Manual:SNMP
Overview
Standards: RFC 1157
Package: system
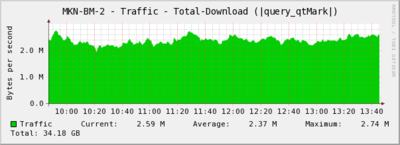
Simple Network Management Protocol (SNMP) is an Internet-standard protocol for managing devices on IP networks. SNMP can be used to graph various data with tools such as CACTI, MRTG or The Dude
RouterOS supports SNMP v1,2 and 3. SNMP write is also supported.
Quick Configuration
To enable SNMP in RouterOS:
[admin@MikroTik] /snmp> print
enabled: no
contact:
location:
engine-id:
trap-community: (unknown)
trap-version: 1
[admin@MikroTik] /snmp> set enabled yes
You can also specify administrative contact information in the above settings. All SNMP data will be available to communities configured in community menu.
General Properties
Sub-menu: /snmp
This sub menu allows to enable SNMP and to configure general settings.
| Property | Description |
|---|---|
| contact (string; Default: "") | Contact information |
| enabled (yes | no; Default: no) | Used to disable/enable SNMP service |
| engine-id (string; Default: "") | |
| location (string; Default: "") | Location information |
| trap-community (string; Default: public) | Which communities configured in community menu to use. |
| trap-generators (interfaces | start-trap; Default: ) | |
| trap-interfaces (string | all; Default: ) | |
| trap-target (list of IP/IPv6; Default: 0.0.0.0) | |
| trap-version (1|2|3; Default: 1) |
Community
Sub-menu: /snmp community
This sub-menu allows to set up access rights for the SNMP data.
There is little security in v1 and v2c, just Clear text community string („username“) and ability for Limiting access by IP adress.
Since SNMP v3, better options have been introduced - Authorisation (User + Pass) with MD5/SHA1, Encryption with DES.
[admin@MikroTik] /snmp community> print value-list
name: public
address: 0.0.0.0/0
security: none
read-access: yes
write-access: no
authentication-protocol: MD5
encryption-protocol: DES
authentication-password: *****
encryption-password: *****

Warning: Default settings only have one community named public without any additional security settings. These settings should be considered insecure and should be adjusted according required security profile.
Properties
| Property | Description |
|---|---|
| address (IP/IPv6 address; Default: 0.0.0.0/0) | Addresses from which connections to SNMP server is allowed |
| authentication-password (string; Default: "") | Password used to authenticate connection to the server |
| authentication-protocol (MD5 | SHA1; Default: MD5) | Protocol used for authentication |
| encryption-password (string; Default: "") | |
| encryption-protocol (DES; Default: DES) | |
| name (string; Default: ) | |
| read-access (yes | no; Default: yes) | Whether read access is enabled for this community |
| security (authorized | none | private; Default: none) | |
| write-access (yes | no; Default: no) | Whether write access is enabled for this community. Read more >> |
Management information base (MIB)
You can download the latest MikroTik RouterOS MIB file. RouterOS v5.x uses such MIBs:
- MIKROTIK-MIB
- MIB-2
- HOST-RESOURCES-MIB
- IF-MIB
- IP-MIB
- IP-FORWARD-MIB
- IPV6-MIB
- BRIDGE-MIB
- DHCP-SERVER-MIB
- CISCO-AAA-SESSION-MIB
- ENTITY-MIB
- UPS-MIB
- SQUID-MIB
Object identifiers (OID)
Each OID identifies a variable that can be read via SNMP. Although the MIB file contains all the needed OID values, you can also print individual OID information in the console with the print oid command at any menu level:
[admin@MikroTik] /interface> print oid
Flags: D - dynamic, X - disabled, R - running, S - slave
0 R name=.1.3.6.1.2.1.2.2.1.2.1 mtu=.1.3.6.1.2.1.2.2.1.4.1
mac-address=.1.3.6.1.2.1.2.2.1.6.1 admin-status=.1.3.6.1.2.1.2.2.1.7.1
oper-status=.1.3.6.1.2.1.2.2.1.8.1 bytes-in=.1.3.6.1.2.1.2.2.1.10.1
packets-in=.1.3.6.1.2.1.2.2.1.11.1 discards-in=.1.3.6.1.2.1.2.2.1.13.1
errors-in=.1.3.6.1.2.1.2.2.1.14.1 bytes-out=.1.3.6.1.2.1.2.2.1.16.1
packets-out=.1.3.6.1.2.1.2.2.1.17.1 discards-out=.1.3.6.1.2.1.2.2.1.19.1
errors-out=.1.3.6.1.2.1.2.2.1.20.1
Traps
SNMP traps enable an agent to notify the management station of significant events by way of an unsolicited SNMP message.
SNMP write
Since RouterOS v3, SNMP write is supported for some functions. SNMP write allows to change router configuration with SNMP requests. Consider to secure access to router or to router's SNMP, when SNMP and write-access are enabled.
Writable options
To change settings by SNMP requests, use the command below to allow SNMP write for the selected community, Write-access option for SNMP is available from v3.14,
/snmp community set <number> write-access=yes
System Identity
It's possible to change router system identity by SNMP set command,
snmpset -c public -v 1 192.168.0.0 1.3.6.1.2.1.1.5.0 s New_Identity
- snmpset, SNMP application used for SNMP SET requests to set information on a network entity;
- public, router's community name;
- 192.168.0.0, IP address of the router;
- 1.3.6.1.2.1.1.5.0, SNMP value for router's identity;
SNMPset command above is equal to the RouterOS command,
/system identity set identity=New_Identity
Reboot
It's possible to reboot the router with SNMP set commamd, you need to set value for reboot SNMP settings, which is not equal to 0,
snmpset -c public -v 1 192.168.0.0 1.3.6.1.4.1.14988.1.1.7.1.0 s 1
- 1.3.6.1.4.1.14988.1.1.7.1.0, SNMP value for the router reboot;
- s 1, snmpset command to set value, value should not be equal to 0;
Reboot snmpset command is equal to the RouterOS command,
/system reboot
Run Script
SNMP write allows to run scripts on the router from system script menu, when you need to set value for SNMP setting of the script,
snmpset -c public -v 1 192.168.0.0 1.3.6.1.4.1.14988.1.1.8.1.1.3.X s 1
- X, script number, numeration starts from 1;
- s 1, snmpset command to set value, value should not be equal to 0;
The same command on RouterOS,
/system script> print Flags: I - invalid 0 name="kaka" owner="admin" policy=ftp,reboot,read,write,policy, test,winbox,password,sniff last-started=jan/01/1970 01:31:57 run-count=23 source=:beep /system script run 0
[ Top | Back to Content ]