Manual:Interface/Wireless
Wireless interface configuration
Basic settings
- master-interface (Text) : Name of wireless interface that has virtual-ap capability. Virtual AP interface will only work if master interface is in ap-bridge, bridge or wds-slave mode. This property is only for virtual AP interfaces.
- mode (One of station, station-wds, ap-bridge, bridge, alignment-only, nstreme-dual-slave, wds-slave, station-pseudobridge or station-pseudobridge-clone; default value: station) :
- Station modes:
- station - Basic station mode. Find and connect to acceptable AP.
- station-wds - Same as station, but create WDS link with AP, using proprietary extension. AP configuration has to allow WDS links with this device. Note that this mode does not use entries in wds.
- station-pseudobridge - Same as station, but additionally perform MAC address translation of all traffic. Allows interface to be bridged.
- station-pseudobridge-clone - Same as station-pseudobridge, but use station-bridge-clone-mac address to connect to AP.
- AP modes:
- ap-bridge - Basic access point mode.
- bridge - Same as ap-bridge, but limited to one associated client.
- wds-slave - Same as ap-bridge, but scan for AP with the same ssid and establishes WDS link. If this link is lost or cannot be established, then continue scanning. If dfs-mode is radar-detect, then APs with enabled hide-ssid will not be found during scanning.
- Special modes:
- alignment-only - Put interface in a continuous transmit mode that is used for aiming remote antenna.
- nstreme-dual-slave - allow this interface to be used in nstreme-dual setup.
- Station modes:
- MAC address translation in pseudobridge modes works by inspecting packets and building table of corresponding IP and MAC addresses. All packets are sent to AP with the MAC address used by pseudobridge, and MAC addresses of received packets are restored from the address translation table. There is single entry in address translation table for all non-IP packets, hence more than one host in the bridged network cannot reliably use non-IP protocols. Note: Currently IPv6 doesn't work over Pseudobridge
- Virtual AP interfaces do not have this property, they follow the mode of their master interface.
- ssid (Text, up to 32 characters long; default value is value of system/identity) : SSID (service set identifier) is a name that identifies wireless network.
- frequency (Frequency value in MHz) : Channel frequency on which AP will operate.
- Allowed values depend on selected band, and are restricted by country setting and wireless card capabilities.
- This setting has no effect if interface is in any of station modes, or in wds-slave mode, or if DFS is active.
- band (One of 2.4ghz-b, 5ghz, 5ghz-turbo, 2.4ghz-b/g, 2.4ghz-g-turbo, 5ghz-10mhz, 5ghz-5mhz, 2ghz-10mhz, 2ghz-5mhz, 5ghz-11n, 2ghz-11n, 2.4ghz-onlyg)
- scan-list (Comma separated list of frequencies and frequency ranges, or default) : The default value is all channels from selected band that are supported by card and allowed by the country and frequency-mode settings (this list can be seen in info). For default scan list in 5ghz band channels are taken with 20MHz step, in 5ghz-turbo band - with 40MHz step, for all other bands - with 5MHz step. If scan-list is specified manually, then all matching channels are taken. (Example: scan-list=default,5200-5245,2412-2427 - This will use the default value of scan list for current band, and add to it supported frequencies from 5200-5245 or 2412-2427 range.)
- antenna-mode (One of ant-a, ant-b, txa-rxb or rxa-txb) :
- ant-a - use only 'a' antenna
- ant-b - use only 'b' antenna
- txa-rxb - use antenna 'a' for transmitting, antenna 'b' for receiving
- rxa-txb - use antenna 'b' for transmitting, antenna 'a' for receiving
- wds-mode (One of disabled, static, dynamic, static-mesh or dynamic-mesh) : Controls how WDS links with other devices (APs and clients in station-wds mode) are established.
- disabled does not allow WDS links.
- static only allows WDS links that are manually configured in wds
- dynamic also allows WDS links with devices that are not configured in wds, by creating required entries dynamically. Such dynamic WDS entries are removed automatically after the connection with the other AP is lost.
- -mesh modes use different (better) method for establishing link between AP, that is not compatible with APs in non-mesh mode. This method avoids one-sided WDS links that are created only by one of the two APs. Such links cannot pass any data.
- When AP or station is establishing WDS connection with another AP, it uses connect-list to check whether this connection is allowed. If station in station-wds mode is establishing connection with AP, AP uses access-list to check whether this connection is allowed.
- If mode is station-wds, then this property has no effect.
- wds-default-bridge (none, or name of bridge interface) : When WDS link is established and status of the wds interface becomes running, it will be added as a bridge port to the bridge interface specified by this property. When WDS link is lost, wds interface is removed from the bridge. If wds interface is already included in a bridge setup when WDS link becomes active, it will not be added to bridge specified by , and will (needs editing)
- wds-ignore-ssid (yes or no; default value: no) : By default, WDS link between two APs can be created only when they work on the same frequency and have the same SSID value. If this property is set to yes, then SSID of the remote AP will not be checked. This property has no effect on connections from clients in station-wds mode. It also does not work if wds-mode is static-mesh or dynamic-mesh.
- default-authentication (yes or no, default value: yes) : For AP mode, this is the value of authentication for clients that do not match any entry in the access-list. For station mode, this is the value of connect for APs that do not match any entry in the connect-list.
- default-forwarding (yes or no; default value: yes) : This is the value of forwarding for clients that do not match any entry in the access-list.
- default-ap-tx-limit : This is the value of ap-tx-limit for clients that do not match any entry in the access-list.
- default-client-tx-limit : This is the value of client-tx-limit for clients that do not match any entry in the access-list.
- hide-ssid (yes or no; default value: no) :
- yes - AP does not include SSID the beacon frames, and does not reply to probe requests that have broadcast SSID.
- no - AP includes SSID in the beacon frames, and replies to probe requests that have broadcast SSID.
- This property has effect only in AP mode. Setting it to yes can remove this network from the list of wireless networks that are shown by some client software. Changing this setting does not improve security of the wireless network, because SSID is included in other frames sent by the AP.
- security-profile : Name of profile from security-profiles
- compression (yes or no; default value: no) : Setting this property to yes will allow use of the hardware compression. Wireless interface must have support for hardware compression. Connections with devices that do not use compression will still work.
- interface-type (virtual-AP, Prism, or Atheros XXXXXX, where XXXXXX is the type of Atheros device; read-only property) : This specifies type of wireless interface. Some properties have meaning only for certain types of interfaces.
Advanced settings
- frequency-mode (one of regulatory-domain, manual-txpower or superchannel) :
- regulatory-domain - Limit available channels and maximum transmit power for each channel according to the value of country
- manual-txpower - Same as above, but do not limit maximum transmit power.
- superchannel - Conformance Testing Mode. Allow all channels supported by the card.
- List of available channels for each band can be seen in /wireless info print. This mode allows you to test wireless channels outside the default scan-list and/or regulatory domain. This mode should only be used in controlled environments, or if you have a special permission to use it in your region. Before v4.3 this was called Custom Frequency Upgrade, or Superchannel. Since RouterOS v4.3 this mode is available without special key upgrades to all installations.
- country (either no_country_set, or name of a regulatory domain) : Limits available bands, frequencies and maximum transmit power for each frequency. Also specifies default value of scan-list. Value no_country_set is an FCC compliant set of channels.
- antenna-gain (default value: 0) : Antenna gain in dBi, used to calculate maximum transmit power according to country limitations.
| band | basic rates | supported rates |
|---|---|---|
| 2.4ghz-b | 1 | 1 .. 11 |
| 5ghz | 6 | 6 .. 54 |
| 2.4ghz-onlyg | 6 | 1 .. 11 and 6 .. 54 |
| 2.4ghz-b/g | 1 .. 11 | 1 .. 11 and 6 .. 54 |
| 2.4ghz-g-turbo | 6 | 6 .. 54 |
- rate-set (default or configured) :
- default - default basic and supported rate sets are used. Values from basic-rates and supported-rates parameters have no effect.
- configured - use values from basic-rates and supported-rates parameters. Note that g mode bands use rates from both "rates-b" and "rates-a/g" properties.
- supported-rates-b : List of supported rates, used for 2.4ghz-b, 2.4ghz-b/g and 2.4ghz-onlyg bands. Two devices will communicate only using rates that are supported by both devices. This property has effect only when value of rate-set is configured.
- supported-rates-a/g : Similar to the above property, but used for 5ghz, 5ghz-10mhz, 5ghz-5mhz, 5ghz-turbo, 2.4ghz-b/g, 2.4ghz-onlyg, 2ghz-10mhz, 2ghz-5mhz and 2.4ghz-g-turbo bands.
- basic-rates-b : List of basic rates, used for 2.4ghz-b, 2.4ghz-b/g and 2.4ghz-onlyg bands.
- Client will connect to AP only if it supports all basic rates announced by the AP.
- AP will establish WDS link only if it supports all basic rates of the other AP.
- This property has effect only in AP modes, and when value of rate-set is configured.
- basic-rates-a/g : Similar to the above property, but used for 5ghz, 5ghz-10mhz, 5ghz-5mhz, 5ghz-turbo, 2.4ghz-b/g, 2.4ghz-onlyg, 2ghz-10mhz, 2ghz-5mhz and 2.4ghz-g-turbo bands.
- max-station-count (1..2007; default value: 2007) : Maximum number of associated clients. WDS links also count toward this limit.
- ack-timeout (indoors, dynamic, or value in microseconds) : How long to wait for confirmation of unicast frames before considering transmission unsuccessful. Value 'dynamic' causes AP to detect and use smallest timeout that works with all connected clients.
- Acknowledgements are not used in Nstreme protocol.
- tx-power (value in the -30..30 range)
- tx-power-mode (one of default, all-rates-fixed, card-rates or manual-table) : (needs editing)
- dfs-mode (one of none, no-radar-detect and radar-detect; default value: none) : Controls DFS (Dynamic Frequency Selection).
- none - disables DFS.
- no-radar-detect - Select channel from scan-list with the lowest number of detected networks. In 'wds-slave' mode this setting has no effect.
- radar-detect - Select channel with the lowest number of detected networks and use it if no radar is detected on it for 60 seconds. Otherwise, select different channel. This setting may be required by the country regulations.
- This property has effect only in AP mode.
- wds-default-cost (number; default value: 100) : Initial bridge port cost of the WDS links.
- wds-cost-range (numeric range; default value: 50-150) : Bridge port cost of WDS links are automatically adjusted, depending on measured link throughput. Port cost is recalculated and adjusted every 5 seconds if it has changed by more than 10%, or if more than 20 seconds have passed since the last adjustment.
- Setting this property to 0 disables automatic cost adjustment.
- Automatic adjustment does not work for WDS links that are manually configured as a bridge port.
- wmm-support (disabled, enabled or required) : Specifies whether to enable WMM.
- disconnect-timeout (time interval in the 0..15s range, in units of 10ms; default value: 3s) : This interval is measured from third sending failure on the lowest data rate. At this point 3 * (hw-retries + 1) frame transmits on the lowest data rate had failed.
- During disconnect-timeout packet transmission will be retried with on-fail-retry-time interval. If no frame can be transmitted successfully during diconnect-timeout, connection is closed, and this event is logged as "extensive data loss". Successful frame transmission resets this timer.
- on-fail-retry-time (time interval in the 10ms..1s range, in 10ms units; default value: 100ms) : After third sending failure on the lowest data rate, wait for this long before retrying.
- frame-lifetime (time in hundredths of a second; default value: 0) : Discard frames that have been queued for sending longer than frame-lifetime. By default, when value of this property is 0, frames are discarded only after connection is closed.
- preamble-mode (one of long, short or both; default value: both) : Short preamble mode is an option of 802.11b standard that reduces per-frame overhead.
- On AP:
- long - Do not use short preamble.
- short - Announce short preamble capability. Do not accept connections from clients that do not have this capability.
- both - Announce short preamble capability.
- On station:
- long - do not use short preamble.
- short - do not connect to AP if it does not support short preamble.
- both - Use short preamble if AP supports it.
- On AP:
- allow-sharedkey (yes or no; default value: no) : Allow WEP Shared Key cilents to connect. Note that no authentication is done for these clients (WEP Shared keys are not compared to anything) - they are just accepted at once (if access list allows that).
- station-bridge-clone-mac (MAC address) : This property has effect only in the station-pseudobridge-clone mode.
- Use this MAC address when connection to AP. If this value is 00:00:00:00:00:00, station will initially use MAC address of the wireless interface.
- As soon as packet with MAC address of another device needs to be transmitted, station will reconnect to AP using that address.
- hw-retries (number 0..15; default value: 15) : Number of times sending frame is retried without considering it a transmission failure.
- Data rate is decreased upon failure and frame is sent again. Three sequential failures on lowest supported rate suspend transmission to this destination for the duration of on-fail-retry-time. After that, frame is sent again. The frame is being retransmitted until transmission success, or until client is disconnected after disconnect-timeout. Frame can be discarded during this time if frame-lifetime is exceeded.
- hw-fragmentation-threshold (integer 256..3000 | disabled;) : Specifies maximum fragment size in bytes when transmitted over wireless medium. 802.11 standard packet (MSDU in 802.11 terminology) fragmentation allows packets to be fragmented before transmiting over wireless medium to increase probability of successful transmission (only fragments that did not transmit correctly are retransmitted). Note that transmission of fragmented packet is less efficient than transmitting unfragmented packet because of protocol overhead and increased resource usage at both - transmitting and receiving party.
Frame protection support (RTS/CTS)
802.11 standard provides means to protect transmission against other device transmission by using RTS/CTS protocol. Frame protection helps to fight "hidden node" problem. There are several types of protection:
- RTS/CTS based protection - device willing to send frame at first sends RequestToSend frame and waits for ClearToSend frame from intended destination. By "seeing" RTS or CTS frame 802.11 compliant devices know that somebody is about to transmit and therefore do not initiate transmission themselves
- "CTS to self" based protection - device willing to send frame sends CTS frame "to itself". As in RTS/CTS protocol every 802.11 compliant device receiving this frame know not to transmit. "CTS to self" based protection has less overhead, but it must be taken into account that this only protects against devices receiving CTS frame (e.g. if there are 2 "hidden" stations, there is no use for them to use "CTS to self" protection, because they will not be able to receive CTS sent by other station - in this case stations must use RTS/CTS so that other station knows not to transmit by seeing CTS transmitted by AP).
Protection mode is controlled by hw-protection-mode setting of wireless interface. Possible values: none - for no protection (default), rts-cts for RTS/CTS based protection or cts-to-self for "CTS to self" based protection.
Frame size threshold at which protection should be used is controlled by hw-protection-threshold setting of wireless interface.
For example, to enable "CTS-to-self" based frame protection on AP for all frames, not depending on size, use command:
[admin@MikroTik] /interface wireless> set 0 hw-protection-mode=cts-to-self hw-protection-threshold=0
To enable RTS/CTS based protection on client use command:
[admin@MikroTik] /interface wireless> set 0 hw-protection-mode=rts-cts hw-protection-threshold=0
Proprietary extensions
- radio-name (text) : Descriptive name of the device, that is shown in registration table entries on the remote devices.
- This is a proprietary extension.
- area (text; default value is empty) : Identifies group of wireless networks. This value is announced by AP, and can be matched in connect-list by area-prefix.
- This is a proprietary extension.
- update-stats-interval (disabled or time interval in the 10s..5h range; default value: disabled) : How often to request update of signals strength and ccq values from clients.
- Access to registration-table also triggers update of these values.
- This is proprietary extension.
- proprietary-extensions (pre-2.9.25 or post-2.9.25; default value: post-2.9.25) : RouterOS includes proprietary information in an information element of management frames. This parameter controls how this information is included.
- pre-2.9.25 - This is older method. It can interoperate with newer versions of RouterOS. This method is incompatible with some clients, for example, Centrino based ones.
- post-2.9.25 - This uses standardized way of including vendor specific information, that is compatible with newer wireless clients.
Atheros specific
- noise-floor-threshold (default or value in the -128..127 range) : This property is only effective for cards based on AR5211 chipset.
- adaptive-noise-immunity (yes or no; default value: yes) : This property is only effective for cards based on Atheros chipset.
- periodic-calibration (one of default, enabled or disabled) : Setting default enables periodic calibration if info default-periodic-calibration property is enabled. Value of that property depends on the type of wireless card.
- This property is only effective for cards based on Atheros chipset.
- periodic-calibration-interval (value in range 1..10000; default value: 60) : This property is only effective for cards based on Atheros chipset.
Prism specific
- prism-cardtype (30mW, 100mW, 200mW) : Specify type of the installed wireless card.
802.11n specific
- ht-ampdu-priorities - frame priorities for which AMPDU sending (aggregating frames and sending using block acknowledgement) should get negotiated and used. Using AMPDUs will increase throughput, but may increase latency therefore may not be desirable for real-time traffic (voice, video). Due to this, by default AMPDUs are enabled only for best-effort traffic.
- ht-amsdu-limit - max AMSDU that device is allowed to prepare when negotiated. AMSDU aggregation may significantly increase throughput especially for small frames, but may increase latency in case of packet loss due to retransmission of aggregated frame. Sending and receiving AMSDUs will also increase CPU usage.
- ht-amsdu-threshold - max frame size to allow including in AMSDU.
- ht-basic-mcs - Modulation and Coding Schemes that every connecting client must support (refer to 802.11n for MCS specification).
- ht-supported-mcs - Modulation and Coding Schemes that this device advertises as supported.
- ht-extension-channel - wether to use additional 20MHz extension channel and if it should be located below or above control (main) channel. Extension channel allows 11n device to use 40MHz of spectrum in total thus increasing max throughput.
- ht-guard-interval - whether to allow use of short guard interval (refer to 802.11n MCS specification to see how this may affect throughput). "any" will use either short or long, depending on data rate, "long" will use long.
- ht-rxchains - which antennas to use for receive.
- ht-txchains - which antetnnas to use for transmit.
See also: 802.11n_Setup_Guide
Access lists
Access list is used by access point to restrict allowed connections from other devices, and to control connection parameters.
Operation
- Access list rules are checked sequentially.
- Disabled rules are always ignored.
- Only the first matching rule is applied.
- If there are no matching rules for the remote connection, then the default values from the wireless interface configuration are used.
- If remote device is matched by rule that has authentication=no value, the connection from that remote device is rejected.
Configuration
Access list configuration is located in /interface wireless access-list console path, and "Access List" tab in the WinBox "Wireless" window.
Match properties
- mac-address (default value: 00:00:00:00:00:00) : Rule matches client with the specified MAC address. Value 00:00:00:00:00:00 matches always.
- interface (Name of wireless interface, or all; default value: all) : Rules with interface=all are used for all wireless interfaces. To make rule that applies only to one wireless interface, specify that interface as a value of this property.
Match properties that also set connection parameters
- signal-range (NUM..NUM - both NUM are numbers in the range -120..120; default value: -120..120) : Rule matches if signal strength of the station is within the range.
- If signal strength of the station will go out of the range that is specified in the rule, access point will disconnect that station.
- time (TIME-TIME,sun,mon,tue,wed,thu,fri,sat - TIME is time interval 0..86400 seconds; all day names are optional; value can be unset; default value is not set) : Rule will match only during specified time.
- Station will be disconnected after specified time ends.
- Both start and end time is expressed as time since midnight, 00:00.
- Rule will match only during specified days of the week.
Connection properties
- authentication (yes or no) :
- no - Client association will always fail.
- yes - Use authentication procedure that is specified in the security-profile of the interface.
- forwarding (yes or no) :
- no - Client cannot send frames to other station that are connected to same access point.
- yes - Client can send frames to other stations on the same access point.
- ap-tx-limit (number, in bits per second; default value: 0) : Limit rate of data transmission to this client. Value 0 means no limit.
- client-tx-limit (number, in bits per second; default value: 0) : Ask client to limit rate of data transmission. Value 0 means no limit.
- This is a proprietary extension that is supported by RouterOS clients.
- private-algo (none, 40bit-wep, 104bit-wep, aes-ccm or tkip) : Only for WEP modes.
- private-key : Only for WEP modes.
- private-pre-shared-key : Used in WPA PSK mode.
Connect lists
connect-list is used to assign priority and security settings to connections with remote access points, and to restrict allowed connections.
connect-list is an ordered list of rules. Each rule in connect-list is attached to specific wireless interface, specified in the interface property of that rule (this is unlike access-list, where rules can apply to all interfaces).
Rule can match MAC address of remote access point, it's signal strength and many other parameters.
Operation
- connect-list rules are always checked sequentially, starting from the first.
- disabled rules are always ignored.
- Only the first matching rule is applied.
- If connect-list does not have any rule that matches remote access point, then the default values from the wireless interface configuration are used.
- If access point is matched by rule that has connect=no value, connection with this access point will not be attempted.
- If access point is matched by rule that has connect=yes value, connection with this access point will be attempted.
- In station mode, if several remote access points are matched by connect list rules with connect=yes value, connection will be attempted with access point that is matched by rule higher in the connect-list.
- If no remote access points are matched by connect-list rules with connect=yes value, then value of default-authentication interface property determines whether station will attempt to connect to any access point. If default-authentication=yes, station will choose access point with best signal and compatible security.
- In access point mode, connect-list is checked before establishing WDS link with remote device. If access point is not matched by any rule in the connect list, then the value of default-authentication determines whether WDS link will be established.
Usage
Restrict station connections only to specific access points
- Set value of default-authentication interface property to no.
/interface wireless set station-wlan default-authentication=no
- Create rules that matches allowed access points. These rules must have connect=yes and interface equal to the name of station wireless interface.
/interface wireless connect-list add interface=station-wlan connect=yes mac-address=00:11:22:33:00:01
/interface wireless connect-list add interface=station-wlan connect=yes mac-address=00:11:22:33:00:02
Disallow connections to specific access points
- Set value of default-authentication interface property to yes.
/interface wireless set station-wlan default-authentication=yes
- Create connect=no rules that match those access points that station should not connect to. These rules must have connect=no and interface equal to the name of station wireless interface.
/interface wireless connect-list add interface=station-wlan connect=no mac-address=00:11:22:33:44:55
Select preferred access points
- Create rules that match preferred access points. These rules must have connect=yes and interface equal to the name of station wireless interface.
- Put rules that match preferred access points higher in the connect-list, in the order of preference.
Restrict WDS link establishment
- Place rules that match allowed access points at the top.
- Add deny-all rule at the end of connect list.
Configuration Reference
Connect lists are configured under the /interface wireless connect-list path in the console, or in the "Connect List" tab of the "Wireless" window in the WinBox.
Match properties
- interface (name of wireless interface; required) : Each rule in connect list applies only to one wireless interface that is specified by this setting.
- area-prefix (text) : Rule matches if area value of AP (a proprietary extension) begins with value of area-prefix.
area value is a proprietary extension.
- mac-address (default value: 00:00:00:00:00:00) : Rule matches only AP with the specified MAC address. Value 00:00:00:00:00:00 matches always.
- ssid (text) : Rule matches access points that have this SSID. Empty value matches any SSID.
- This property has effect only when station mode interface ssid is empty, or when access point mode interface has wds-ignore-ssid=yes
Match properties that also set connection parameters
- signal-range (NUM..NUM - both NUM are numbers in the range -120..120) : Rule matches if signal strength of the access point is within the range.
- If station establishes connection to access point that is matched by this rule, it will disconnect from that access point when signal strength goes out of the specified range.
- security-profile (name of security-profile, or none) : Name of security profile that is used when connecting to matching access points, If value of this property is none, then security profile specified in the interface configuration will be used.
- In station mode, rule will match only access points that can support specified security profile. Value none will match access point that support security profile that is specified in the interface configuration. In access point mode value of this property will not be used to match remote devices.
Connection properties
- connect (yes or no) :
- yes - Connect to access point that matches this rule.
- no - Do not connect to any access point that matches this rule.
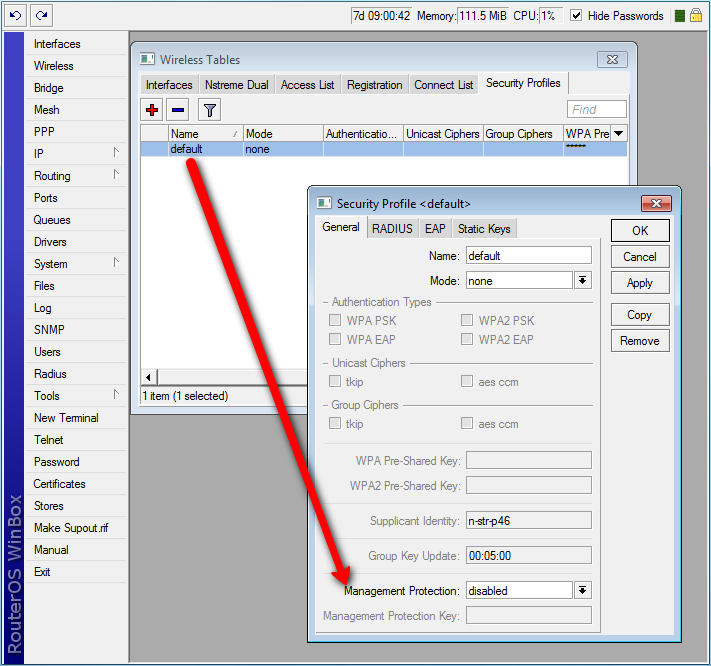
Security profiles
Security profiles are configured under the /interface wireless security-profiles path in the console, or in the "Security Profiles" tab of the "Wireless" window in the WinBox. Security profiles are referenced by the wireless interface security-profile parameter and security-profile parameter of the connect lists.
Basic properties
- mode (one of none, static-keys-optional, static-keys-required or dynamic-keys; default value: none) :
- none - Encryption is not used. Encrypted frames are not accepted.
- static-keys-required - WEP mode. Do not accept and do not send unencrypted frames.
Station in static-keys-required mode will not connect to an access point in static-keys-optional mode. - static-keys-optional - WEP mode. Support encryption and decryption, but allow also to receive and send unencrypted frames. Device will send unencrypted frames if encryption algorithm is specified as none.
Station in static-keys-optional mode will not connect to an access point in static-keys-required mode.
See also: static-sta-private-algo, static-transmit-key - dynamic-keys - WPA mode.
- name : see generic properties
WPA properties
These properties have effect only when mode=dynamic-keys.
- authentication-types (multiple choice of wpa-psk, wpa2-psk, wpa-eap and wpa2-eap; default value is empty) : Set of supported authentication types. Access point will advertise supported authentication types, and client will connect to access point only if supports any of the advertised authentication types.
- unicast-ciphers (multiple choice of tkip, aes-ccm; default value is empty) : Access point advertises that it supports specified ciphers. Client attempts connection only to access points that supports at least one of the specified ciphers.
- One of the ciphers will be used to encrypt unicast frames that are sent between access point and station.
- group-ciphers (multiple choice of tkip, aes-ccm; default value is empty) : Access point advertises one of these ciphers, and uses it to encrypt all broadcast and multicast frames. Client attempts connection only to access points that use one of the specified group ciphers.
- group-key-update (time interval in the 30s..1h range; default value: 5m) : Controls how often access point updates group key. This key is used to encrypt all broadcast and multicast frames.
- This property has no effect in station mode.
- wpa-pre-shared-key, wpa2-pre-shared-key (text) : WPA and WPA2 pre-shared key mode requires all devices in a BSS to have common secret key. Value of this key can be an arbitrary text.
RouterOS also allows to override pre-shared key value for specific clients, using either private-pre-shared-key property in the access-list, or the Mikrotik-Wireless-Psk attribute in the RADIUS MAC authentication response. This is an extension.
- These properties have effect only when authentication-types contains either wpa-psk or wpa2-psk.
wpa-pre-shared-key is used for wpa-psk authentication type. wpa2-pre-shared-key is used for wpa2-psk.
WPA EAP properties
These properties have effect only when authentication-types contains wpa-eap or wpa2-eap, and mode=dynamic-keys.
- eap-methods (array of eap-tls, passthrough) :
- eap-tls - Use built-in EAP TLS authentication. Both client and server certificates are supported. See description of tls-mode and tls-certificate properties.
- passthrough - Access point will relay authentication process to the RADIUS server. This value is ignored in station mode.
- Order of values is significant for access point configuration, it is used by access point when offering specified methods to clients.
- Example: Access point uses security-profile where eap-methods=eap-tls,passthrough:
- Access point offers EAP-TLS method to the client.
- Client refuses.
- Access point starts relaying EAP communication to the radius server.
- supplicant-identity (text; default value is same as system/identity of router at the moment of profile creation) : EAP identity that is sent by client at the beginning of EAP authentication. This value is used as a value for User-Name attribute in RADIUS messages sent by RADIUS EAP accounting and RADIUS EAP pass-through authentication.
- tls-mode (one of verify-certificate, dont-verify-certificate, no-certificates; default value: no-certificates) :
- verify-certificate - Require remote device to have valid certificate. Check that it is signed by known certificate authority. No additional identity verification is done.
Note: Certificate may include information about time period during which it is valid. If router has incorrect time and date, it may reject valid certificate because router's clock is outside that period.
See also: certificate configuration. - dont-verify-certificate - Do not check certificate of the remote device. Access point will not require client to provide certificate.
- no-certificates - Do not use certificates. TLS session is established using 2048 bit anonymous Diffie-Hellman key exchange.
- verify-certificate - Require remote device to have valid certificate. Check that it is signed by known certificate authority. No additional identity verification is done.
- When using first two modes, remote device has to support one of the "RC4-MD5", "RC4-SHA" or "DES-CBC3-SHA" TLS cipher suites. In the last mode remote device must support "ADH-DES-CBC3-SHA" cipher suite.
- This property has effect only when eap-methods contains eap-tls.
- tls-certificate (none or name of certificate; default value: none) : Access point always needs certificate when configured with tls-mode=verify-certificate, or tls-mode=dont-verify-certificate. Client needs certificate only if access point is configured with tls-mode=verify-certificate. In this case client needs valid certificate that is signed by CA known to the access point.
- This property has effect only if tls-mode≠no-certificates.
- This property has effect only when eap-methods contains eap-tls.
RADIUS properties
- radius-mac-authentication (yes or no; default value: no) : This property affects the way how access point processes clients that are not found in the access-list.
- no - allow or reject client authentication based on the value of default-authentication property of the wireless interface.
- yes - Query RADIUS server using MAC address of client as user name. With this setting the value of default-authentication has no effect.
- radius-mac-accounting (yes or no; default value: no) : (needs editing)
- radius-eap-accounting (yes or no; default value: no) : (needs editing)
- interim-update (time interval; default value: 0) : When RADIUS accounting is used, access point periodically sends accounting information updates to the RADIUS server. This property specifies default update interval that can be overridden by the RADIUS server using Acct-Interim-Interval attribute.
- radius-mac-format (one of XX:XX:XX:XX:XX:XX, XXXX:XXXX:XXXX, XXXXXX:XXXXXX, XX-XX-XX-XX-XX-XX, XXXXXX-XXXXXX, XXXXXXXXXXXX, XX XX XX XX XX XX; default value: XX:XX:XX:XX:XX:XX) : Controls how MAC address of the client is encoded by access point in the User-Name attribute of the MAC authentication and MAC accounting RADIUS requests.
- radius-mac-mode (one of as-username, as-username-and-password; default value: as-username) : By default access point uses empty password, when sending Access-Request during MAC authentication. When this property is set to as-username-and-password, access point will use the same value for User-Password attribute as for the User-Name attribute.
- radius-mac-caching (either disabled or time interval; default value: disabled) : If this value is set to time interval, the access point will cache RADIUS MAC authentication responses for specified time, and will not contact RADIUS server if matching cache entry already exists. Value disabled will disable cache, access point will always contact RADIUS server.
WEP properties
These properties have effect only when mode is static-keys-required or static-keys-optional. See section "Statically configured WEP keys".
- static-key-0, static-key-1, static-key-2, static-key-3 (hexadecimal representation of the key. Length of key must be appropriate for selected algorithm - see section "Statically configured WEP keys; default value is empty) : (needs editing)
- static-algo-0, static-algo-1, static-algo-2, static-algo-3 (one of none, 40bit-wep, 104bit-wep, tkip or aes-ccm; default value: none) : Encryption algorithm to use with the corresponding key.
- static-transmit-key (one of key-0, key-1, key-2 or key-3; default value: key-0) : Access point will use the specified key to encrypt frames for clients that do not use private key. Access point will also use this key to encrypt broadcast and multicast frames.
- Client will use the specified key to encrypt frames if static-sta-private-algo=none.
- If corresponding static-algo- property has value none, frame will be sent unencrypted (when mode=static-keys-optional) or will not be sent at all (when mode=static-keys-required).
- static-sta-private-key (hexadecimal representation of the key. Length of key must be appropriate for selected algorithm - see section "Statically configured WEP keys") : This property is used only in station mode. Access point uses corresponding key either from private-key property of access-list, or from Mikrotik-Wireless-Enc-Key attribute in RADIUS Access-Accept MAC authentication response.
- static-sta-private-algo (one of none, 40bit-wep, 104bit-wep, tkip or aes-ccm) : Encryption algorithm to use with station private key. Value none disables use of the private key.
- This property is used only in station mode. Access point has to get corresponding value either from private-algo property of access-list, or from Mikrotik-Wireless-Enc-Algo attribute in RADIUS Access-Accept MAC authentication response.
- Station private key replaces key 0 for unicast frames. Station will not use private key to decrypt broadcast frames.
Management frame protection
Used for: Deauthentication attack prevention, MAC address cloning issue.
RouterOS implements proprietary management frame protection algorithm based on shared secret. Management frame protection means that RouterOS wireless device is able to verify source of management frame and confirm that particular frame is not malicious. This feature allows to withstand deauthentication and disassociation attacks on RouterOS based wireless devices.
Management protection mode is configured in security-profile with management-protection setting. Possible values are: disabled - management protection is disabled (default), allowed - use management protection if supported by remote party (for AP - allow both, non-management protection and management protection clients, for client - connect both to APs with and without management protection), required - establish association only with remote devices that support management protection (for AP - accept only clients that support management protection, for client - connect only to APs that support management protection).
Management protection shared secret is configured with security-profile management-protection-key setting.
When interface is in AP mode, default management protection key (configured in security-profile) can be overridded by key specified in access-list or RADIUS attribute.
[admin@mikrotik] /interface wireless security-profiles> print 0 name="default" mode=none authentication-types="" unicast-ciphers="" group-ciphers="" wpa-pre-shared-key="" wpa2-pre-shared-key="" supplicant-identity="n-str-p46" eap-methods=passthrough tls-mode=no-certificates tls-certificate=none static-algo-0=none static-key-0="" static-algo-1=none static-key-1="" static-algo-2=none static-key-2="" static-algo-3=none static-key-3="" static-transmit-key=key-0 static-sta-private-algo=none static-sta-private-key="" radius-mac-authentication=no radius-mac-accounting=no radius-eap-accounting=no interim-update=0s radius-mac-format=XX:XX:XX:XX:XX:XX radius-mac-mode=as-username radius-mac-caching=disabled group-key-update=5m management-protection=disabled management-protection-key=""
[admin@mikrotik] /interface wireless security-profiles> set default management-protection=
allowed disabled required
Operation details
RADIUS MAC authentication
Note: RAIDUS MAC authentication is used by access point for clients that are not found in the access-list, similarly to the default-authentication property of the wireless interface. It controls whether client is allowed to proceed with authentication, or is rejected immediately.
When radius-mac-authentication=yes, access point queries RADIUS server by sending Access-Request with the following attributes:
- User-Name - Client MAC address. This is encoded as specified by the radius-mac-format setting. Default encoding is "XX:XX:XX:XX:XX:XX".
- Nas-Port-Id - name of wireless interface.
- User-Password - When radius-mac-mode=as-username-and-password this is set to the same value as User-Name. Otherwise this attribute is empty.
- Calling-Station-Id - Client MAC address, encoded as "XX-XX-XX-XX-XX-XX".
- Called-Station-Id - MAC address and SSID of the access point, encoded as "XX-XX-XX-XX-XX-XX:SSID" (minus separated pairs of MAC address digits, followed by colon, followed by SSID value).
- Acct-Session-Id - Added when radius-mac-accounting=yes.
When access point receives Access-Accept or Access-Reject response from the RADIUS server, it stores the response and either allows or rejects client. Access point uses following RADIUS attributes from the Access-Accept response:
- Ascend-Data-Rate
- Ascend-Xmit-Rate
- Mikrotik-Wireless-Forward - Same as access-list forwarding.
- Mikrotik-Wireless-Enc-Algo - Same as access-list private-algo.
- Mikrotik-Wireless-Enc-Key - Same as access-list private-key.
- Mikrotik-Wireless-Psk - Same as access-list private-pre-shared-key.
- Session-Timeout - Time, after which client will be disconnected.
- Acct-Interim-Interval - Overrides value of interim-update.
- Class - If present, value of this attribute is saved and included in Accounting-Request messages.
Caching
Caching of RADIUS MAC authentication was added to support RADIUS authentication for clients that require from the access point very quick response to the association request. Such clients time out before response from RADIUS server is received. Access point caches authentication response for some time and can immediately reply to the repeated association request from the same client.
RADIUS EAP pass-through authentication
When using WPA EAP authentication type, clients that have passed MAC authentication are required to perform EAP authentication before being authorized to pass data on wireless network. With pass-through EAP method the access point will relay authentication to RADIUS server, and use following attributes in the Access-Request RADIUS message:
- User-Name - EAP supplicant identity. This value is configured in the supplicant-identity property of the client security profile.
- Nas-Port-Id - name of wireless interface.
- Calling-Station-Id - Client MAC address, encoded as "XX-XX-XX-XX-XX-XX".
- Called-Station-Id - MAC address and SSID of the access point, encoded as "XX-XX-XX-XX-XX-XX:SSID" (pairs of MAC address digits separated by minus sign, followed by colon, followed by SSID value).
- Acct-Session-Id - Added when radius-eap-accounting=yes.
- Acct-Multi-Session-Id - MAC address of access point and client, and unique 8 byte value, that is shared for all accounting sessions that share single EAP authentication. Encoded as AA-AA-AA-AA-AA-AA-CC-CC-CC-CC-CC-CC-XX-XX-XX-XX-XX-XX-XX-XX.
- Added when radius-eap-accounting=yes.
Access point uses following RADIUS attributes from the Access-Accept server response:
- Class - If present, value of this attribute is saved and included in Accounting-Request messages.
- Session-Timeout - Time, after which client will be disconnected. Additionally, access point will remember authentication result, and if during this time client reconnects, it will be authorized immediately, without repeating EAP authentication.
- Acct-Interim-Interval - Overrides value of interim-update.
Statically configured WEP keys
Different algorithms require different length of keys:
- 40bit-wep - 10 hexadecimal digits (40 bits). If key is longer, only first 40 bits are used.
- 104bit-wep - 26 hexadecimal digits (104 bits). If key is longer, only first 104 bits are used.
- tkip - At least 64 hexadecimal digits (256 bits).
- aes-ccm - At least 32 hexadecimal digits (128 bits).
Key must contain even number of hexadecimal digits.
WDS security configuration
WDS links can use all available security features. However, they require careful configuration of security parameters.
It is possible to use one security profile for all clients, and different security profiles for WDS links. Security profile for WDS link is specified in connect-list. Access point always checks connect list before establishing WDS link with another access point, and used security settings from matching connect list entry. WDS link will work when each access point will have connect list entry that matches the other device, has connect=yes and specifies compatible security-profile.
WDS and WPA/WPA2
If access point uses security profile with mode=dynamic-keys, then encryption will be used for all WDS links. Since WPA authentication and key exchange is not symmetrical, one of the access points will act as a client for the purpose of establishing secure connection. This is similar to how static-mesh and dynamic-mesh WDS modes work. Some problems, like single sided WDS link between two incorrectly configured access points that use non-mesh mode, is not possible if WPA encryption is enabled. However, non-mesh modes with WPA still have other issues (like constant reconnection attempts in case of configuration mismatch) that are solved by use of the -mesh WDS modes.
In general, WPA properties on both access points that establish WPA protected WDS link have to match. These properties are authentication-types, unicast-ciphers, group-ciphers. For non-mesh WDS mode these properties need to have the same values on both devices. In mesh WDS mode each access point has to support the other one as a client.
Theoretically it is possible to use RADIUS MAC authentication and other RADIUS services with WDS links. However, only one access point will interact with the RADIUS server, the other access point will behave as a client.
Implementation of eap-tls EAP method in RouterOS is particularly well suited for WDS link encryption. tls-mode=no-certificates requires no additional configuration, and provides very strong encryption.
WDS and WEP
mode, static-sta-private-key and static-sta-private-algo parameters in the security profile assigned to the WDS link need to have the same values on both access points that establish WDS link with WPA encryption.
Security profile and access point matching in the connect list
Client uses value of connect-list security-profile property to match only those access points that support necessary security.
- mode=static-keys-required and mode=static-keys-optional matches only access points with the same mode in interface security-profile.
- If mode=dynamic-keys, then connect list entry matches if all of the authentication-types, unicast-ciphers and group-ciphers contain at least one value that is advertised by access point.