SwOS/CSS610: Difference between revisions
No edit summary |
|||
| (14 intermediate revisions by 2 users not shown) | |||
| Line 1: | Line 1: | ||
{{Warning|This manual is moved to https://help.mikrotik.com/docs/display/SWOS/CSS610+series+Manual}} | |||
==Summary== | ==Summary== | ||
<p> | <p> | ||
| Line 8: | Line 11: | ||
CSS610 series switches support only SwOS Lite operating system. | CSS610 series switches support only SwOS Lite operating system. | ||
The main | The main differences compared to CSS3xx series switches are: | ||
* unsupported Independent VLAN Learning; | * unsupported Independent VLAN Learning; | ||
* unsupported VLAN mode "enabled"; | * unsupported VLAN mode "enabled"; | ||
* unsupported ACL Rate limiting; | * unsupported ACL Rate limiting; | ||
* supported Port Egress Rate limiting | * supported Port Egress Rate limiting | ||
| Line 108: | Line 111: | ||
<p>Open your web browser and enter IP address of your Switch (192.168.88.1 by default) and login screen will appear.</p> | <p>Open your web browser and enter IP address of your Switch (192.168.88.1 by default) and login screen will appear.</p> | ||
[[File: | [[File:swos_login_css610.png|center|alt=Alt text|SwOS Login|frame]] | ||
<p>SwOS default <i>IP address:</i> <b>192.168.88.1</b>, <i>user name:</i> <b>admin</b> and there is no password. | <p>SwOS default <i>IP address:</i> <b>192.168.88.1</b>, <i>user name:</i> <b>admin</b> and there is no password. | ||
| Line 151: | Line 154: | ||
{{ Note | SwOS uses a simple algorithm to ensure TCP/IP communication - it just replies to the same IP and MAC address packet came from. This way there is no need for Default Gateway on the device itself.}} | {{ Note | SwOS uses a simple algorithm to ensure TCP/IP communication - it just replies to the same IP and MAC address packet came from. This way there is no need for Default Gateway on the device itself.}} | ||
[[File: | [[File:swos_system_css610.png|alt=Alt text|General Settings|center|frame]] | ||
<br/> | <br/> | ||
<table class="styled_table" > | <table class="styled_table" > | ||
| Line 204: | Line 207: | ||
===DHCP & PPPoE Snooping=== | ===DHCP & PPPoE Snooping=== | ||
[[File: | [[File:CSS610_DHCPSnooping.png|alt=Alt text|DHCP & PPPoE snooping settings|center|frame]] | ||
<br> | <br> | ||
| Line 279: | Line 282: | ||
==LAG== | ==LAG== | ||
<p>IEEE 802.3ad (LACP) compatible link aggregation is supported, as well as static link aggregation to ensure failover and load balancing based on Layer2 | <p>IEEE 802.3ad (LACP) compatible link aggregation is supported, as well as static link aggregation to ensure failover and load balancing is based only on Layer2 hashing.</p> | ||
<p>Up to 16 link aggregation groups with up to 8 ports per a group are supported.</p> | <p>Up to 16 link aggregation groups with up to 8 ports per a group are supported.</p> | ||
[[File:swos_lag_css326.png|alt=Alt text|LAG Tab|center|frame]] | [[File:swos_lag_css326.png|alt=Alt text|LAG Tab|center|frame]] | ||
| Line 320: | Line 323: | ||
==Forwarding== | ==Forwarding== | ||
<p>Forwarding Tab provides advanced forwarding options among switch ports, port locking, port mirroring, bandwidth limit and broadcast storm control features.</p> | <p>Forwarding Tab provides advanced forwarding options among switch ports, port locking, port mirroring, bandwidth limit and broadcast storm control features.</p> | ||
[[File: | [[File:swos_forw_css610.png|center|alt=Alt text|Forwarding Settings|center|frame]] | ||
<br/> | <br/> | ||
<table class="styled_table" > | <table class="styled_table" > | ||
| Line 329: | Line 332: | ||
<tr> | <tr> | ||
<td><b>Port Lock</b></td><td> | <td><b>Port Lock</b></td><td> | ||
* <code><b>Port Lock</b></code> - Enables or disables MAC address learning on this port. When option is enabled, it will restrict MAC address learning and static MAC addresses should be configured. Any received frames with unknown source MAC address will be dropped | * <code><b>Port Lock</b></code> - Enables or disables MAC address learning on this port. When the option is enabled, it will restrict MAC address learning and static MAC addresses should be configured. Any received frames with unknown source MAC address will be dropped | ||
* <code><b>Lock On First</b></code> - Allows to learn source MAC address from the first received frame, this property should be used together with <code><b>Port Lock</b></code>. Learning of the first MAC address will reset every time an interface status changes</td> | * <code><b>Lock On First</b></code> - Allows to learn source MAC address from the first received frame, this property should be used together with <code><b>Port Lock</b></code>. Learning of the first MAC address will reset every time an interface status changes</td> | ||
</tr> | </tr> | ||
| Line 340: | Line 343: | ||
<tr> | <tr> | ||
<td><b>Broadcast Storm Control</b></td><td> | <td><b>Broadcast Storm Control</b></td><td> | ||
* <code><b>Storm Rate | * <code><b>Storm Rate</b></code> - Limit the number of broadcast packets transmitted by an interface. The rate is measured in bits per second (bps). | ||
* <code><b>Include Unknown Unicast</b></code> - Include unicast packets without an entry in host table in <code>Storm Rate</code> limitation | |||
* <code><b>Include Unknown Unicast</b></code> - Include unicast packets without an entry in host table in <code>Storm Rate</code> limitation</td> | * <code><b>Flood Unknown Multicast</b></code> - Flood multicast packets without an entry in igmp multicast registration table</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 350: | Line 353: | ||
</tr> | </tr> | ||
</table> | </table> | ||
{{ Note | It is possible to limit ingress/egress traffic per port basis. The policer is used for ingress traffic, the shaper is used for egress traffic. The ingress policer controls the received traffic with packet drops. Everything that exceeds the defined limit will get dropped. This can affect the TCP congestion control mechanism on end hosts and achieved bandwidth can be actually less than defined. The egress shaper tries to queue packets that exceed the limit instead of dropping them. Eventually, it will also drop packets when the output queue gets full, however, it should allow utilizing the defined throughput better.}} | |||
==RSTP== | ==RSTP== | ||
| Line 423: | Line 428: | ||
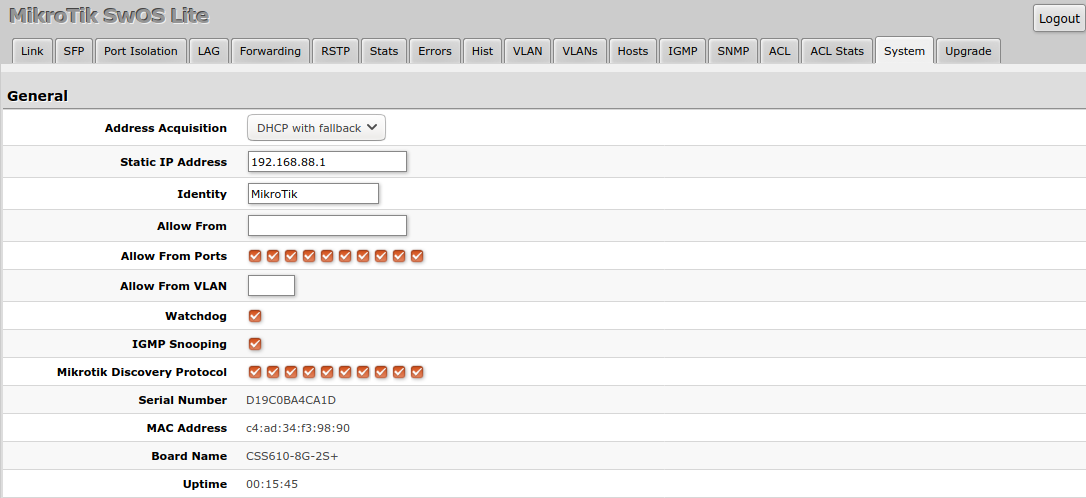
<p>VLAN configuration for switch ports.</p> | <p>VLAN configuration for switch ports.</p> | ||
[[File: | [[File:swos_vlan_css610.png|center|alt=Alt text|Port VLAN Settings|center|frame]] | ||
<br> | <br> | ||
| Line 467: | Line 472: | ||
<br/> | <br/> | ||
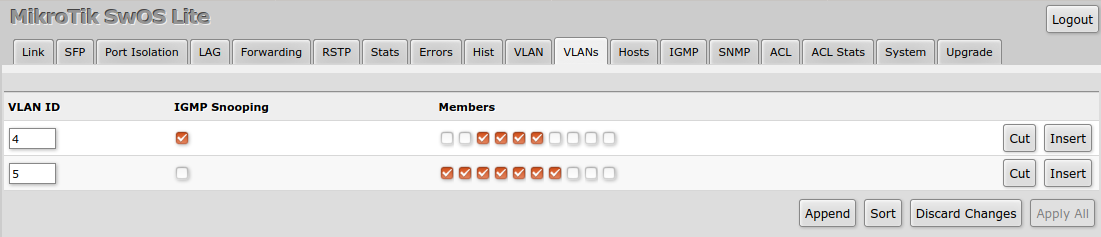
<p>VLAN membership configuration for switch ports.</p> | <p>VLAN membership configuration for switch ports.</p> | ||
[[File: | [[File:swos_vlans_css610.png|center|alt=Alt text|VLAN Table Settings|center|frame]] | ||
<br/> | <br/> | ||
| Line 501: | Line 506: | ||
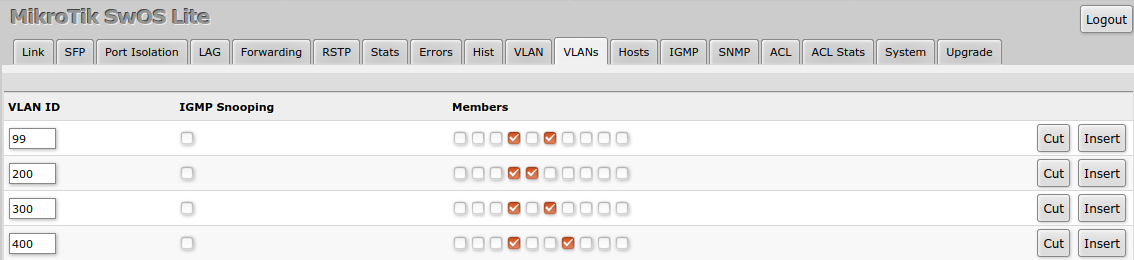
==Hosts== | ==Hosts== | ||
<p>This table represents dynamically learnt MAC address to port mapping entries. It can contain two kinds of entries: dynamic and static. Dynamic entries get added automatically, this is also called a learning process: when switch receives a packet from certain port, it adds the packet's source MAC address and port it received the packet from to host table, so when a packet comes in with certain destination MAC address it knows to which port it should forward the packet. If the destination MAC address is not present in host table then it forwards the packet to all ports in the group. Dynamic entries take about 5 minutes to time out. | <p>This table represents dynamically learnt MAC address to port mapping entries. It can contain two kinds of entries: dynamic and static. Dynamic entries get added automatically, this is also called a learning process: when switch receives a packet from certain port, it adds the packet's source MAC address and port it received the packet from to host table, so when a packet comes in with certain destination MAC address it knows to which port it should forward the packet. If the destination MAC address is not present in host table then it forwards the packet to all ports in the group. Dynamic entries take about 5 minutes to time out. CSS610 devices supports 16383 host table entries.</p> | ||
<p>Static entries will take over dynamic if dynamic entry with same mac-address already exists. Also by adding a static entry you get access to some more functionality.</p> | <p>Static entries will take over dynamic if dynamic entry with same mac-address already exists. Also by adding a static entry you get access to some more functionality.</p> | ||
[[File: | [[File:swos_shost_css610.png|center|alt=Alt text|Host Table|center|frame]] | ||
<br> | <br> | ||
| Line 513: | Line 518: | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
<td><b> | <td><b>Port</b></td><td>Ports the packet should be forwarded to</td> | ||
</tr> | </tr> | ||
<tr> | <tr> | ||
| Line 534: | Line 539: | ||
==IGMP Snooping== | ==IGMP Snooping== | ||
IGMP Snooping | IGMP Snooping controls multicast streams and prevents multicast flooding. The feature allows a switch to listen in the IGMP conversation between hosts and routers. | ||
Enable this option under System tab. | Enable this option under System tab. | ||
[[File: | [[File:css610_igmp_snooping.png|alt=Alt text|IGMP Snooping under System tab|center|frame]] | ||
<br> | <br> | ||
| Line 546: | Line 551: | ||
It is possible to enable IGMP Snooping for a specific VLAN ID under VLANs menu. | It is possible to enable IGMP Snooping for a specific VLAN ID under VLANs menu. | ||
[[File: | [[File:css610_igmp_vlantab.png|alt=Alt text|IGMP Snooping VLANs settings|center|frame]] | ||
==SNMP== | ==SNMP== | ||
| Line 586: | Line 591: | ||
<p>An access control list (ACL) rule table is very powerful tool allowing wire speed packet filtering, forwarding and VLAN tagging based on L2,L3 protocol header field conditions. Each rule contains a conditions part and an action part.</p> | <p>An access control list (ACL) rule table is very powerful tool allowing wire speed packet filtering, forwarding and VLAN tagging based on L2,L3 protocol header field conditions. Each rule contains a conditions part and an action part.</p> | ||
[[File: | [[File:CSS610-ACL-table.png|frameless|border|upright=4.4|center|CSS610 ACL table]] | ||
<div style="clear:both"></div> | <div style="clear:both"></div> | ||
Latest revision as of 15:57, 21 July 2021

Warning: This manual is moved to https://help.mikrotik.com/docs/display/SWOS/CSS610+series+Manual
Summary
SwOS Lite is an operating system designed specifically for administration of MikroTik CSS610 series switch products.
SwOS Lite is configurable from your web browser. It gives you all the basic functionality for a managed switch, plus more: allows to manage port-to-port forwarding, broadcast storm control, apply MAC filter, configure VLANs, mirror traffic, apply bandwidth limitation and even adjust some MAC and IP header fields.
CSS610 series switches support only SwOS Lite operating system.
The main differences compared to CSS3xx series switches are:
- unsupported Independent VLAN Learning;
- unsupported VLAN mode "enabled";
- unsupported ACL Rate limiting;
- supported Port Egress Rate limiting

Warning: Each RouterBoard switch series device has its own firmware which cannot be installed on other series models!
- CSS610-1Gi-7R-2S+ supports SwOS Lite v2.12 and newer.
- CSS610-8G-2S+ supports SwOS Lite v2.12 and newer.
CSS610 features
| Features | Description |
|---|---|
| Forwarding |
|
| Spanning Tree Protocol |
|
| Link Aggregation |
|
| Multicast Forwarding |
|
| Mirroring |
|
| VLAN |
|
| Security |
|
| Quality of Service (QoS) |
|
| Access Control List |
|
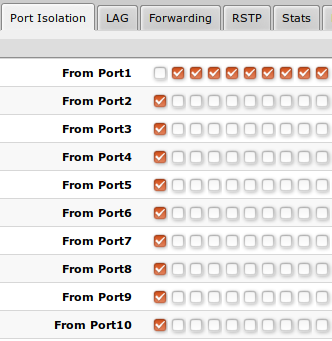
Connecting to the Switch
Open your web browser and enter IP address of your Switch (192.168.88.1 by default) and login screen will appear.
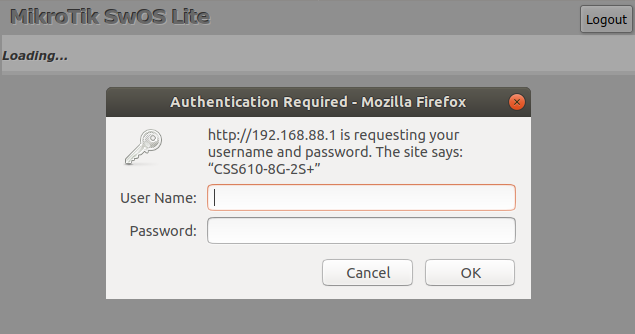
SwOS default IP address: 192.168.88.1, user name: admin and there is no password.

Note: MikroTik Neighbor Discovery protocol tools can be used to discover IP address of Mikrotik switch. Manual:IP/Neighbor_discovery. Currently LLDP is not supported.
Interface Overview
SwOS interface menu consists of multiple tabs depending on the device model. These are all possible SwOS menus: Link, PoE, SFP, Port Isolation, LAG, Forwarding, RSTP, Stats, Errors, Hist, VLAN, VLANs, Hosts, IGMP, SNMP, ACL, System, Health and Upgrade.
Description of buttons in SwOS configuration tool:
- Append - add new item to the end of the list
- Apply All - applies current configuration changes
- Cut - removes item from the list
- Clear - resets properties of the item
- Discard Changes - removes unsaved configuration
- Insert - add new item to the list (places it before current item)
- Sort - sort VLAN table by VLAN-IDs; sort host table by MAC addresses
- Change Password - changes password of the switch
- Logout - logout from current Switch
- Reboot - reboot the switch
- Reset Configuration - reset configuration back to factory defaults
- Choose File - browse for upgrade or backup file
- Upgrade - upgrade firmware of the Switch
- Restore Backup - restore Switch using selected backup file
- Save Backup - generate and download backup file from the Switch
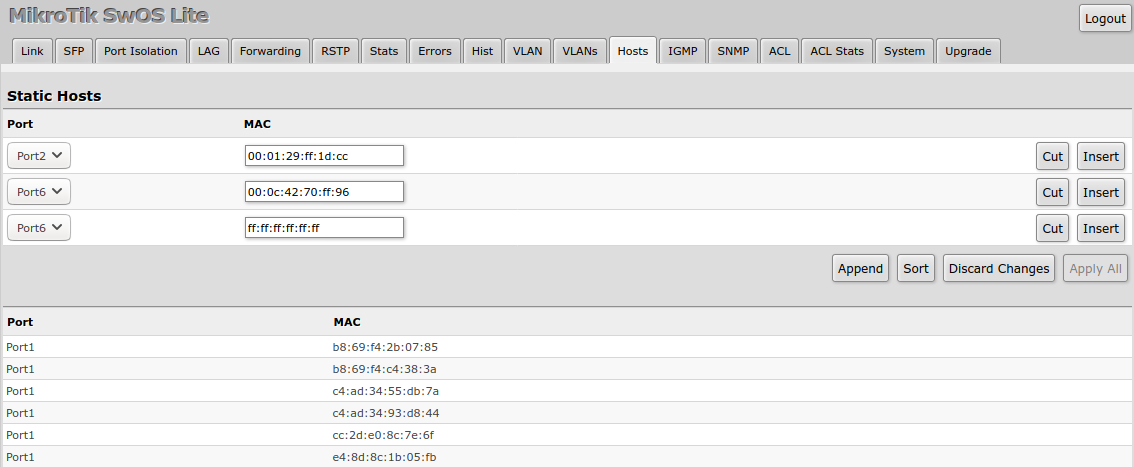
System
System Tab performs the following functions:
- General information about Switch
- Switch management
- Configuration reset
- Backup and restore configuration

Note: SwOS uses a simple algorithm to ensure TCP/IP communication - it just replies to the same IP and MAC address packet came from. This way there is no need for Default Gateway on the device itself.
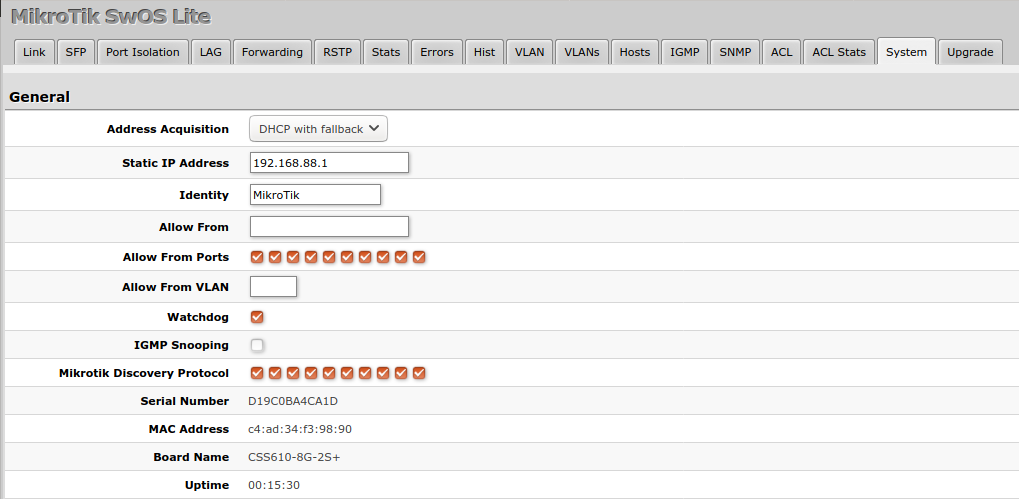
| Property | Description |
|---|---|
| Address Acquisition | Specify which address acquisition method to use:
|
| Static IP Address | IP address of the switch in case of Address Acquisition is set as DHCP with fallback or static |
| Identity | Name of the switch (for Mikrotik Neighbor Discovery protocol) |
| Allow From | IP address from which the switch is accessible. Default value is '0.0.0.0/0' - any address |
| Allow From Ports | List of switch ports from which it is accessible |
| Allow From VLAN | VLAN ID from which the switch is accessible (VLAN Mode on ingress port must be other than disabled in order to connect) |
| Watchdog | Enable or disable system Watchdog. It will reset CPU of the switch in case of fault condition |
| IGMP Snooping | Enable or disable IGMP Snooping |
| Mikrotik Discovery Protocol | Enable or disable Mikrotik Neighbor Discovery protocol |
| MAC Address | MAC address of the switch (Read-only) |
| Serial Number | Serial number of the switch (Read-only) |
| Board Name | MikroTik model name of the switch (Read-only) |
| Uptime | Current switch uptime (Read-only) |
DHCP & PPPoE Snooping
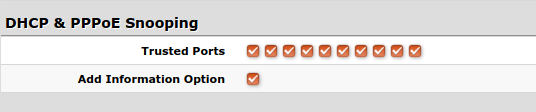
| Property | Description |
|---|---|
| Trusted Ports | Group of ports, which allows DHCP or PPPoE servers to provide a requested information. Mainly used to limit unauthorized servers to provide malicious information for users, access ports usually do not configure as trusted |
| Add Information Option | Enables or disables DHCP Option-82 information. When enabled, the Option-82 information (Agent Remote ID and Circuit ID) is added for DHCP packets received from untrusted ports. Can be used together with Option-82 capable DHCP server to assign IP addresses and implement policies |
Password and Backup
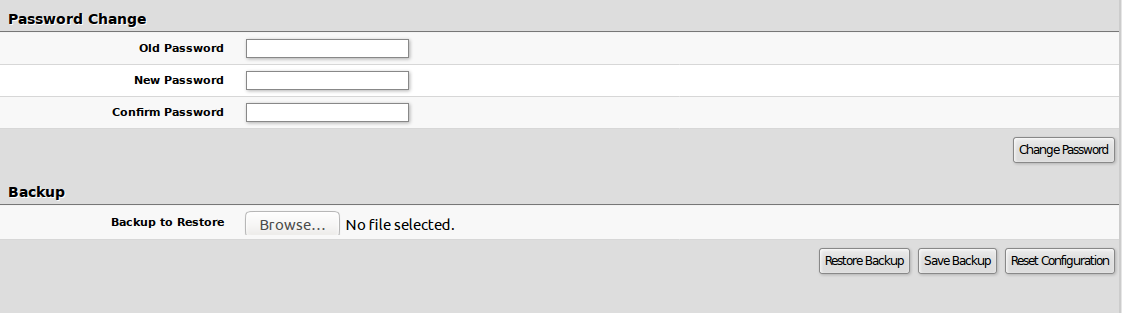
Link
Link Tab allows you to configure each interface settings and monitor link status
| Property | Description |
|---|---|
| Enabled | Enable or disable port |
| Name | Editable port name |
| Link Status | Current link status (Read-only) |
| Auto Negotiation | Enable or disable auto negotiation |
| Speed | Specify speed setting of the port (requires auto negotiation to be disabled) |
| Full Duplex | Specify duplex mode of the port (requires auto negotiation to be disabled) |
| Flow control | Enable or disable 802.3x Flow control |
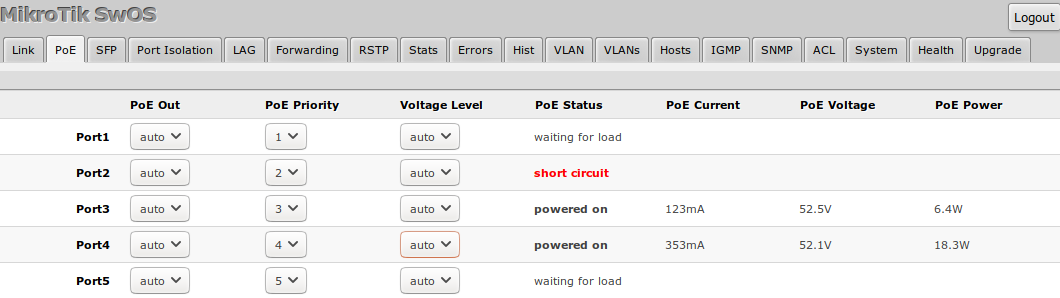
PoE
Devices with PoE-out support have some configuration options and certain monitoring features, like PoE-out current, voltage, etc. For more detailed description, see Manual:PoE-Out.
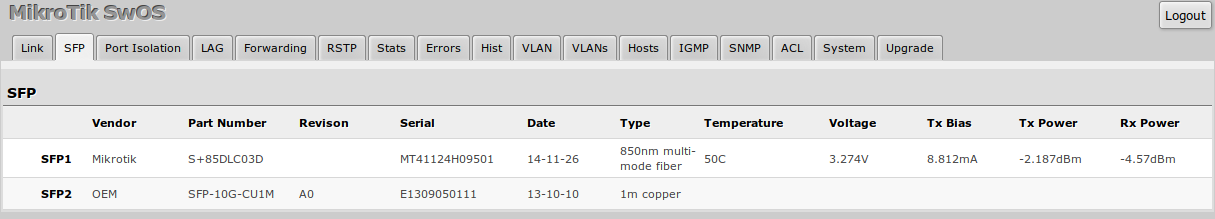
SFP
SFP tab allows you to monitor status of SFP/SFP+ modules.
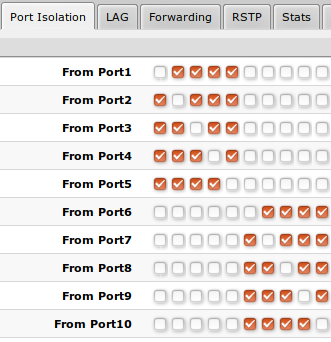
Port Isolation
Port Isolation table allows or restricts traffic forwarding between specific ports. By default, all available switch chip ports can communicate with any other port, there is no isolation used. When the checkbox is enabled/ticked you allow to forward traffic from this port towards the ticked port. Below are some port isolation examples.

Note: It is possible to check/uncheck multiple checkboxes by checking one of them and then dragging horizontally (Click & Drag).

Note: (R)STP will only work properly in Private VLAN setups. In setups with multiple isolated switch groups (R)STP might not properly receive BPDUs and therefore fail to detect network loops.
LAG
IEEE 802.3ad (LACP) compatible link aggregation is supported, as well as static link aggregation to ensure failover and load balancing is based only on Layer2 hashing.
Up to 16 link aggregation groups with up to 8 ports per a group are supported.
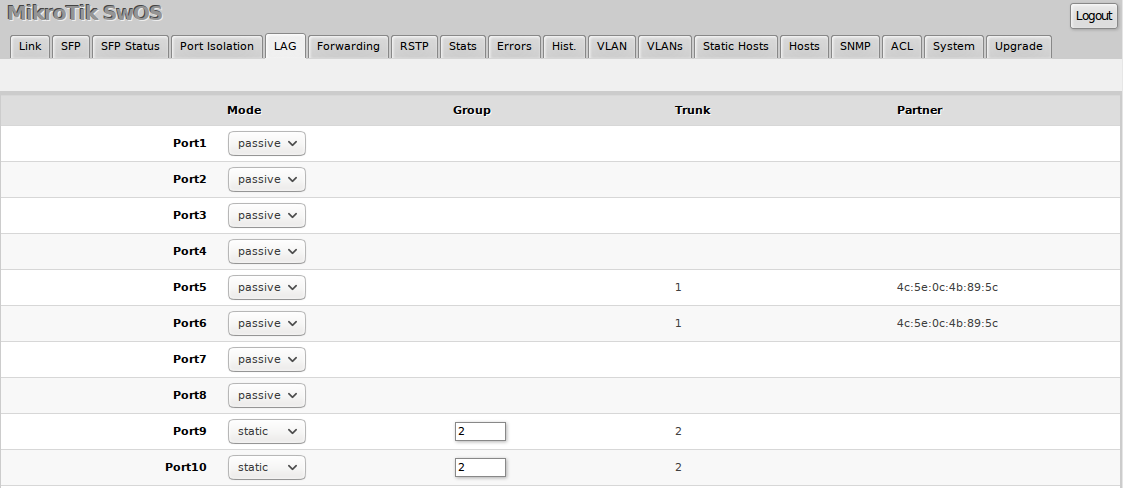
Each individual port can be configured as Passive LACP, Active LACP or a Static LAG port.
| Property | Description |
|---|---|
| Mode (default: passive) | Specify LACP packet exchange mode or Static LAG mode on ports:
|
| Property | Description |
|---|---|
| Group | Specify a Static LAG group |
| Trunk (read only) | Represents group number port belongs to. |
| Partner (read only) | Represents partner mac-address. |
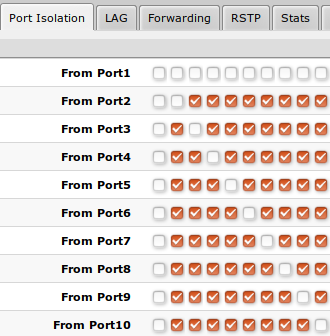
Forwarding
Forwarding Tab provides advanced forwarding options among switch ports, port locking, port mirroring, bandwidth limit and broadcast storm control features.
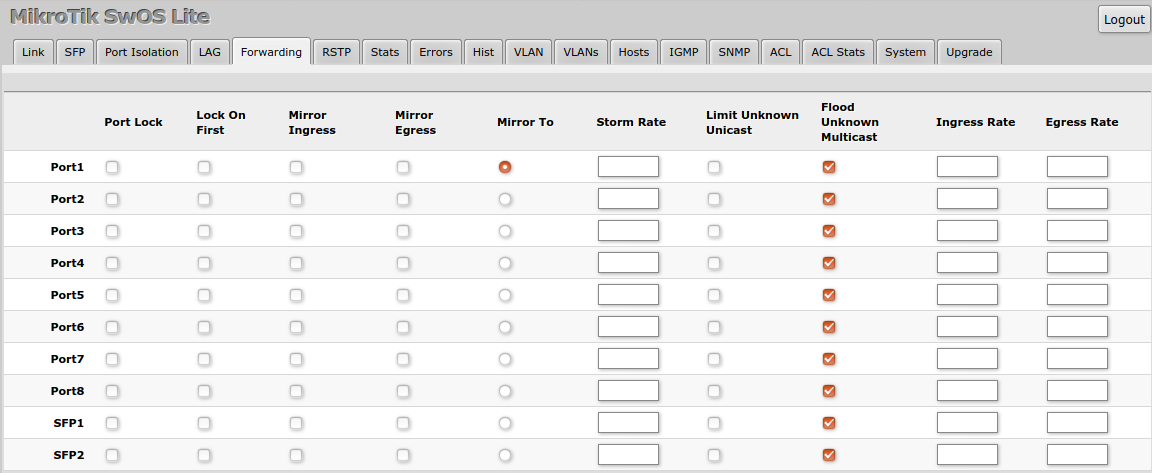
| Property | Description |
|---|---|
| Port Lock |
|
| Port Mirroring |
|
| Broadcast Storm Control |
|
| Bandwidth Limit |
|

Note: It is possible to limit ingress/egress traffic per port basis. The policer is used for ingress traffic, the shaper is used for egress traffic. The ingress policer controls the received traffic with packet drops. Everything that exceeds the defined limit will get dropped. This can affect the TCP congestion control mechanism on end hosts and achieved bandwidth can be actually less than defined. The egress shaper tries to queue packets that exceed the limit instead of dropping them. Eventually, it will also drop packets when the output queue gets full, however, it should allow utilizing the defined throughput better.
RSTP
Per port and global RSTP configuration and monitoring is available in the RSTP menu.
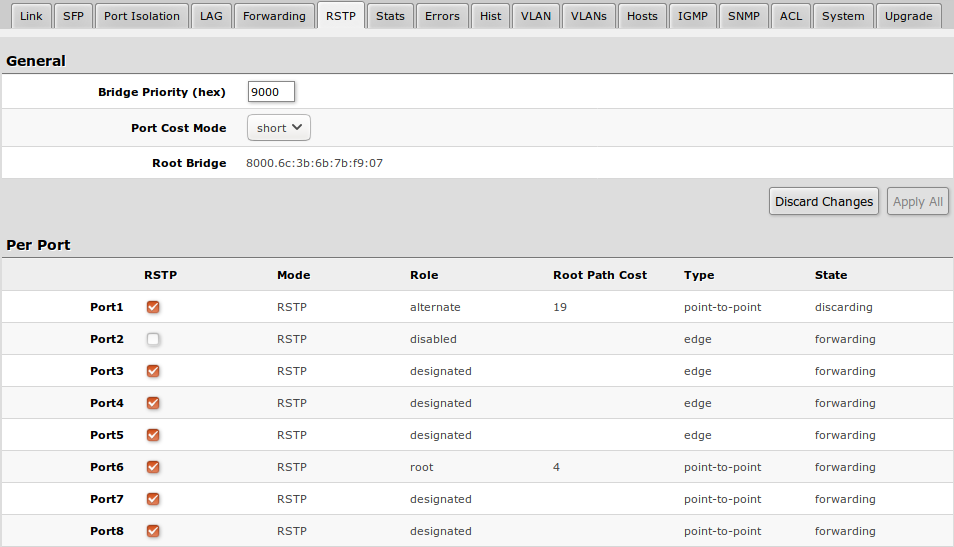
| Property | Description |
|---|---|
| Bridge Priority (hex) | RSTP bridge priority for Root Bridge selection |
| Port Cost Mode | There are two methods for automatically detecting RSTP port cost depending on link speed.
|
| Root Bridge | The priority and MAC address of the selected Root Bridge in the network (Read-only) |
| Property | Description |
|---|---|
| RSTP | Enable or disable STP/RSTP functionality on this port |
| Mode | Shows STP/RSTP functionality mode on specific port (Read-only):
|
| Role | Shows specific port role (Read-only):
|
| Root Path Cost | Shows root path cost for ports that are facing root bridge (Read-only) |
| Type |
|
| State | Shows each port state (Read-only):
|
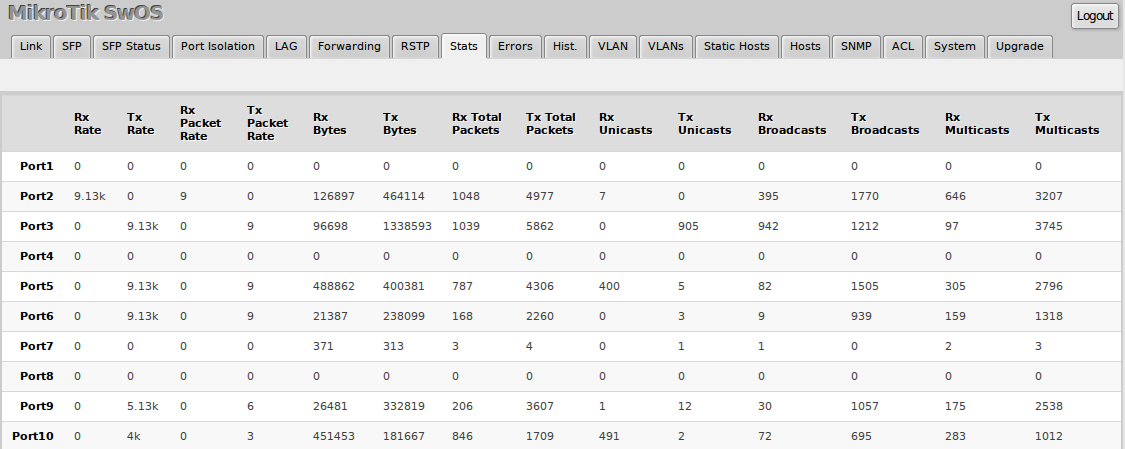
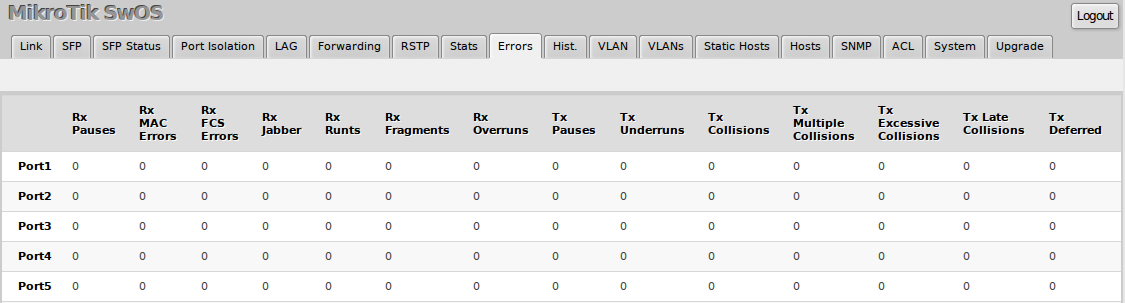
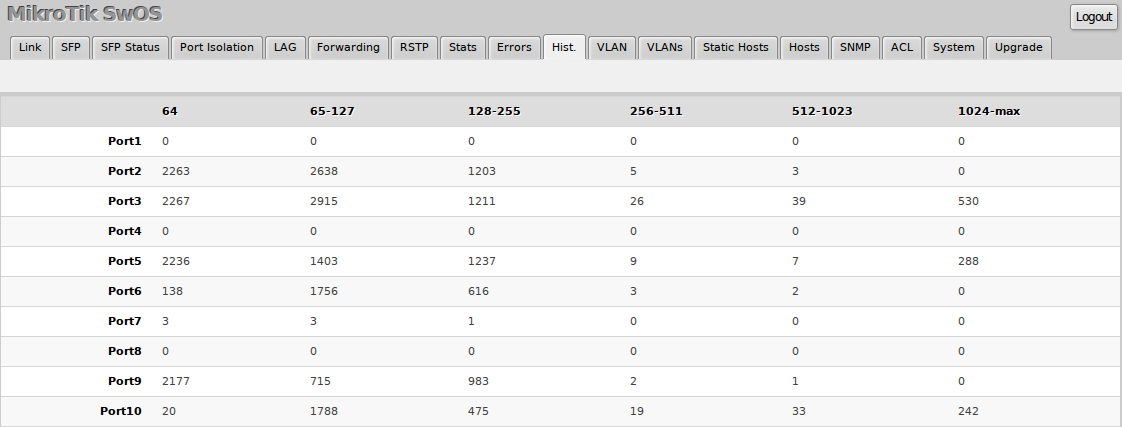
Stats, Errors and Histogram
These menus provide detailed information about received and transmitted packets.
VLAN and VLANs
VLAN configuration for switch ports.
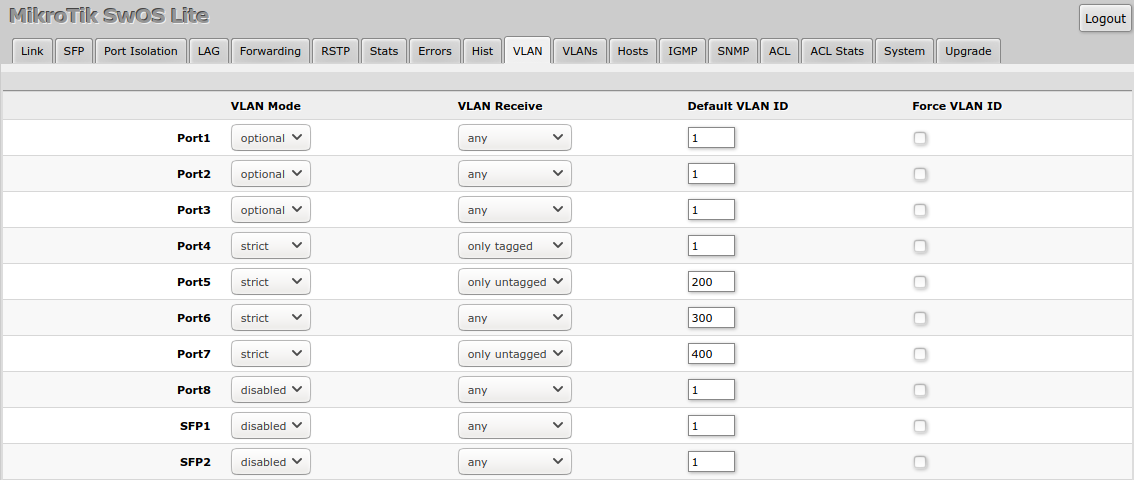
| Property | Description |
|---|---|
| VLAN Mode (disabled | optional | strict; Default: optional) | VLAN filtering mode, these options are relevant to egress ports (except for strict mode).
|
| VLAN Receive (any | only tagged | only untagged; Default: optional) | Ingress traffic filtering based on VLAN tag presence.
|
| Default VLAN ID (integer: 1..4095; Default: 1) | VLAN ID which will be assigned on ingress traffic. Only has effect on untagged traffic, it will be ignored for tagged traffic. This parameter is usually used to allocate access ports with specific VLAN. It is also used to untag egress traffic if packet's VLAN ID matches Default VLAN ID. |
| Force VLAN ID (integer: yes | no; Default: no) | Assigns the Default VLAN ID value to all ingress traffic (tagged and untagged). Has effect in all VLAN Modes. If port receives tagged traffic and Default VLAN ID is set to 1, then with this parameter the egress traffic will be untagged. |
VLAN membership configuration for switch ports.
| Property | Description |
|---|---|
| VLAN ID (integer: 1..4095; Default: 0) | VLAN ID to which assign ports. |
| IGMP Snooping (yes | no; Default: no) | Enables or disables IGMP Snooping on the defined VLAN. When enabled, the switch will listen to IGMP Join and Leave requests from the defined VLAN and only forward traffic to ports, which have sent IGMP membership requests from the defined VLAN. When disabled, the switch will flood all VLAN member ports with Multicast traffic. |
| Members (ports; Default: none) | Group of ports, which are allowed to forward traffic on the defined VLAN. |
VLAN Configuration Example
Simple trunk and access port configuration, as well as trunk and hybrid port configuration examples can be found in this article - SWOS/CSS326-VLAN-Example.
Hosts
This table represents dynamically learnt MAC address to port mapping entries. It can contain two kinds of entries: dynamic and static. Dynamic entries get added automatically, this is also called a learning process: when switch receives a packet from certain port, it adds the packet's source MAC address and port it received the packet from to host table, so when a packet comes in with certain destination MAC address it knows to which port it should forward the packet. If the destination MAC address is not present in host table then it forwards the packet to all ports in the group. Dynamic entries take about 5 minutes to time out. CSS610 devices supports 16383 host table entries.
Static entries will take over dynamic if dynamic entry with same mac-address already exists. Also by adding a static entry you get access to some more functionality.
| Property | Description |
|---|---|
| Port | Ports the packet should be forwarded to |
| MAC | MAC address |
| Property | Description |
|---|---|
| Port | Ports the packet should be forwarded to (Read-only) |
| MAC | Learned MAC address (Read-only) |
IGMP Snooping
IGMP Snooping controls multicast streams and prevents multicast flooding. The feature allows a switch to listen in the IGMP conversation between hosts and routers.
Enable this option under System tab.
Available IGMP snooping data can be found under IGMP tab:
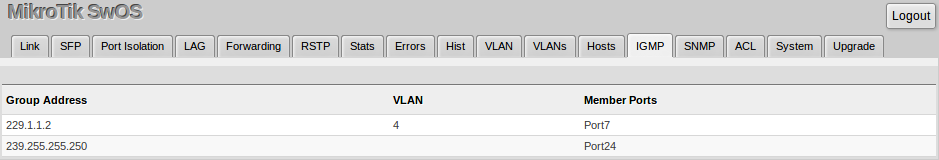
It is possible to enable IGMP Snooping for a specific VLAN ID under VLANs menu.
SNMP
SwOS supports SNMP v1 and uses IF-MIB, SNMPv2-MIB, BRIDGE-MIB and MIKROTIK-MIB (only for health, PoE-out and SFP diagnostics) for SNMP reporting.
Available SNMP data:
System informationSystem uptimePort statusInterface statisticsHost table information
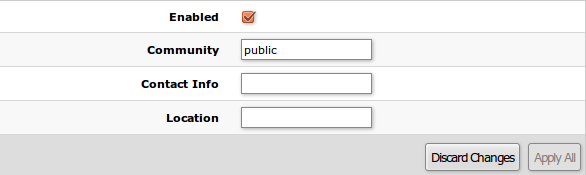
| Property | Description |
|---|---|
| Enabled | Enable or disable SNMP service |
| Community | SNMP community name |
| Contact Info | Contact information for the NMS |
| Location | Location information for the NMS |
ACL Tab
An access control list (ACL) rule table is very powerful tool allowing wire speed packet filtering, forwarding and VLAN tagging based on L2,L3 protocol header field conditions. Each rule contains a conditions part and an action part.
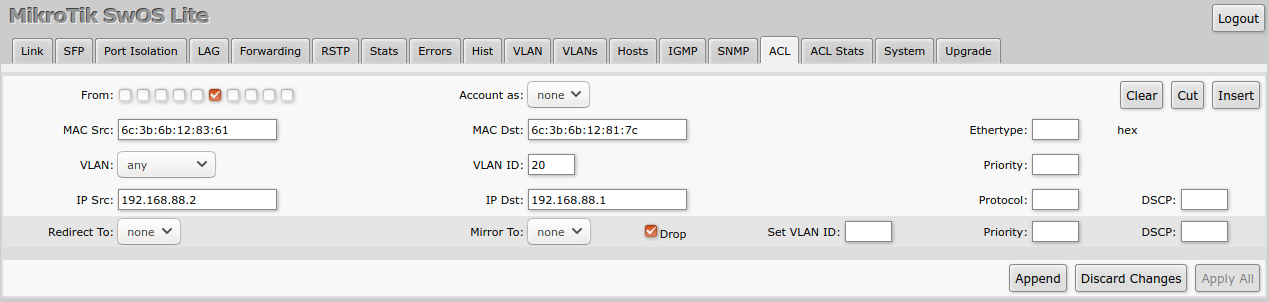
Conditions part parameters
| Property | Description |
|---|---|
| From | Port that packet came in from |
| MAC Src | Source MAC address and mask |
| MAC Dst | Destination MAC address and mask |
| Ethertype | Protocol encapsulated in the payload of an Ethernet Frame |
| VLAN |
VLAN header presence:
|
| VLAN ID | VLAN tag ID |
| Priority | Priority in VLAN tag |
| IP Src (IP/netmask:port) | Source IPv4 address, netmask and L4 port number |
| IP Dst (IP/netmask:port) | Destination IPv4 address, netmask and L4 port number |
| Protocol (integer) | IP protocol |
| DSCP | IP DSCP field |
Action part parameters
| Property | Description |
|---|---|
| Redirect To | Force new packets destination port |
| Mirror | Clones packet and sends it to mirror-target port |
| Drop | Drop packet |
| Set VLAN ID | Changes the VLAN tag ID, if VLAN tag is present |
| Priority | Changes the VLAN tag priority bits, if VLAN tag is present |
| DSCP | Changes the IP DSCP field |
Reset and Reinstall
CSS610 switches have built-in backup SwOS firmware which can be loaded in case standard firmware breaks or upgrade fails:
- Holding Reset button for few seconds while CSS610 is booting resets configuration and loads backup firmware SwOS "2.XXp".
- After loading backup firmware SwOS "2.XXp" it is possible to connect to 192.168.88.1 using web browser and install new SwOS firmware.