Manual:Interface/VLAN: Difference between revisions
No edit summary |
|||
| Line 343: | Line 343: | ||
[[Category:VPN|V]] | [[Category:VPN|V]] | ||
[[Category:Interface|V]] | [[Category:Interface|V]] | ||
[[Category:Bridging and switching]] | |||
Revision as of 15:25, 17 April 2018
Summary
Sub-menu: /interface vlan
Standards: IEEE 802.1Q
Virtual Local Area Network (VLAN) is a Layer 2 method that allows multiple Virtual LANs on a single physical interface (ethernet, wireless, etc.), giving the ability to segregate LANs efficiently.
You can use MikroTik RouterOS (as well as Cisco IOS, Linux and other router systems) to mark these packets as well as to accept and route marked ones.
As VLAN works on OSI Layer 2, it can be used just as any other network interface without any restrictions. VLAN successfully passes through regular Ethernet bridges.
You can also transport VLANs over wireless links and put multiple VLAN interfaces on a single wireless interface. Note that as VLAN is not a full tunnel protocol (i.e., it does not have additional fields to transport MAC addresses of sender and recipient), the same limitation applies to bridging over VLAN as to bridging plain wireless interfaces. In other words, while wireless clients may participate in VLANs put on wireless interfaces, it is not possible to have VLAN put on a wireless interface in station mode bridged with any other interface.
802.1Q
The most commonly used protocol for Virtual LANs (VLANs) is IEEE 802.1Q. It is a standardized encapsulation protocol that defines how to insert a four-byte VLAN identifier into Ethernet header. (see Figure 12.1.)
Each VLAN is treated as a separate subnet. It means that by default, a host in a specific VLAN cannot communicate with a host that is a member of another VLAN, although they are connected in the same switch. So if you want inter-VLAN communication you need a router. RouterOS supports up to 4095 VLAN interfaces, each with a unique VLAN ID, per interface. VLAN priorities may also be used and manipulated.
When the VLAN extends over more than one switch, the inter-switch link has to become a 'trunk', where packets are tagged to indicate which VLAN they belong to. A trunk carries the traffic of multiple VLANs; it is like a point-to-point link that carries tagged packets between switches or between a switch and router.

Note: The IEEE 802.1Q standard has reserved VLAN IDs with special use cases, the following VLAN IDs should not be used in generic VLAN setups: 0, 1, 4095
Q-in-Q
Original 802.1Q allows only one vlan header, Q-in-Q on the other hand allows two or more vlan headers. In RouterOS Q-in-Q can be configured by adding one vlan interface over another. Example:
/interface vlan add name=vlan1 vlan-id=11 interface=ether1 add name=vlan2 vlan-id=12 interface=vlan1
If any packet is sent over 'vlan2' interface, two vlan tags will be added to ethernet header - '11' and '12'.
Properties
| Property | Description |
|---|---|
| arp (disabled | enabled | proxy-arp | reply-only; Default: enabled) | Address Resolution Protocol mode |
| interface (name; Default: ) | Name of physical interface on top of which VLAN will work |
| l2mtu (integer; Default: ) | Layer2 MTU. For VLANS this value is not configurable. Read more>> |
| mtu (integer; Default: 1500) | Layer3 Maximum transmission unit |
| name (string; Default: ) | Interface name |
| use-service-tag (yes | no; Default: ) | 802.1ad compatible Service Tag |
| vlan-id (integer: 4095; Default: 1) | Virtual LAN identifier or tag that is used to distinguish VLANs. Must be equal for all computers that belong to the same VLAN. |

Note: MTU should be set to 1500 bytes same as on Ethernet interfaces. But this may not work with some Ethernet cards that do not support receiving/transmitting of full size Ethernet packets with VLAN header added (1500 bytes data + 4 bytes VLAN header + 14 bytes Ethernet header). In this situation MTU 1496 can be used, but note that this will cause packet fragmentation if larger packets have to be sent over interface. At the same time remember that MTU 1496 may cause problems if path MTU discovery is not working properly between source and destination.
Setup examples
VLANs on Mikrotik environment are also described here: VLANs with bridging
Layer2 VLAN examples

Warning: These configurations are known to cause issues with other vendor devices, especially in STP enabled network, you should use bridge VLAN filtering instead in case you are using RouterOS v6.41 or newer. You can read more about this Here.
Port based VLAN tagging #1 (Trunk and Access ports)
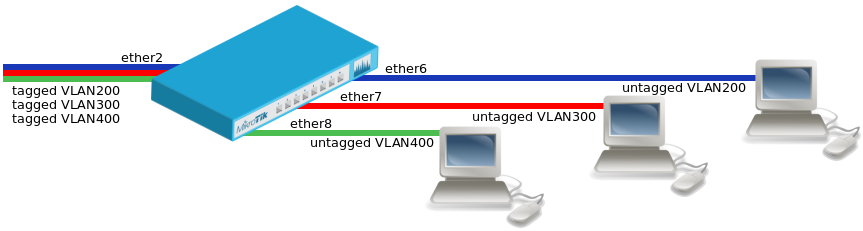
- Add necessary VLAN interfaces on ethernet interface to make it as a VLAN trunk port
/interface vlan add interface=ether2 name=eth2-vlan200 vlan-id=200 add interface=ether2 name=eth2-vlan300 vlan-id=300 add interface=ether2 name=eth2-vlan400 vlan-id=400
- Add bridges for each VLAN
/interface bridge add name=bridge-vlan200 add name=bridge-vlan300 add name=bridge-vlan400
- Add VLAN interfaces to their corresponding bridges and ethernet interfaces where untagged traffic is necessary
/interface bridge port add bridge=bridge-vlan200 interface=eth2-vlan200 add bridge=bridge-vlan200 interface=ether6 add bridge=bridge-vlan300 interface=eth2-vlan300 add bridge=bridge-vlan300 interface=ether7 add bridge=bridge-vlan400 interface=eth2-vlan400 add bridge=bridge-vlan400 interface=ether8
Port based VLAN tagging #2 (Trunk and Hybrid ports)
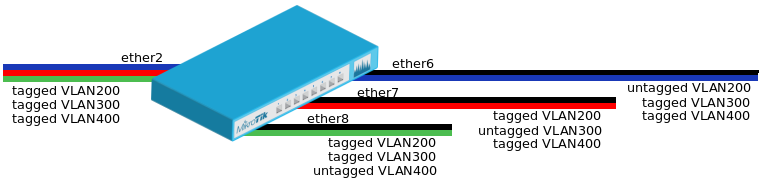
- Add necessary VLAN interfaces on ethernet interfaces to make them as VLAN trunk ports
/interface vlan add interface=ether2 name=eth2-vlan200 vlan-id=200 add interface=ether2 name=eth2-vlan300 vlan-id=300 add interface=ether2 name=eth2-vlan400 vlan-id=400 add interface=ether6 name=eth6-vlan300 vlan-id=300 add interface=ether6 name=eth6-vlan400 vlan-id=400 add interface=ether7 name=eth7-vlan200 vlan-id=200 add interface=ether7 name=eth7-vlan400 vlan-id=400 add interface=ether8 name=eth8-vlan200 vlan-id=200 add interface=ether8 name=eth8-vlan300 vlan-id=300
- Add bridges for each VLAN
/interface bridge add name=bridge-vlan200 add name=bridge-vlan300 add name=bridge-vlan400
- Add VLAN interfaces to their corresponding bridges and ethernet interfaces where untagged traffic is necessary
/interface bridge port add bridge=bridge-vlan200 interface=eth2-vlan200 add bridge=bridge-vlan200 interface=eth7-vlan200 add bridge=bridge-vlan200 interface=eth8-vlan200 add bridge=bridge-vlan200 interface=ether6 add bridge=bridge-vlan300 interface=eth2-vlan300 add bridge=bridge-vlan300 interface=eth6-vlan300 add bridge=bridge-vlan300 interface=eth8-vlan300 add bridge=bridge-vlan300 interface=ether7 add bridge=bridge-vlan400 interface=eth2-vlan400 add bridge=bridge-vlan400 interface=eth6-vlan400 add bridge=bridge-vlan400 interface=eth7-vlan400 add bridge=bridge-vlan400 interface=ether8
Layer3 VLAN examples
Simple VLAN routing
Lets assume that we have several MikroTik routers connected to a hub. Remember that a hub is an OSI physical layer device (if there is a hub between routers, then from L3 point of view it is the same as an Ethernet cable connection between them). For simplification assume that all routers are connected to the hub using ether1 interface and has assigned IP addresses as illustrated in figure below. Then on each of them the VLAN interface is created. File:Image12004.gif
Configuration for R2 and R4 is shown below:
R2:
[admin@MikroTik] /interface vlan> add name=VLAN2 vlan-id=2 interface=ether1 disabled=no [admin@MikroTik] /interface vlan> print Flags: X - disabled, R - running, S - slave # NAME MTU ARP VLAN-ID INTERFACE 0 R VLAN2 1500 enabled 2 ether1
R4:
[admin@MikroTik] /interface vlan> add name=VLAN2 vlan-id=2 interface=ether1 disabled=no [admin@MikroTik] /interface vlan> print Flags: X - disabled, R - running, S - slave # NAME MTU ARP VLAN-ID INTERFACE 0 R VLAN2 1500 enabled 2 ether1
The next step is to assign IP addresses to the VLAN interfaces.
R2:
[admin@MikroTik] ip address> add address=10.10.10.3/24 interface=VLAN2 [admin@MikroTik] ip address> print Flags: X - disabled, I - invalid, D - dynamic # ADDRESS NETWORK BROADCAST INTERFACE 0 10.0.1.4/24 10.0.1.0 10.0.1.255 ether1 1 10.20.0.1/24 10.20.0.0 10.20.0.255 pc1 2 10.10.10.3/24 10.10.10.0 10.10.10.255 vlan2 [admin@MikroTik] ip address>
R4:
[admin@MikroTik] ip address> add address=10.10.10.5/24 interface=VLAN2 [admin@MikroTik] ip address> print Flags: X - disabled, I - invalid, D - dynamic # ADDRESS NETWORK BROADCAST INTERFACE 0 10.0.1.5/24 10.0.1.0 10.0.1.255 ether1 1 10.30.0.1/24 10.30.0.0 10.30.0.255 pc2 2 10.10.10.5/24 10.10.10.0 10.10.10.255 vlan2 [admin@MikroTik] ip address>
At this point it should be possible to ping router R4 from router R2 and vice versa:
"Ping from R2 to R4:" [admin@MikroTik] ip address> /ping 10.10.10.5 10.10.10.5 64 byte ping: ttl=255 time=4 ms 10.10.10.5 64 byte ping: ttl=255 time=1 ms 2 packets transmitted, 2 packets received, 0% packet loss round-trip min/avg/max = 1/2.5/4 ms "From R4 to R2:" [admin@MikroTik] ip address> /ping 10.10.10.3 10.10.10.3 64 byte ping: ttl=255 time=6 ms 10.10.10.3 64 byte ping: ttl=255 time=1 ms 2 packets transmitted, 2 packets received, 0% packet loss round-trip min/avg/max = 1/3.5/6 ms
To make sure if VLAN setup is working properly, try to ping R1 from R2. If pings are timing out then VLANs are successfully isolated.
"From R2 to R1:" [admin@MikroTik] ip address> /ping 10.10.10.2 10.10.10.2 ping timeout 10.10.10.2 ping timeout 3 packets transmitted, 0 packets received, 100% packet loss
InterVLAN routing
If separate VLANs are implemented on a switch, then a router is required to provide communication between VLANs. Switch works at OSI layer 2 so it uses only Ethernet header to forward and does not check IP header. For this reason we must use the router that is working as a gateway for each VLAN. Without a router, a host is unable to communicate outside of its own VLAN. Routing process between VLANs described above is called inter-VLAN communication.
To illustrate inter-VLAN communication, we will create a trunk that will carry traffic from three VLANs (VLAN2 and VLAN3, VLAN4) across a single link between a Mikrotik router and a manageable switch that supports VLAN trunking. File:Image12005.gif
Each VLAN has its own separate subnet (broadcast domain) as we see in figure above:
- VLAN 2 – 10.10.20.0/24;
- VLAN 3 – 10.10.30.0/24;
- VLAN 4 – 10.10.40.0./24.
VLAN configuration on most switches is straightforward, basically we need to define which ports are members of the VLANs and define a 'trunk' port that can carry tagged frames between the switch and the router.
"Configuration example on MikroTik router:"
"Create VLAN interfaces:"
/interface vlan add name=VLAN2 vlan-id=2 interface=ether1 disabled=no add name=VLAN3 vlan-id=3 interface=ether1 disabled=no add name=VLAN4 vlan-id=4 interface=ether1 disabled=no
"Add IP addresses to VLANs:"
/ip address add address=10.10.20.1/24 interface=VLAN2 add address=10.10.30.1/24 interface=VLAN3 add address=10.10.40.1/24 interface=VLAN4
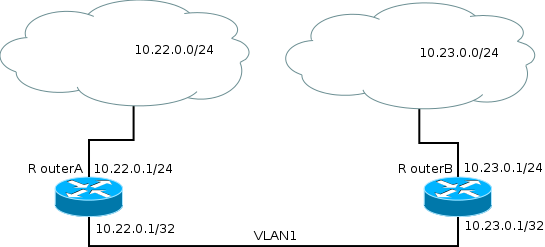
RouterOS /32 and IP unnumbered addresses
In RouterOS, to create a point-to-point tunnel with addresses you have to use address with a network mask of '/32' that effectively brings you the same features as some vendors unnumbered IP address.
There are 2 routers RouterA and RouterB where each is part of networks 10.22.0.0/24 and 10.23.0.0/24 respectively and to connect these routers using VLANs as a carrier with the following configuration:
RouterA:
/ip address add address=10.22.0.1/24 interface=ether1 /interface vlan add interface=ether2 vlan-id=1 name=vlan1 /ip address add address=10.22.0.1/32 interface=vlan1 network=10.23.0.1 /ip route add gateway=10.23.0.1 dst-address=10.23.0.0/24
RouterB:
/ip address add address=10.23.0.1/24 interface=ether1 /interface vlan add interface=ether2 vlan-id=1 name=vlan1 /ip address add address=10.23.0.1/32 interface=vlan1 network=10.22.0.1 /ip route add gateway=10.22.0.1 dst-address=10.22.0.0/24
[ Top | Back to Content ]