnerable against Offline attacks in "aggressive" mode, however recent discoveries indicate that offline attack is possible also in case of "main" and "ike2" exchange modes. General recommendation is to avoid using PSK authentication method.
IKE can optionally provide a Perfect Forward Secrecy (PFS), which is a property of key exchanges, that, in turn, means for IKE that compromising the long term phase 1 key will not allow to easily gain access to all IPsec data that is protected by SAs established through this phase 1. It means an additional keying material is generated for each phase 2.
Generation of keying material is computationally very expensive. Exempli gratia, the use of modp8192 group can take several seconds even on very fast computer. It usually takes place once per phase 1 exchange, which happens only once between any host pair and then is kept for long time. PFS adds this expensive operation also to each phase 2 exchange.
Diffie-Hellman Groups
Diffie-Hellman (DH) key exchange protocol allows two parties without any initial shared secret to create one securely. The following Modular Exponential (MODP) and Elliptic Curve (EC2N) Diffie-Hellman (also known as "Oakley") Groups are supported:
| Diffie-Hellman Group | Name | Reference |
|---|---|---|
| Group 1 | 768 bit MODP group | RFC 2409 |
| Group 2 | 1024 bits MODP group | RFC 2409 |
| Group 3 | EC2N group on GP(2^155) | RFC 2409 |
| Group 4 | EC2N group on GP(2^185) | RFC 2409 |
| Group 5 | 1536 bits MODP group | RFC 3526 |
| Group 14 | 2048 bits MODP group | RFC 3526 |
| Group 15 | 3072 bits MODP group | RFC 3526 |
| Group 16 | 4096 bits MODP group | RFC 3526 |
| Group 17 | 6144 bits MODP group | RFC 3526 |
| Group 18 | 8192 bits MODP group | RFC 3526 |
| Group 19 | 256 bits random ECP group | RFC 5903 |
| Group 20 | 384 bits random ECP group | RFC 5903 |
| Group 21 | 521 bits random ECP group | RFC 5903 |
More on standards can be found here.
IKE Traffic
To avoid problems with IKE packets hit some SPD rule and require to encrypt it with not yet established SA (that this packet perhaps is trying to establish), locally originated packets with UDP source port 500 are not processed with SPD. The same way packets with UDP destination port 500 that are to be delivered locally are not processed in incoming policy check.
Setup Procedure
To get IPsec to work with automatic keying using IKE-ISAKMP you will have to configure policy, peer and proposal (optional) entries.

Warning: Ipsec is very sensitive to time changes. If both ends of the IpSec tunnel are not synchronizing time equally(for example, different NTP servers not updating time with the same timestamp), tunnels will break and will have to be established again.
EAP Authentication methods
| Outer Auth | Inner Auth |
|---|---|
| EAP-GTC | |
| EAP-MD5 | |
| EAP-MSCHAPv2 | |
| EAP-PEAPv0 |
EAP-MSCHAPv2 |
| EAP-SIM | |
| EAP-TLS | |
| EAP-TTLS |
PAP |
EAP-TLS on Windows is called "Smart Card or other certificate".
Authentication Header (AH)
AH is a protocol that provides authentication of either all or part of the contents of a datagram through the addition of a header that is calculated based on the values in the datagram. What parts of the datagram are used for the calculation, and the placement of the header, depends whether tunnel or transport mode is used.
The presence of the AH header allows to verify the integrity of the message, but doesn't encrypt it. Thus, AH provides authentication but not privacy. Another protocol (ESP) is considered superior, it provides data privacy and also its own authentication method.
RouterOS supports the following authentication algorithms for AH:
- SHA2 (256, 512)
- SHA1
- MD5
Transport mode
In transport mode AH header is inserted after IP header. IP data and header is used to calculate authentication value. IP fields that might change during transit, like TTL and hop count, are set to zero values before authentication.
Tunnel mode
In tunnel mode original IP packet is encapsulated within a new IP packet. All of the original IP packet is authenticated.
Encapsulating Security Payload (ESP)
Encapsulating Security Payload (ESP) uses shared key encryption to provide data privacy. ESP also supports its own authentication scheme like that used in AH.
ESP packages its fields in a very different way than AH. Instead of having just a header, it divides its fields into three components:
- ESP Header - Comes before the encrypted data and its placement depends on whether ESP is used in transport mode or tunnel mode.
- ESP Trailer - This section is placed after the encrypted data. It contains padding that is used to align the encrypted data.
- ESP Authentication Data - This field contains an Integrity Check Value (ICV), computed in a manner similar to how the AH protocol works, for when ESP's optional authentication feature is used.
Transport mode
In transport mode ESP header is inserted after original IP header. ESP trailer and authentication value is added to the end of the packet. In this mode only IP payload is encrypted and authenticated, IP header is not secured.
Tunnel mode
In tunnel mode original IP packet is encapsulated within a new IP packet thus securing IP payload and IP header.
Encryption algorithms
RouterOS ESP supports various encryption and authentication algorithms.
Authentication:
- MD5
- SHA1
- SHA2 (256-bit, 512-bit)
Encryption:
- AES - 128-bit, 192-bit and 256-bit key AES-CBC, AES-CTR and AES-GCM algorithms;
- Blowfish - added since v4.5
- Twofish - added since v4.5
- Camellia - 128-bit, 192-bit and 256-bit key Camellia encryption algorithm added since v4.5
- DES - 56-bit DES-CBC encryption algorithm;
- 3DES - 168-bit DES encryption algorithm;
Hardware acceleration
Hardware acceleration allows to do faster encryption process by using built-in encryption engine inside CPU.
| RouterBoard | DES and 3DES | AES-CBC | AES-CTR | AES-GCM | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | MD5 | SHA1 | SHA256 | SHA512 | |
| RBcAPGi-5acD2nD (cAP ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD23UGS-5HPacD2HnD-NM (NetMetal ac²) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD25G-5HPacQD2HPnD (Audience) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD25GR-5HPacQD2HPnD&R11e-LTE6 (Audience LTE6 kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD52G-5HacD2HnD (hAP ac2) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD53GR-5HacD2HnD&R11e-LTE6 (hAP ac3 LTE6 kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBD53G-5HacD2HnD-TC&EG12-EA (Chateau LTE12) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBDiscG-5acD (DISC Lite5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLDFG-5acD (LDF 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5acD (LHG 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5HPacD2HPnD-XL (LHG XL 52 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-5acD-XL (LHG XL 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLHGG-60ad (Wireless Wire Dish) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBLtAP-2HnD (LtAP) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-LTE (LtAP LTE kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-4G (LtAP 4G kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBLtAP-2HnD&R11e-LTE6 (LtAP LTE6 kit) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBM11G **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBM33G **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RBSXTsqG-5acD (SXTsq 5 ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPG-60ad (wAP 60G) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPG-60ad-A (wAP 60G AP) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD (wAP R ac) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-LTE (wAP ac LTE kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-4G (wAP ac 4G kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RBwAPGR-5HacD2HnD&R11e-LTE6 (wAP ac LTE6 kit) * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB450Gx4 * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB750Gr3 (hEX) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RB760iGS (hEX S) **** | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no | no | no | no | no |
| RB850Gx2 ** | no | no | no | no | yes | yes | yes | yes | no | no | no | no | no | no | no | no |
| RB1100AHx2 | yes | yes | yes | no | yes | yes | yes | yes | no | no | no | no | no | no | no | no |
| RB1100AHx4 and RB1100AHx4 Dude Edition | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
| RB1200 *** | no | no | no | no | yes | yes | yes | yes | yes | yes | yes | yes | no | no | no | no |
| RB3011UiAS-RM * | no | yes | yes | no | no | yes | yes | no | no | yes | yes | no | no | no | no | no |
| RB4011iGS+RM and RB4011iGS+5HacQ2HnD-IN | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
| CCR2004-1G-12S+2XS | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
| Cloud Core Router series | yes | yes | yes | no | yes | yes | yes | no | yes | yes | yes | no | no | no | no | no |
| x86 (AES-NI) *** | no | no | no | no | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes | yes |
* supported only 128 bit and 256 bit key sizes
** only manufactured since 2016, serial numbers that begin with number 5 and 7
*** AES-CBC and AES-CTR only encryption is accelerated, hashing done in software
**** DES is not supported, only 3DES and AES-CBC
IPsec throughput results of various encryption and hash algorithm combinations are published on MikroTik products page. When testing throughput, please follow the guidelines available in the Traffic Generator manual page
Policies
Sub-menu: /ip ipsec policy
Policy table is used to determine whether security settings should be applied to a packet.
Properties
| Property | Description |
|---|---|
| action (discard | encrypt | none; Default: encrypt) | Specifies what to do with packet matched by the policy.
|
| comment (string; Default: ) | Short description of the policy. |
| disabled (yes | no; Default: no) | Whether policy is used to match packets. |
| dst-address (IP/IPv6 prefix; Default: 0.0.0.0/32) | Destination address to be matched in packets. Applicable when tunnel mode (tunnel=yes) or template (template=yes) is used. |
| dst-port (integer:0..65535 | any; Default: any) | Destination port to be matched in packets. If set to any all ports will be matched. |
| group (string; Default: default) | Name of the policy group to which this template is assigned. |
| ipsec-protocols (ah | esp; Default: esp) | Specifies what combination of Authentication Header and Encapsulating Security Payload protocols you want to apply to matched traffic. |
| level (require | unique | use; Default: require) | Specifies what to do if some of the SAs for this policy cannot be found:
|
| peer (string; Default: ) | Name of the peer on which the policy applies. |
| proposal (string; Default: default) | Name of the proposal template that will be sent by IKE daemon to establish SAs for this policy. |
| protocol (all | egp | ggp| icmp | igmp | ...; Default: all) | IP packet protocol to match. |
| src-address (ip/ipv6 prefix; Default: 0.0.0.0/32) | Source address to be matched in packets. Applicable when tunnel mode (tunnel=yes) or template (template=yes) is used. |
| src-port (any | integer:0..65535; Default: any) | Source port to be matched in packets. If set to any all ports will be matched. |
| template (yes | no; Default: no) | Creates a template and assigns it to specified policy group.
Following parameters are used by template:
|
| tunnel (yes | no; Default: no) | Specifies whether to use tunnel mode. |
Read only properties
| Property | Description |
|---|---|
| active (yes | no) | Whether this policy is currently in use. |
| default (yes | no) | Whether this is a default system entry. |
| dynamic (yes | no) | Whether this is a dynamically added or generated entry. |
| invalid (yes | no) | Whether this policy is invalid - possible cause is duplicate policy with the same src-address and dst-address. |
| ph2-count (integer) | Number of active phase 2 sessions associated with the policy. |
| ph2-state (expired | no-phase2 | established) | Indication of the progress of key establishing. |
| sa-dst-address (ip/ipv6 address; Default: ::) | SA destination IP/IPv6 address (remote peer). |
| sa-src-address (ip/ipv6 address; Default: ::) | SA source IP/IPv6 address (local peer). |

Warning: policy order is important starting form v6.40. Now it works similar as firewall filters where policies are executed from top to bottom (priority parameter is removed).

Note: All packets are IPIP encapsulated in tunnel mode, and their new IP header's src-address and dst-address are set to sa-src-address and sa-dst-address values of this policy. If you do not use tunnel mode (id est you use transport mode), then only packets whose source and destination addresses are the same as sa-src-address and sa-dst-address can be processed by this policy. Transport mode can only work with packets that originate at and are destined for IPsec peers (hosts that established security associations). To encrypt traffic between networks (or a network and a host) you have to use tunnel mode.
Statistics
Sub-menu: /ip ipsec statistics
This menu shows various IPsec statistics and errors.
Read only properties
| Property | Description |
|---|---|
| in-errors (integer) | All inbound errors that are not matched by other counters. |
| in-buffer-errors (integer) | No free buffer. |
| in-header-errors (integer) | Header error. |
| in-no-states (integer) | No state is found i.e. either inbound SPI, address, or IPsec protocol at SA is wrong. |
| in-state-protocol-errors (integer) | Transformation protocol specific error, for example SA key is wrong or hardware accelerator is unable to handle amount of packets. |
| in-state-mode-errors (integer) | Transformation mode specific error. |
| in-state-sequence-errors (integer) | Sequence number is out of window. |
| in-state-expired (integer) | State is expired. |
| in-state-mismatches (integer) | State has mismatched option, for example UDP encapsulation type is mismatched. |
| in-state-invalid (integer) | State is invalid. |
| in-template-mismatches (integer) | No matching template for states, e.g. inbound SAs are correct but SP rule is wrong. Possible cause is mismatched sa-source or sa-destination address. |
| in-no-policies (integer) | No policy is found for states, e.g. inbound SAs are correct but no SP is found. |
| in-policy-blocked (integer) | Policy discards. |
| in-policy-errors (integer) | Policy errors. |
| out-errors (integer) | All outbound errors that are not matched by other counters. |
| out-bundle-errors (integer) | Bundle generation error. |
| out-bundle-check-errors (integer) | Bundle check error. |
| out-no-states (integer) | No state is found. |
| out-state-protocol-errors (integer) | Transformation protocol specific error. |
| out-state-mode-errors (integer) | Transformation mode specific error. |
| out-state-sequence-errors (integer) | Sequence errors, for example sequence number overflow. |
| out-state-expired (integer) | State is expired. |
| out-policy-blocked (integer) | Policy discards. |
| out-policy-dead (integer) | Policy is dead. |
| out-policy-errors (integer) | Policy error. |
Proposals
Sub-menu: /ip ipsec proposal
Proposal information that will be sent by IKE daemons to establish SAs for certain policy.
Properties
| Property | Description |
|---|---|
| auth-algorithms (md5|null|sha1|sha256|sha512; Default: sha1) | Allowed algorithms for authorization. SHA (Secure Hash Algorithm) is stronger, but slower. MD5 uses 128-bit key, sha1-160bit key. |
| comment (string; Default: ) | |
| disabled (yes | no; Default: no) | Whether item is disabled. |
| enc-algorithms (null|des|3des|aes-128-cbc|aes-128-cbc|aes-128gcm|aes-192-cbc|aes-192-ctr|aes-192-gcm|aes-256-cbc|aes-256-ctr|aes-256-gcm|blowfish|camellia-128|camellia-192|camellia-256|twofish; Default: aes-256-cbc,aes-192-cbc,aes-128-cbc) | Allowed algorithms and key lengths to use for SAs. |
| lifetime (time; Default: 30m) | How long to use SA before throwing it out. |
| name (string; Default: ) | |
| pfs-group (ec2n155 | ec2n185 | ecp256 | ecp384 | ecp521 | modp768 | modp1024 | modp1536 | modp2048 | modp3072 | modp4096 | modp6144 | modp8192 | none; Default: modp1024) | Diffie-Helman group used for Perfect Forward Secrecy. |
Read only properties
| Property | Description |
|---|---|
| default (yes | no) | Whether this is a default system entry. |
Groups
Sub-menu: /ip ipsec policy group
In this menu it is possible to create additional policy groups used by policy templates.
Properties
| Property | Description |
|---|---|
| name (string; Default: ) | |
| comment (string; Default: ) |
Peers
Sub-menu: /ip ipsec peer
Peer configuration settings are used to establish connections between IKE daemons. This connection then will be used to negotiate keys and algorithms for SAs. Exchange mode is the only unique identifier between the peers, meaning that there can be multiple peer configurations with the same remote-address as long as different exchange-mode is used.
Properties
| Property | Description |
|---|---|
| address (IP/IPv6 Prefix; Default: 0.0.0.0/0) | If remote peer's address matches this prefix, then the peer configuration is used in authentication and establishment of Phase 1. If several peer's addresses match several configuration entries, the most specific one (i.e. the one with largest netmask) will be used. |
| comment (string; Default: ) | Short description of the peer. |
| disabled (yes | no; Default: no) | Whether peer is used to match remote peer's prefix. |
| exchange-mode (aggressive | base | main | ike2; Default: main) | Different ISAKMP phase 1 exchange modes according to RFC 2408. main mode relaxes rfc2409 section 5.4, to allow pre-shared-key authentication in main mode. ike2 mode enables Ikev2 RFC 7296. Parameters that are ignored by IKEv2 proposal-check, compatibility-options, lifebytes, dpd-maximum-failures, nat-traversal. |
| local-address (IP/IPv6 Address; Default: ) | Routers local address on which Phase 1 should be bounded to. |
| name (string; Default: ) | |
| passive (yes | no; Default: no) | When passive mode is enabled will wait for remote peer to initiate IKE connection. Enabled passive mode also indicates that peer is xauth responder, and disabled passive mode - xauth initiator. When passive mode is disabled peer will try to establish not only phase1, but also phase2 automatically, if policies are configured or created during phase1. |
| port (integer:0..65535; Default: 500) | Communication port used (when router is initiator) to connect to remote peer in cases if remote peer uses non-default port. |
| profile (string; Default: default) | Name of the profile template that will be used during IKE negotiation. |
| send-initial-contact (yes | no; Default: yes) | Specifies whether to send "initial contact" IKE packet or wait for remote side, this packet should trigger removal of old peer SAs for current source address. Usually in road warrior setups clients are initiators and this parameter should be set to no. Initial contact is not sent if modecfg or xauth is enabled for ikev1. |
Read only properties
| Property | Description |
|---|---|
| dynamic (yes | no) | Whether this is a dynamically added entry by different service (e.g L2TP). |
| responder (yes | no) | Whether this peer will act as a responder only (listen to incoming requests) and not initiate a connection. |
Identities
Identities are configuration parameters that are specific to the remote peer. Main purpose of an identity is to handle authentication and verify peer's integrity.
Properties
| Property | Description |
|---|---|
| auth-method (digital-signature | eap | eap-radius | pre-shared-key | pre-shared-key-xauth | rsa-key | rsa-signature-hybrid; Default: pre-shared-key) | Authentication method:
|
| certificate (string; Default: ) | Name of a certificate listed in System/Certificates (signing packets; the certificate must have private key). Applicable if digital signature authentication method (auth-method=digital-signature) or EAP (auth-method=eap) is used. |
| comment (string; Default: ) | Short description of the identity. |
| disabled (yes | no; Default: no) | Whether identity is used to match remote peer. |
| eap-methods (eap-mschapv2 | eap-peap | eap-tls | eap-ttls; Default: eap-tls) | All EAP methods requires whole certificate chain including intermediate and root CA certificates to be present in System/Certificates menu. Also username and password (if required by authentication server) must be specified. Multiple EAP methods may be specified and will be used in specified order. Currently supported EAP methods:
|
| generate-policy (no | port-override | port-strict; Default: no) | Allow this peer to establish SA for non-existing policies. Such policies are created dynamically for the lifetime of SA. Automatic policies allows, for example, to create IPsec secured L2TP tunnels, or any other setup where remote peer's IP address is not known at the configuration time.
|
| key (string; Default: ) | Name of the private key from keys menu. Applicable if RSA key authentication method (auth-method=rsa-key) is used. |
| match-by (remote-id | certificate; Default: remote-id) | Defines the logic used for peer's identity validation.
|
| mode-config (none | *request-only | string; Default: none) | Name of the configuration parameters from mode-config menu. When parameter is set mode-config is enabled. |
| my-id (auto | address | fqdn | user-fqdn | key-id; Default: auto) | On initiator, this controls what ID_i is sent to the responder. On responder, this controls what ID_r is sent to the initiator. In IKEv2, responder also expects this ID in received ID_r from initiator.
|
| notrack-chain (string; Default: ) | Adds IP/Firewall/Raw rules matching IPsec policy to specified chain. Use together with generate-policy. |
| password (string; Default: ) | XAuth or EAP password. Applicable if pre-shared key with XAuth authentication method (auth-method=pre-shared-key-xauth) or EAP (auth-method=eap) is used. |
| peer (string; Default: ) | Name of the peer on which the identity applies. |
| policy-template-group (none | string; Default: default) | If generate-policy is enabled, traffic selectors are checked against templates from the same group. If none of the templates match, Phase 2 SA will not be established. |
| remote-certificate (string; Default: ) | Name of a certificate (listed in System/Certificates) for authenticating the remote side (validating packets; no private key required). If remote-certificate is not specified then received certificate from remote peer is used and checked against CA in certificate menu. Proper CA must be imported in certificate store. If remote-certificate and match-by=certificate is specified, only the specific client certificate will be matched. Applicable if digital signature authentication method (auth-method=digital-signature) is used. |
| remote-id (auto | fqdn | user-fqdn | key-id | ignore; Default: auto) | This parameter controls what ID value to expect from the remote peer. Note that all types except for ignore will verify remote peer's ID with received certificate. In case when the peer sends certificate name as its ID, it is checked against the certificate, else the ID is checked against Subject Alt. Name.
|
| remote-key (string; Default: ) | Name of the public key from keys menu. Applicable if RSA key authentication method (auth-method=rsa-key) is used. |
| secret (string; Default: ) | Secret string. If it starts with '0x', it is parsed as a hexadecimal value. Applicable if pre-shared key authentication method (auth-method=pre-shared-key and auth-method=pre-shared-key-xauth) is used. |
| username (string; Default: ) | XAuth or EAP username. Applicable if pre-shared key with XAuth authentication method (auth-method=pre-shared-key-xauth) or EAP (auth-method=eap) is used. |
Read only properties
| Property | Description |
|---|---|
| dynamic (yes | no) | Whether this is a dynamically added entry by different service (e.g L2TP). |
Profiles
Profiles defines a set of parameters that will be used for IKE negotiation during Phase 1. These parameters may be common with other peer configurations.
Properties
| Property | Description |
|---|---|
| dh-group (modp768 | modp1024 | ec2n155 | ec2n185 | modp1536 | modp2048 | modp3072 | modp4096 | modp6144 | modp8192 | ecp256 | ecp384 | ecp521; Default: modp1024,modp2048) | Diffie-Hellman group (cipher strength) |
| dpd-interval (time | disable-dpd; Default: 2m) | Dead peer detection interval. If set to disable-dpd, dead peer detection will not be used. |
| dpd-maximum-failures (integer: 1..100; Default: 5) | Maximum count of failures until peer is considered to be dead. Applicable if DPD is enabled. |
| enc-algorithm (3des | aes-128 | aes-192 | aes-256 | blowfish | camellia-128 | camellia-192 | camellia-256 | des; Default: aes-128) | List of encryption algorithms that will be used by the peer. |
| hash-algorithm (md5 | sha1 | sha256 | sha512; Default: sha1) | Hashing algorithm. SHA (Secure Hash Algorithm) is stronger, but slower. MD5 uses 128-bit key, sha1-160bit key. |
| lifebytes (Integer: 0..4294967295; Default: 0) | Phase 1 lifebytes is used only as administrative value which is added to proposal. Used in cases if remote peer requires specific lifebytes value to establish phase 1. |
| lifetime (time; Default: 1d) | Phase 1 lifetime: specifies how long the SA will be valid. |
| name (string; Default: ) | |
| nat-traversal (yes | no; Default: yes) | Use Linux NAT-T mechanism to solve IPsec incompatibility with NAT routers inbetween IPsec peers. This can only be used with ESP protocol (AH is not supported by design, as it signs the complete packet, including IP header, which is changed by NAT, rendering AH signature invalid). The method encapsulates IPsec ESP traffic into UDP streams in order to overcome some minor issues that made ESP incompatible with NAT. |
| proposal-check (claim | exact | obey | strict; Default: obey) | Phase 2 lifetime check logic:
|
Active Peers
Sub-menu: /ip ipsec active-peers
This menu provides various statistics about remote peers that currently have established phase 1 connection.
Read only properties
| Property | Description |
|---|---|
| dynamic-address (ip/ipv6 address) | Dynamically assigned IP address by mode config |
| last-seen (time) | Duration since last message received by this peer. |
| local-address (ip/ipv6 address) | Local address on the router used by this peer. |
| natt-peer (yes | no) | Whether NAT-T is used for this peer. |
| ph2-total (integer) | Total amount of active IPsec security associations. |
| remote-address (ip/ipv6 address) | Remote peer's ip/ipv6 address. |
| responder (yes | no) | Whether the connection is initiated by remote peer. |
| rx-bytes (integer) | Total amount of bytes received from this peer. |
| rx-packets (integer) | Total amount of packets received from this peer. |
| side (initiator | responder) | Shows which side initiated the Phase1 negotiation. |
| state (string) | State of phase 1 negotiation with the peer. For example when phase1 and phase 2 are negotiated it will show state "established". |
| tx-bytes (integer) | Total amount of bytes transmitted to this peer. |
| tx-packets (integer) | Total amount of packets transmitted to this peer. |
| uptime (time) | How long peers are in established state. |
Commands
| Property | Description |
|---|---|
| kill-connections () | Manually disconnects all remote peers. |
Mode configs
Sub-menu: /ip ipsec mode-config
ISAKMP and IKEv2 configuration attributes are configured in this menu.
Properties
| Property | Description |
|---|---|
| address-pool (none | string; Default: ) | Name of the address pool from which responder will try to assign address if mode-config is enabled. |
| address-prefix-length (integer [1..32]; Default: ) | Prefix length (netmask) of assigned address from the pool. |
| comment (string; Default: ) | |
| name (string; Default: ) | |
| responder (yes | no; Default: no) | Specifies whether the configuration will work as an initiator (client) or responder (server). Initiator will request for mode-config parameters from responder. |
| split-include (list of IP prefix; Default: ) | List of subnets in CIDR format, which to tunnel. Subnets will be sent to the peer using CISCO UNITY extension, remote peer will create specific dynamic policies. |
| src-address-list (address list; Default: ) | Specifying an address list will generate dynamic source NAT rules. This parameter is only available with responder=no. RoadWarrior client with NAT |
| static-dns (list of IP; Default: ) | Manually specified DNS server's IP address to be sent to the client. |
| system-dns (yes | no; Default: ) | When this option is enabled DNS addresses will be taken from /ip dns. |
Read only properties
| Property | Description |
|---|---|
| default (yes | no) | Whether this is a default system entry. |

Note: If RouterOS client is initiator, it will always send CISCO UNITY extension, and RouterOS supports only split-include from this extension.
Installed SAs
Sub-menu: /ip ipsec installed-sa
This menu provides information about installed security associations including the keys.
Read only properties
| Property | Description |
|---|---|
| AH (yes | no) | Whether AH protocol is used by this SA. |
| ESP (yes | no) | Whether ESP protocol is used by this SA. |
| add-lifetime (time/time) | Added lifetime for the SA in format soft/hard:
|
| addtime (time) | Date and time when this SA was added. |
| auth-algorithm (md5 | null | sha1 | ...) | Currently used authentication algorithm. |
| auth-key (string) | Used authentication key. |
| current-bytes (64-bit integer) | Number of bytes seen by this SA. |
| dst-address (IP) | Destination address of this SA. |
| enc-algorithm (des | 3des | aes-cbc | ...) | Currently used encryption algorithm. |
| enc-key (string) | Used encryption key. |
| enc-key-size (number) | Used encryption key length. |
| expires-in (yes | no) | Time left until rekeying. |
| hw-aead (yes | no) | Whether this SA is hardware accelerated. |
| replay (integer) | Size of replay window in bytes. |
| spi (string) | Security Parameter Index identification tag |
| src-address (IP) | Source address of this SA. |
| state (string) | Shows the current state of the SA ("mature", "dying" etc) |
Commands
| Property | Description |
|---|---|
| flush () | Manually removes all installed security associations. |
Keys
Sub-menu: /ip ipsec key
This menu lists all imported public andprivate keys, that can be used for peer authentication. Menu has several commands to work with keys.
Properties
| Property | Description |
|---|---|
| name (string; Default: ) |
Read only properties
| Property | Description |
|---|---|
| key-size (1024 | 2048 | 4096) | Size of this key. |
| private-key (yes | no) | Whether this is a private key. |
| rsa (yes | no) | Whether this is a RSA key. |
Commands
| Property | Description |
|---|---|
| export-pub-key (file-name; key) | Export public key to file from one of existing private keys. |
| generate-key (key-size; name) | Generate private key. Takes two parameters, name of newly generated key and key size 1024,2048 and 4096. |
| import (file-name; name) | Import key from file. |
Settings
Sub-menu: /ip ipsec settings
| Property | Description |
|---|---|
| accounting (yes | no; Default: ) | Whether to send RADIUS accounting requests to RADIUS server. Applicable if EAP Radius (auth-method=eap-radius) or pre-shared key with XAuth authentication method (auth-method=pre-shared-key-xauth) is used. |
| interim-update (time; Default: ) | Interval between each consecutive RADIUS accounting Interim update. Accounting must be enabled. |
| xauth-use-radius (yes | no; Default: ) | Whether to use Radius client for XAuth users or not. |
Application Guides
RoadWarrior client with NAT
Consider setup as illustrated below. RouterOS acts as a RoadWarrior client connected to Office allowing access to its internal resources.
Tunnel is established, local mode-config IP address is received and a set of dynamic policies are generated.
[admin@pair_r1] > ip ipsec policy print
Flags: T - template, X - disabled, D - dynamic, I - invalid, A - active, * - default
0 T * group=default src-address=::/0 dst-address=::/0 protocol=all proposal=default template=yes
1 DA src-address=192.168.77.254/32 src-port=any dst-address=10.5.8.0/24 dst-port=any protocol=all
action=encrypt level=unique ipsec-protocols=esp tunnel=yes sa-src-address=10.155.107.8
sa-dst-address=10.155.107.9 proposal=default ph2-count=1
2 DA src-address=192.168.77.254/32 src-port=any dst-address=192.168.55.0/24 dst-port=any protocol=all
action=encrypt level=unique ipsec-protocols=esp tunnel=yes sa-src-address=10.155.107.8
sa-dst-address=10.155.107.9 proposal=default ph2-count=1
Currently only packets with source address of 192.168.77.254/32 will match the IPsec policies. For local network to be able to reach remote subnets, it is necessary to change the source address of local hosts to the dynamically assigned mode config IP address. It is possible to generate source NAT rules dynamically. This can be done by creating a new address list which contains of all local networks that NAT rule should be applied. In our case, it is 192.168.88.0/24.
/ip firewall address-list add address=192.168.88.0/24 list=local-RW
By specifying the address list under mode-config initiator configuration, a set of source NAT rules will be dynamically generated.
/ip ipsec mode-config set [ find name="request-only" ] src-address-list=local-RW
When the IPsec tunnel is established, we can see the dynamically created source NAT rules for each network. Now every host in 192.168.88.0/24 is able to access Office's internal resources.
[admin@pair_r1] > ip firewall nat print
Flags: X - disabled, I - invalid, D - dynamic
0 D ;;; ipsec mode-config
chain=srcnat action=src-nat to-addresses=192.168.77.254 dst-address=192.168.55.0/24 src-address-list=local-RW
1 D ;;; ipsec mode-config
chain=srcnat action=src-nat to-addresses=192.168.77.254 dst-address=10.5.8.0/24 src-address-list=local-RW
Simple mutual PSK XAuth configuration
Server side configuration:
/ip ipsec peer add address=2.2.2.1 auth-method=pre-shared-key-xauth secret="123" passive=yes /ip ipsec user add name=test password=345
Client side configuration:
/ip ipsec peer add address=2.2.2.2 auth-method=pre-shared-key-xauth secret="123" \ xauth-login=test xauth-password=345
Allow only IPsec encapsulated traffic
There are some scenarios where for security reasons you would like to drop access from/to specific networks if incoming/outgoing packets are not encrypted. For example, if we have L2TP/IPsec setup we would want to drop non encrypted L2TP connection attempts.
There are several ways how to achieve this:
- Using IPsec policy matcher in firewall;
- Using generic IPsec policy with action set to drop and lower priority (can be used in Road Warrior setups where dynamic policies are generated);
- By setting DSCP or priority in mangle and matching the same values in firewall after decapsulation.
IPsec policy matcher
Lets set up IPsec policy matcher to accept all packets that matched any of IPsec policies and drop the rest:
add chain=input comment="ipsec policy matcher" in-interface=WAN \
ipsec-policy=in,ipsec
add action=drop chain=input comment="drop all" in-interface=WAN log=yes
IPsec policy matcher takes two parameters direction,policy. We used incoming direction and IPsec policy. IPsec policy option allows us to inspect packets after decapsulation, so for example if we want to allow only gre encapsulated packet from specific source address and drop the rest we could set up following rules:
add chain=input comment="ipsec policy matcher" in-interface=WAN \
ipsec-policy=in,ipsec protocol=gre src=address=192.168.33.1
add action=drop chain=input comment="drop all" in-interface=WAN log=yes
For L2TP rule set would be:
add chain=input comment="ipsec policy matcher" in-interface=WAN \
ipsec-policy=in,ipsec protocol=udp dst-port=1701
add action=drop chain=input protocol=udp dst-port=1701 comment="drop l2tp" in-interface=WAN log=yes
Using generic IPsec policy
The trick of this method is to add default policy with action drop. Lets assume we are running L2TP/IPsec server on public 1.1.1.1 address and we want to drop all non encrypted L2TP:
/ip ipsec policy add src-address=1.1.1.1 dst-address=0.0.0.0/0 sa-src-address=1.1.1.1 \ protocol=udp src-port=1701 tunnel=yes action=discard
Now router will drop any L2TP unencrypted incoming traffic, but after successful L2TP/IPsec connection dynamic policy is created with higher priority than it is on default static rule and packets matching that dynamic rule can be forwarded.

Note: Policy order is important! For this to work, make sure the static drop policy is below the dynamic policies. Move it below the policy template if necessary.
[admin@rack2_10g1] /ip ipsec policy> print
Flags: T - template, X - disabled, D - dynamic, I - inactive, * - default
0 T * group=default src-address=::/0 dst-address=::/0 protocol=all
proposal=default template=yes
1 D src-address=1.1.1.1/32 src-port=1701 dst-address=10.5.130.71/32
dst-port=any protocol=udp action=encrypt level=require
ipsec-protocols=esp tunnel=no sa-src-address=1.1.1.1
sa-dst-address=10.5.130.71
2 src-address=1.1.1.1/32 src-port=1701 dst-address=0.0.0.0/0
dst-port=any protocol=udp action=discard level=unique
ipsec-protocols=esp tunnel=yes sa-src-address=1.1.1.1
sa-dst-address=0.0.0.0 proposal=default manual-sa=none
Manually specifying local-address parameter under Peer configuration
Using different routing table
IPsec, as any other service in RouterOS, uses main routing table regardless what local-address parameter is used for Peer configuration. It is necessary to apply routing marks to both IKE and IPSec traffic.
Consider the following example. There are two default routes - one in main routing table and another in routing table "backup". It is necessary to use the backup link for IPsec site to site tunnel.
[admin@pair_r1] > /ip route print detail Flags: X - disabled, A - active, D - dynamic, C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, B - blackhole, U - unreachable, P - prohibit 0 A S dst-address=0.0.0.0/0 gateway=10.155.107.1 gateway-status=10.155.107.1 reachable via ether1 distance=1 scope=30 target-scope=10 routing-mark=backup 1 A S dst-address=0.0.0.0/0 gateway=172.22.2.115 gateway-status=172.22.2.115 reachable via ether2 distance=1 scope=30 target-scope=10 2 ADC dst-address=10.155.107.0/25 pref-src=10.155.107.8 gateway=ether1 gateway-status=ether1 reachable distance=0 scope=10 3 ADC dst-address=172.22.2.0/24 pref-src=172.22.2.114 gateway=ether2 gateway-status=ether2 reachable distance=0 scope=10 4 ADC dst-address=192.168.1.0/24 pref-src=192.168.1.1 gateway=bridge-local gateway-status=ether2 reachable distance=0 scope=10 [admin@pair_r1] > /ip firewall nat print Flags: X - disabled, I - invalid, D - dynamic 0 chain=srcnat action=masquerade out-interface=ether1 log=no log-prefix="" 1 chain=srcnat action=masquerade out-interface=ether2 log=no log-prefix=""
IPsec peer and policy configurations are created using the backup link's source address, as well as NAT bypass rule for IPsec tunnel traffic.
/ip ipsec peer add address=10.155.130.136/32 local-address=10.155.107.8 secret=test /ip ipsec policy add sa-src-address=10.155.107.8 src-address=192.168.1.0/24 dst-address=172.16.0.0/24 sa-dst-address=10.155.130.136 tunnel=yes /ip firewall nat add action=accept chain=srcnat src-address=192.168.1.0/24 dst-address=172.16.0.0/24 place-before=0
Currently, we see "phase1 negotiation failed due to time up" errors in the log. It is because IPsec tries to reach the remote peer using the main routing table with incorrect source address. It is necessary to mark UDP/500, UDP/4500 and ipsec-esp packets using Mangle.
/ip firewall mangle add action=mark-connection chain=output connection-mark=no-mark dst-address=10.155.130.136 dst-port=500,4500 \ new-connection-mark=ipsec passthrough=yes protocol=udp add action=mark-connection chain=output connection-mark=no-mark dst-address=10.155.130.136 new-connection-mark=ipsec \ passthrough=yes protocol=ipsec-esp add action=mark-routing chain=output connection-mark=ipsec new-routing-mark=backup passthrough=no
Using same routing table with multiple IP addresses
Consider the following example. There are multiple IP addresses from the same subnet on the public interface. Masquerade rule is configured on out-interface. It is necessary to use one of the IP addresses explicitly.
[admin@pair_r1] > /ip address print Flags: X - disabled, I - invalid, D - dynamic # ADDRESS NETWORK INTERFACE 0 192.168.1.1/24 192.168.1.0 bridge-local 1 172.22.2.1/24 172.22.2.0 ether1 2 172.22.2.2/24 172.22.2.0 ether1 3 172.22.2.3/24 172.22.2.0 ether1 [admin@pair_r1] > /ip route print Flags: X - disabled, A - active, D - dynamic, C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, B - blackhole, U - unreachable, P - prohibit # DST-ADDRESS PREF-SRC GATEWAY DISTANCE 1 A S 0.0.0.0/0 172.22.2.115 1 3 ADC 172.22.2.0/24 172.22.2.1 ether1 0 4 ADC 192.168.1.0/24 192.168.1.1 bridge-local 0 [admin@pair_r1] /ip firewall nat> print Flags: X - disabled, I - invalid, D - dynamic 0 chain=srcnat action=masquerade out-interface=ether1 log=no log-prefix=""
IPsec peer and policy configuration is created using one of the public IP addresses.
/ip ipsec peer add address=10.155.130.136/32 local-address=172.22.2.3 secret=test /ip ipsec policy add sa-src-address=172.22.2.3 src-address=192.168.1.0/24 dst-address=172.16.0.0/24 sa-dst-address=10.155.130.136 tunnel=yes /ip firewall nat add action=accept chain=srcnat src-address=192.168.1.0/24 dst-address=172.16.0.0/24 place-before=0
Currently the phase 1 connection uses a different source address than we specified and "phase1 negotiation failed due to time up" errors are shown in the logs. This is because masquerade is changing the source address of the connection to match pref-src address of the connected route. Solution is to exclude connections from the public IP address from being masqueraded.
/ip firewall nat add action=accept chain=srcnat protocol=udp src-port=500,4500 place-before=0
Application Examples
Site to Site IPsec tunnel
Consider setup as illustrated below. Two remote office routers are connected to internet and office workstations are behind NAT. Each office has its own local subnet, 10.1.202.0/24 for Office1 and 10.1.101.0/24 for Office2. Both remote offices needs secure tunnel to local networks behind routers.
Site 1 configuration
Start off by creating new Phase 1 profile and Phase 2 proposal entries using stronger or weaker encryption parameters that suits your needs. It is advised to create separate entries for each menu so that they are unique for each peer in case it is necessary to adjust any of the settings in the future. These parameters must match between the sites or else the connection will not establish.
/ip ipsec profile add dh-group=modp2048 enc-algorithm=aes-128 name=ike1-site2 /ip ipsec proposal add enc-algorithms=aes-128-cbc name=ike1-site2 pfs-group=modp2048
Continue by configuring a peer. Specify the address of the remote router. This address should be reachable through UDP/500 and UDP/4500 ports, so make sure appropriate actions are taken regarding the router's firewall. Specify the name for this peer as well as the newly created profile.
/ip ipsec peer add address=192.168.80.1/32 name=ike1-site2 profile=ike1-site2
The next step is to create an identity. For a basic pre-shared key secured tunnel, there is nothing much to set except for a strong secret and the peer to which this identity applies.
/ip ipsec identity add peer=ike1-site2 secret=thisisnotasecurepsk
Lastly, create a policy which controls the networks/hosts between whom traffic should be encrypted.
/ip ipsec policy add src-address=10.1.202.0/24 src-port=any dst-address=10.1.101.0/24 dst-port=any \ tunnel=yes action=encrypt proposal=ike1-site2 peer=ike1-site2
Site 2 configuration
Office 2 configuration is almost identical as Office 1 with proper IP address configuration. Start off by creating new Phase 1 profile and Phase 2 proposal entries.
/ip ipsec profile add dh-group=modp2048 enc-algorithm=aes-128 name=ike1-site1 /ip ipsec proposal add enc-algorithms=aes-128-cbc name=ike1-site1 pfs-group=modp2048
Next is the peer and identity.
/ip ipsec peer add address=192.168.90.1/32 name=ike1-site1 profile=ike1-site1 /ip ipsec identity add peer=ike1-site1 secret=thisisnotasecurepsk
When it is done, create a policy:
/ip ipsec policy add src-address=10.1.101.0/24 src-port=any dst-address=10.1.202.0/24 dst-port=any \ tunnel=yes action=encrypt proposal=ike1-site1 peer=ike1-site1
At this point, the tunnel should be established and two IPsec Security Associations should be created on both routers:
/ip ipsec active-peers print installed-sa print
NAT and Fasttrack Bypass
At this point if you try to send traffic over the IPsec tunnel, it will not work, packets will be lost. This is because both routers have NAT rules (masquerade) that is changing source address before packet is encrypted. Router is unable to encrypt the packet, because source address do not match address specified in policy configuration. For more information see IPsec packet flow example.
To fix this we need to set up IP/Firewall/NAT bypass rule.
Office 1 router:
/ip firewall nat add chain=srcnat action=accept place-before=0 \ src-address=10.1.202.0/24 dst-address=10.1.101.0/24
Office 2 router:
/ip firewall nat add chain=srcnat action=accept place-before=0 \ src-address=10.1.101.0/24 dst-address=10.1.202.0/24

Note: If you previously tried to establish an IP connection before NAT bypass rule was added, you have to clear connection table from existing connection or restart both routers.
It is very important that bypass rule is placed at the top of all other NAT rules.
Another issue is if you have IP/Fasttrack enabled, packet bypasses IPsec policies. So we need to add accept rule before FastTrack.
/ip firewall filter add chain=forward action=accept place-before=1 src-address=10.1.101.0/24 dst-address=10.1.202.0/24 connection-state=established,related add chain=forward action=accept place-before=1 src-address=10.1.202.0/24 dst-address=10.1.101.0/24 connection-state=established,related
However, this can add significant load to router's CPU if there is a fair amount of tunnels and significant traffic on each tunnel.
Solution is to use IP/Firewall/Raw to bypass connection tracking, that way eliminating need of filter rules listed above and reducing load on CPU by approximately 30%.
/ip firewall raw add action=notrack chain=prerouting src-address=10.1.101.0/24 dst-address=10.1.202.0/24 add action=notrack chain=prerouting src-address=10.1.202.0/24 dst-address=10.1.101.0/24
Road Warrior setup using IKEv2 with RSA authentication
This example explains how to establish a secure IPsec connection between a device connected to the Internet (road warrior client) and a device running RouterOS acting as a server.
RouterOS server configuration
Before configuring IPsec, it is required to set up certificates. It is possible to use a separate Certificate Authority for certificate management, however in this example, self signed certificates are generated in RouterOS System/Certificates menu. Some certificate requirements should be met to connect various devices to the server:
- Common name should contain IP or DNS name of the server;
- SAN (subject alternative name) should have IP or DNS of the server;
- EKU (extended key usage) tls-server and tls-client are required.
Considering all requirements above, generate CA and server certificates:
/certificate add common-name=ca name=ca sign ca ca-crl-host=2.2.2.2 add common-name=2.2.2.2 subject-alt-name=IP:2.2.2.2 key-usage=tls-server name=server1 sign server1 ca=ca
Now that valid certificates are created on the router, add new Phase 1 profile and Phase 2 proposal entries with pfs-group=none.
/ip ipsec profile add name=ike2 /ip ipsec proposal add name=ike2 pfs-group=none
Mode config is used for address distribution from IP/Pools.
/ip pool add name=ike2-pool ranges=192.168.77.2-192.168.77.254 /ip ipsec mode-config add address-pool=ike2-pool address-prefix-length=32 name=ike2-conf
Since that the policy template must be adjusted to allow only specific network policies, it is advised to create a separate policy group and template.
/ip ipsec policy group add name=ike2-policies /ip ipsec policy add dst-address=192.168.77.0/24 group=ike2-policies proposal=ike2 src-address=0.0.0.0/0 template=yes
Create a new IPsec peer entry which will listen to all incoming IKEv2 requests.
/ip ipsec peer add exchange-mode=ike2 name=ike2 passive=yes profile=ike2
Identity configuration
Identity menu allows to match specific remote peers and assign different configuration for each one of them. First, create a default identity, that will accept all peers, but will verify the peer's identity with its certificate.
/ip ipsec identity add auth-method=digital-signature certificate=server1 generate-policy=port-strict mode-config=ike2-conf peer=ike2 policy-template-group=ike2-policies

Note: If peer's ID (ID_i) is not matching with the certificate it sends, the identity lookup will fail. See remote-id in identities section.
For example, we want to assign different mode config for user "A", who uses certificate "rw-client1" to authenticate itself to the server. First of all, make sure a new mode config is created and ready to be applied for the specific user.
/ip ipsec mode-config add address=192.168.66.2 address-prefix-length=32 name=usr_A split-include=192.168.55.0/24 system-dns=no
It is possible apply this configuration for user "A" by using match-by=certificate parameter and specifying his certificate with remote-certificate.
/ip ipsec identity add auth-method=digital-signature certificate=server1 generate-policy=port-strict match-by=certificate mode-config=usr_A peer=ike2 policy-template-group=ike2-policies remote-certificate=rw-client1
Split tunnel configuration
Split tunneling is a method which allows road warrior clients to only access a specific secured network and at the same time send the rest of the traffic based on their internal routing table (as opposed to sending all traffic over the tunnel). To configure split tunneling, changes to mode config parameters are needed.
For example we will allow our road warrior clients to only access 10.5.8.0/24 network.
/ip ipsec mode-conf set [find name="rw-conf"] split-include=10.5.8.0/24
It is also possible to send specific DNS server for the client to use. By default system-dns=yes is used, which sends DNS servers that are configured on the router itself in IP/DNS. We can force the client to use different DNS server by using the static-dns parameter.
/ip ipsec mode-conf set [find name="rw-conf"] system-dns=no static-dns=10.5.8.1
While it is possible to adjust IPsec policy template to only allow road warrior clients to generate policies to network configured by split-include parameter, this can cause compatibility issues with different vendor implementations (see known limitations). Instead of adjusting the policy template, allow access to secured network in IP/Firewall/Filter and drop everything else.
/ip firewall filter add action=drop chain=forward src-address=192.168.77.0/24 dst-address=!10.5.8.0/24

Warning: Split networking is not a security measure. The client (initiator) can still request a different Phase 2 traffic selector.
Generating client certificates
To generate a new certificate for the client and sign it with previously created CA.
/certificate add common-name=rw-client1 name=rw-client1 key-usage=tls-client sign rw-client1 ca=ca
PKCS12 format is accepted by most of client implementations, so when exporting the certificate, make sure PKCS12 is specified.
/certificate export-certificate rw-client1 export-passphrase=1234567890 type=pkcs12
A file named cert_export_rw-client1.p12 is now located in the routers System/File section. This file should be securely transported to the client device.
Typically PKCS12 bundle contains also CA certificate, but some vendors may not install this CA, so self-signed CA certificate must be exported separately using PEM format.
/certificate export-certificate ca type=pem
A file named cert_export_ca.crt is now located in the routers System/File section. This file should also be securely transported to the client device.
PEM is another certificate format for use in client software that do not support PKCS12. Principle is pretty much the same.
/certificate export-certificate ca export-certificate rw-client1 export-passphrase=1234567890
Three files are now located in the routers Files section: cert_export_ca.crt, cert_export_rw-client1.crt and cert_export_rw-client1.key which should be securely transported to the client device.
Known limitations
Here is a list of known limitations by popular client software IKEv2 implementations.
- Windows will always ignore networks received by split-include and request policy with destination 0.0.0.0/0 (TSr). When IPsec-SA is generated, Windows requests DHCP option 249 to which RouterOS will respond with configured split-include networks automatically.
- Both Apple macOS and iOS will only accept the first split-include network.
- Both Apple macOS and iOS will use the DNS servers from system-dns and static-dns parameters only when 0.0.0.0/0 split-include is used.
- While some implementations can make use of different PFS group for phase 2, it is advised to use pfs-group=none under proposals to avoid any compatibility issues.
RouterOS client configuration
Import a PKCS12 format certificate in RouterOS.
/certificate import file-name=cert_export_RouterOS_client.p12 passphrase=1234567890
There should now be the self-signed CA certificate and the client certificate in Certificate menu. Find out the name of the client certificate.
/certificate print
cert_export_RouterOS_client.p12_0 is the client certificate.
It is advised to create a separate Phase 1 profile and Phase 2 proposal configurations to not interfere with any existing IPsec configuration.
/ip ipsec profile add name=ike2-rw /ip ipsec proposal add name=ike2-rw pfs-group=none
While it is possible to use the default policy template for policy generation, it is better to create a new policy group and template to separate this configuration from any other IPsec configuration.
/ip ipsec policy group add name=ike2-rw /ip ipsec policy add group=ike2-rw proposal=ike2-rw template=yes
Create a new mode config entry with responder=no that will request configuration parameters from the server.
/ip ipsec mode-config add name=ike2-rw responder=no
Lastly, create peer and identity configurations.
/ip ipsec peer add address=2.2.2.2/32 exchange-mode=ike2 name=ike2-rw-client /ip ipsec identity add auth-method=digital-signature certificate=cert_export_RouterOS_client.p12_0 generate-policy=port-strict mode-config=ike2-rw peer=ike2-rw-client policy-template-group=ike2-rw
Verify that the connection is successfully established.
/ip ipsec active-peers print installed-sa print
Enabling dynamic source NAT rule generation
If we look at the generated dynamic policies, we see that only traffic with a specific (received by mode config) source address will be sent through the tunnel. But a router in most cases will need to route a specific device or network through the tunnel. In such case we can use source NAT to change the source address of packets to match the mode config address. Since the mode config address is dynamic, it is impossible to create static source NAT rule. In RouterOS it is possible to generate dynamic source NAT rules for mode config clients.
For example, we have a local network 192.168.88.0/24 behind the router and we want all traffic from this network to be sent over the tunnel. First of all, we have to make a new IP/Firewall/Address list which consists of our local network.
/ip firewall address-list add address=192.168.88.0/24 list=local
When it is done, we can assign newly created IP/Firewall/Address list to mode config configuration.
/ip ipsec mode-config set [ find name=ike2-rw ] src-address-list=local
Verify correct source NAT rule is dynamically generated when the tunnel is established.
[admin@MikroTik] > /ip firewall nat print
Flags: X - disabled, I - invalid, D - dynamic
0 D ;;; ipsec mode-config
chain=srcnat action=src-nat to-addresses=192.168.77.254 src-address-list=local dst-address-list=!local

Warning: Make sure dynamic mode config address is not a part of local network.
Windows client configuration
Open PKCS12 format certificate file on the Windows computer. Install the certificate by following the instructions. Make sure you select Local Machine store location.
You can now proceed to Network and Internet settings -> VPN and add a new configuration. Fill in the Connection name, Server name or address parameters. Select IKEv2 under VPN type. When it is done, it is necessary to select "Use machine certificates". This can be done in Network and Sharing Center by clicking the Properties menu for the VPN connection. The setting is located under Security tab.
Currently Windows 10 is compatible with the following Phase 1 ( profiles) and Phase 2 ( proposals) proposal sets:
| Phase 1 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | DH Group |
| SHA1 | 3DES | modp1024 |
| SHA256 | 3DES | modp1024 |
| SHA1 | AES-128-CBC | modp1024 |
| SHA256 | AES-128-CBC | modp1024 |
| SHA1 | AES-192-CBC | modp1024 |
| SHA256 | AES-192-CBC | modp1024 |
| SHA1 | AES-256-CBC | modp1024 |
| SHA256 | AES-256-CBC | modp1024 |
| SHA1 | AES-128-GCM | modp1024 |
| SHA256 | AES-128-GCM | modp1024 |
| SHA1 | AES-256-GCM | modp1024 |
| SHA256 | AES-256-GCM | modp1024 |
| Phase 2 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | PFS Group |
| SHA1 | AES-256-CBC | none |
| SHA1 | AES-128-CBC | none |
| SHA1 | 3DES | none |
| SHA1 | DES | none |
| SHA1 | none | none |
macOS client configuration
Open PKCS12 format certificate file on the macOS computer and install the certificate in "System" keychain. It is necessary to mark the CA certificate as trusted manually since it is self-signed. Locate the certificate macOS Keychain Access app under System tab and mark it as Always Trust.
You can now proceed to System Preferences -> Network and add a new configuration by clicking the + button. Select Interface: VPN, VPN Type: IKEv2 and name your connection. Remote ID must be set equal to common-name or subjAltName of server's certificate. Local ID can be left blank. Under Authentication Settings select None and choose the client certificate. You can now test the connectivity.
Currently macOS is compatible with the following Phase 1 ( profiles) and Phase 2 ( proposals) proposal sets:
| Phase 1 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | DH Group |
| SHA256 | AES-256-CBC | modp2048 |
| SHA256 | AES-256-CBC | ecp256 |
| SHA256 | AES-256-CBC | modp1536 |
| SHA1 | AES-128-CBC | modp1024 |
| SHA1 | 3DES | modp1024 |
| Phase 2 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | PFS Group |
| SHA256 | AES-256-CBC | none |
| SHA1 | AES-128-CBC | none |
| SHA1 | 3DES | none |
iOS client configuration
Typically PKCS12 bundle contains also CA certificate, but iOS does not install this CA, so self-signed CA certificate must be installed separately using PEM format. Open these files on the iOS device and install both certificates by following the instructions. It is necessary to mark the self-signed CA certificate as trusted on the iOS device. This can be done in Settings -> General -> About -> Certificate Trust Settings menu. When it is done, check whether both certificates are marked as "verified" under Settings -> General -> Profiles menu.
You can now proceed to Settings -> General -> VPN menu and add a new configuration. Remote ID must be set equal to common-name or subjAltName of server's certificate. Local ID can be left blank.
Currently iOS is compatible with the following Phase 1 ( profiles) and Phase 2 ( proposals) proposal sets:
| Phase 1 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | DH Group |
| SHA256 | AES-256-CBC | modp2048 |
| SHA256 | AES-256-CBC | ecp256 |
| SHA256 | AES-256-CBC | modp1536 |
| SHA1 | AES-128-CBC | modp1024 |
| SHA1 | 3DES | modp1024 |
| Phase 2 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | PFS Group |
| SHA256 | AES-256-CBC | none |
| SHA1 | AES-128-CBC | none |
| SHA1 | 3DES | none |

Note: If you are connected to the VPN over WiFi, the iOS device can go into sleep mode and disconnect from the network.
Android (strongSwan) client configuration
Currently there is no IKEv2 native support in Android, however it is possible to use strongSwan from Google Play Store which brings IKEv2 to Android. StrongSwan accepts PKCS12 format certificates, so before setting up the VPN connection in strongSwan, make sure you download the PKCS12 bundle to your Android device. When it is done, create a new VPN profile in strongSwan, type in the server IP and choose "IKEv2 Certificate" as VPN Type. When selecting a User certificate, press Install and follow the certificate extract procedure by specifying the PKCS12 bundle. Save the profile and test the connection by pressing on the VPN profile.
It is possible to specify custom encryption settings in strongSwan by ticking the "Show advanced settings" checkbox. Currently strongSwan by default is compatible with the following Phase 1 ( profiles) and Phase 2 ( proposals) proposal sets:
| Phase 1 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | DH Group |
| SHA* | AES-*-CBC | modp2048 |
| SHA* | AES-*-CBC | ecp256 |
| SHA* | AES-*-CBC | ecp384 |
| SHA* | AES-*-CBC | ecp521 |
| SHA* | AES-*-CBC | modp3072 |
| SHA* | AES-*-CBC | modp4096 |
| SHA* | AES-*-CBC | modp6144 |
| SHA* | AES-*-CBC | modp8192 |
| SHA* | AES-*-GCM | modp2048 |
| SHA* | AES-*-GCM | ecp256 |
| SHA* | AES-*-GCM | ecp384 |
| SHA* | AES-*-GCM | ecp521 |
| SHA* | AES-*-GCM | modp3072 |
| SHA* | AES-*-GCM | modp4096 |
| SHA* | AES-*-GCM | modp6144 |
| SHA* | AES-*-GCM | modp8192 |
| Phase 2 | ||
|---|---|---|
| Hash Algorithm | Encryption Algorithm | PFS Group |
| none | AES-256-GCM | none |
| none | AES-128-GCM | none |
| SHA256 | AES-256-CBC | none |
| SHA512 | AES-256-CBC | none |
| SHA1 | AES-256-CBC | none |
| SHA256 | AES-192-CBC | none |
| SHA512 | AES-192-CBC | none |
| SHA1 | AES-192-CBC | none |
| SHA256 | AES-128-CBC | none |
| SHA512 | AES-128-CBC | none |
| SHA1 | AES-128-CBC | none |
Linux (strongSwan) client configuration
Download the PKCS12 certificate bundle and move it to /etc/ipsec.d/private directory.
Add exported passphrase for the private key to /etc/ipsec.secrets file where "strongSwan_client.p12" is the file name and "1234567890" is the passphrase.
: P12 strongSwan_client.p12 "1234567890"
Add a new connection to /etc/ipsec.conf file
conn "ikev2"
keyexchange=ikev2
ike=aes128-sha1-modp2048
esp=aes128-sha1
leftsourceip=%modeconfig
leftcert=strongSwan_client.p12
leftfirewall=yes
right=2.2.2.2
rightid="CN=2.2.2.2"
rightsubnet=0.0.0.0/0
auto=add
You can now restart (or start) the ipsec daemon and initialize the connection
$ ipsec restart $ ipsec up ikev2
Road Warrior setup with Mode Conf
Consider setup where worker need to access other co-workers (workstations) and local office server remotely. Office has two subnets:
- 192.168.55.0/24 for workstations
- 192.168.66.0/24 network that must not be reachable by RoadWarrior clients
- 10.5.8.0/24 for servers
And access to those networks should be secure.
Typically in RoadWarrior setups as this it is impossible to know from which address user will connect, so we need to set up generate-policy parameter on the server side. However this leads to other problems, client can generate any policy and access any network in the office. Even set 0.0.0.0/0 and deny internet access to office workers.
Mode Conf, policy group and policy templates will allow us to overcome these problems.
IPsec Server Config
At first we need a pool from which RoadWarrior will will get an address. Typically in office you set up DHCP server for local workstations, the same DHCP pool can be used.
/ip pool add name=ipsec-RW ranges=192.168.77.2-192.168.77.254
Next we need to set up what settings to send to the client using Mode Conf.
/ip ipsec mode-config
add address-pool=ipsec-RW name=RW-cfg split-include=\
10.5.8.0/24,192.168.55.0/24
As you can see we specified from which pool to give out address and two allowed subnets.
Now to allow only specific source/destination address in generated policies we will use policy group and create policy templates:
/ip ipsec policy group
add name=RoadWarrior
/ip ipsec policy
add dst-address=192.168.77.0/24 group=RoadWarrior src-address=10.5.8.0/24 \
template=yes
add dst-address=192.168.77.0/24 group=RoadWarrior src-address=192.168.55.0/24 \
template=yes
Now we just add xauth users and peer with enabled Mode Conf and policy group.
/ip ipsec user
add name=user1 password=123
add name=user2 password=234
/ip ipsec peer
add auth-method=pre-shared-key-xauth generate-policy=port-strict mode-config=RW-cfg \
policy-template-group=RoadWarrior secret=123 passive=yes
Apple iOS (iPhone/iPad) Client
For iOS devices to be able to connect, proposal changes are needed:
- does not work with 3des encryption algorithm, aes-128/256 works
- auth algorithm must be sha1
- PFS group must be none
- lifetime must be 8 hours
Example of valid proposal configuration for iOS devices:
/ip ipsec proposal
set default enc-algorithms=aes-128-cbc,aes-256-cbc lifetime=8h \
pfs-group=none

Note: Iphone does not work with split-include 0.0.0.0/0. If you set 0.0.0.0/0 for older clients traffic will not be sent over the tunnel, for newer ios clients tunnel will not be established.
Android Client Notes
Android devices are trying to add policy with destination 0.0.0.0/0, so you have to make sure that correct policy template is added.
In our case we need to add:
/ip ipsec policy add group=RoadWarrior dst-address=192.168.77.0/24 src-address=0.0.0.0/0 template=yes
RouterOS Client Config
/ip ipsec peer
add address=2.2.2.2 auth-method=pre-shared-key-xauth generate-policy=port-strict secret=123 \
xauth-login=user1 xauth-password=123 mode-config=request-only
Shrew Client Config
n:version:2 n:network-ike-port:500 n:network-mtu-size:1380 n:network-natt-port:4500 n:network-natt-rate:15 n:network-frag-size:540 n:network-dpd-enable:0 n:client-banner-enable:0 n:network-notify-enable:0 n:client-wins-used:0 n:client-wins-auto:1 n:client-dns-used:1 n:client-dns-auto:0 n:client-splitdns-used:1 n:client-splitdns-auto:0 n:phase1-dhgroup:2 n:phase1-life-secs:86400 n:phase1-life-kbytes:0 n:vendor-chkpt-enable:0 n:phase2-life-secs:300 n:phase2-life-kbytes:0 n:policy-nailed:1 n:policy-list-auto:1 n:client-addr-auto:1 s:network-host:2.2.2.2 s:client-auto-mode:pull s:client-iface:virtual s:network-natt-mode:disable s:network-frag-mode:disable s:auth-method:mutual-psk-xauth s:ident-client-type:address s:ident-server-type:address b:auth-mutual-psk:MTIz s:phase1-exchange:main s:phase1-cipher:3des s:phase1-hash:md5 s:phase2-transform:esp-3des s:phase2-hmac:sha1 s:ipcomp-transform:disabled n:phase2-pfsgroup:2 s:policy-level:require
Basic L2TP/IPsec setup
This example demonstrates how to easily setup L2TP/IPsec server on RouterOS for road warrior connections (works with Windows, Android, iOS, macOS and other vendor L2TP/IPsec implementations).
RouterOS server configuration
First step is to enable L2TP server:
/interface l2tp-server server set enabled=yes use-ipsec=required ipsec-secret=mySecret default-profile=default
use-ipsec is set to required to make sure that only IPsec encapsulated L2TP connections are accepted.
Now what it does is enables L2TP server and creates dynamic IPsec peer with specified secret.
[admin@MikroTik] /ip ipsec peer> print
0 D address=0.0.0.0/0 local-address=0.0.0.0 passive=yes port=500
auth-method=pre-shared-key secret="123" generate-policy=port-strict
exchange-mode=main-l2tp send-initial-contact=yes nat-traversal=yes
hash-algorithm=sha1 enc-algorithm=3des,aes-128,aes-192,aes-256
dh-group=modp1024 lifetime=1d dpd-interval=2m dpd-maximum-failures=5
Next step is to create VPN pool and add some users.
/ip pool add name=vpn-pool range=192.168.99.2-192.168.99.100 /ppp profile set default local-address=192.168.99.1 remote-address=vpn-pool /ppp secret add name=user1 password=123 add name=user2 password=234
Now router is ready to accept L2TP/IPsec client connections.
RouterOS client configuration
For RouterOS to work as L2TP/IPsec client, it is as simple as adding a new L2TP client.
/interface l2tp-client
add connect-to=1.1.1.1 disabled=no ipsec-secret=mySecret name=l2tp-out1 \
password=123 use-ipsec=yes user=user1
It will automatically create dynamic IPsec peer and policy configuration.
Site to Site GRE tunnel over IPsec (IKEv2) using DNS
This example explains how it is possible to establish a secure and encrypted GRE tunnel between two RouterOS devices when one or both sites do not have a static IP address. Before making this configuration possible, it is necessary to have a DNS name assigned to one of the devices which will act as a responder (server). For simplicity, we will use RouterOS built in DDNS service IP/Cloud.
Site 1 (server) configuration
This is the side that will listen to incoming connections and act as a responder. We will use mode config to provide an IP address for the second site, but first create a loopback (blank) bridge and assign an IP address to it that will be used later for GRE tunnel establishment.
/interface bridge add name=loopback /ip address add address=192.168.99.1 interface=loopback
Continuing with the IPsec configuration, start off by creating new Phase 1 profile and Phase 2 proposal entries using stronger or weaker encryption parameters that suits your needs. Note that this configuration example will listen to all incoming IKEv2 requests, meaning the profile configuration will be shared between all other configurations (e.g. RoadWarrior).
/ip ipsec profile add dh-group=ecp256,modp2048,modp1024 enc-algorithm=aes-256,aes-192,aes-128 name=ike2 /ip ipsec proposal add auth-algorithms=null enc-algorithms=aes-128-gcm name=ike2-gre pfs-group=none
Next, create new mode config entry with responder=yes. This will provide an IP configuration for the other site as well as the host (loopback address) for policy generation.
/ip ipsec mode-config add address=192.168.99.2 address-prefix-length=32 name=ike2-gre split-include=192.168.99.1/32 system-dns=no
It is advised to create a new policy group to separate this configuration from any existing or future IPsec configuration.
/ip ipsec policy group add name=ike2-gre
Now it is time to set up a new policy template that will match the remote peers new dynamic address and the loopback address.
/ip ipsec policy add dst-address=192.168.99.2/32 group=ike2-gre proposal=ike2-gre src-address=192.168.99.1/32 template=yes
The next step is to create peer configuration that will listen for all IKEv2 requests. If you already have such entry, you can skip this step.
/ip ipsec peer add exchange-mode=ike2 name=ike2 passive=yes profile=ike2
Lastly, set up an identity that will match our remote peer by pre-shared-key authentication with specific secret.
/ip ipsec identity add generate-policy=port-strict mode-config=ike2-gre peer=ike2 policy-template-group=ike2-gre secret=test
The server side is now configured and listening to all IKEv2 requests. Please make sure the firewall is not blocking UDP/4500 port.
The last step is to create the GRE interface itself. This can also be done later when IPsec connection is established from the client side.
/interface gre add local-address=192.168.99.1 name=gre-tunnel1 remote-address=192.168.99.2
Site 2 (client) configuration
Similarly to server configuration, start off by creating new Phase 1 profile and Phase 2 proposal configurations. Since this side will be the initiator, we can use more specific profile configuration to control which exact encryption parameters are used, just make sure they overlap with what is configured on the server side.
/ip ipsec profile add dh-group=ecp256 enc-algorithm=aes-256 name=ike2-gre /ip ipsec proposal add auth-algorithms=null enc-algorithms=aes-128-gcm name=ike2-gre pfs-group=none
Next, create new mode config entry with responder=no. This will make sure the peer requests IP and split-network configuration from the server.
/ip ipsec mode-config add name=ike2-gre responder=no
It is also advised to create a new policy group to separate this configuration from any existing or future IPsec configuration.
/ip ipsec policy group add name=ike2-gre
Create a new policy template on the client side as well.
/ip ipsec policy add dst-address=192.168.99.1/32 group=ike2-gre proposal=ike2-gre src-address=192.168.99.2/32 template=yes
Move on to peer configuration. Now we can specify the DNS name for the server under address parameter. Obviously, you can use an IP address as well.
/ip ipsec peer add address=n.mynetname.net exchange-mode=ike2 name=p1.ez profile=ike2-gre
Lastly, create an identity for our newly created peer.
/ip ipsec identity add generate-policy=port-strict mode-config=ike2-gre peer=p1.ez policy-template-group=ike2-gre secret=test
If everything was done properly, there should be a new dynamic policy present.
/ip ipsec policy print
Flags: T - template, X - disabled, D - dynamic, I - invalid, A - active, * - default
0 T * group=default src-address=::/0 dst-address=::/0 protocol=all proposal=default template=yes
1 T group=ike2-gre src-address=192.168.99.2/32 dst-address=192.168.99.1/32 protocol=all proposal=ike2-gre template=yes
2 DA src-address=192.168.99.2/32 src-port=any dst-address=192.168.99.1/32 dst-port=any protocol=all action=encrypt level=unique ipsec-protocols=esp
tunnel=yes sa-src-address=172.17.2.1 sa-dst-address=172.17.2.2 proposal=ike2-gre ph2-count=1
A secure tunnel is now established between both sites which will encrypt all traffic between 192.168.99.2 <=> 192.168.99.1 addresses. We can use these addresses to create a GRE tunnel.
/interface gre add local-address=192.168.99.2 name=gre-tunnel1 remote-address=192.168.99.1
IKEv2 EAP between NordVPN and RouterOS
Troubleshooting/FAQ
- Phase 1 Failed to get valid proposal
[admin@MikroTik] /log> print (..) 17:12:32 ipsec,error no suitable proposal found. 17:12:32 ipsec,error 10.5.107.112 failed to get valid proposal. 17:12:32 ipsec,error 10.5.107.112 failed to pre-process ph1 packet (side: 1, status 1). 17:12:32 ipsec,error 10.5.107.112 phase1 negotiation failed. (..)
- Peers are unable to negotiate encryption parameters causing the connection to drop. To solve this issue, enable IPSec debug logs and find out which parameters are proposed by the remote peer and adjust configuration accordingly.
[admin@MikroTik] /system logging> add topics=ipsec,!debug
[admin@MikroTik] /log> print (..) 17:21:08 ipsec rejected hashtype: DB(prop#1:trns#1):Peer(prop#1:trns#1) = MD5:SHA 17:21:08 ipsec rejected enctype: DB(prop#1:trns#2):Peer(prop#1:trns#1) = 3DES-CBC:AES-CBC 17:21:08 ipsec rejected hashtype: DB(prop#1:trns#2):Peer(prop#1:trns#1) = MD5:SHA 17:21:08 ipsec rejected enctype: DB(prop#1:trns#1):Peer(prop#1:trns#2) = AES-CBC:3DES-CBC 17:21:08 ipsec rejected hashtype: DB(prop#1:trns#1):Peer(prop#1:trns#2) = MD5:SHA 17:21:08 ipsec rejected hashtype: DB(prop#1:trns#2):Peer(prop#1:trns#2) = MD5:SHA 17:21:08 ipsec,error no suitable proposal found. 17:21:08 ipsec,error 10.5.107.112 failed to get valid proposal. 17:21:08 ipsec,error 10.5.107.112 failed to pre-process ph1 packet (side: 1, status 1). 17:21:08 ipsec,error 10.5.107.112 phase1 negotiation failed. (..)
- In this example, remote end requires SHA1 to be used as hash algorithm, but MD5 is configured on local router. Setting before the column symbol (:) is configured on the local side, parameter after the column symbol (:) is configured on the remote side.
- "phase1 negotiation failed due to time up" what does it mean?
- There are communication problems between the peers. Possible causes include - misconfigured Phase 1 IP addresses; firewall blocking UDP ports 500 and 4500; NAT between peers not properly translating IPsec negotiation packets.
- This error message can also appear when local-address parameter is not used properly. More information available here.
- Random packet drops or connections over the tunnel is very slow, enabling packet sniffer/torch fixes the problem
- Problem is that before encapsulation packets are sent to Fasttrack/FastPath, thus bypassing IPsec policy checking.
- Solution is to exclude traffic that need to be encapsulated/decaplsulated from Fasttrack, see configuration example here.
- How to enable ike2?
- For basic configuration enabling ike2 is very simple, just change exchange-mode in peer settings to ike2.
- fatal NO-PROPOSAL-CHOSEN notify messsage
- Remote peer sent notify that it cannot accept proposed algorithms, to find exact cause of the problem, look at remote peers debug logs or configuration and verify that both client and server have the same set of algorithms.
- I can ping only in one direction.
- Typical problem in such cases is strict firewall, firewall rules allow to create new connections only in one direction. Solution is to recheck firewall rules, or explicitly accept all traffic that should be encapsulated/decapsulated.
- Can I allow only encrypted traffic?
- Yes, you can, see examples here.
- I enable IKEv2 REAUTH on StrongSwan and got error 'initiator did not reauthenticate as requested'
- RouterOS does not support rfc4478, reauth must be disabled on StrongSwan.
[ Top | Back to Content ]