Manual:CRS3xx VLANs with Bonds
Summary
This page will show how to configure multiple switches to use bonding interfaces and port based VLANs, it will also show a working example with a DHCP-Server, interVLAN routing, management IP and invalid VLAN filtering configuration.
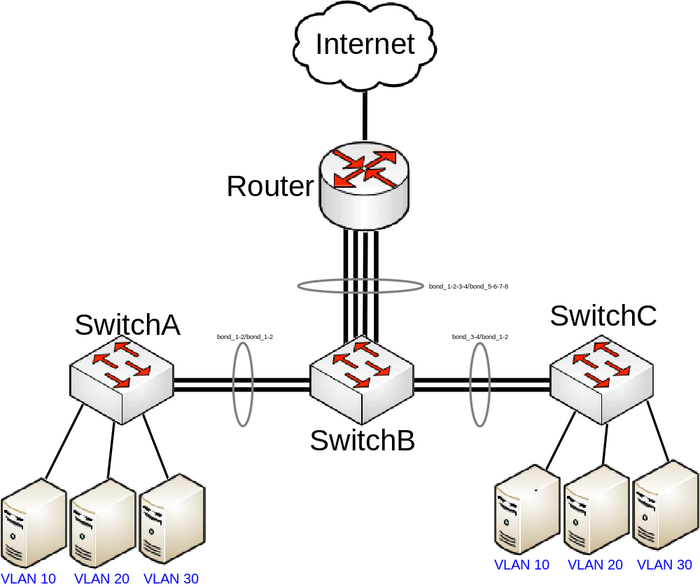

Note: For this network topology we will be using two CRS326-24G-2S+, one CRS317-1G-16S+ and one CCR1072-1G-8S+, but same principles can be applied to any CRS3xx series devices and a router.
In this setup SwitchA and SwitchC will tag all traffic from ports ether1-ether8 to VLAN ID 10, ether9-ether16 to VLAN ID 20, ether17-ether24 to VLAN ID 30. Management will only be possible if user is connecting with tagged traffic with VLAN ID 99 from ether1 on SwitchA or SwitchB, connecting to all devices will also be possible from the router using tagged traffic with VLAN ID 99. SFP+ ports in this setup are going to be used as VLAN trunk ports while being in a bond to create a LAG interface.
Port switching
All switches in this setup require that all used ports are switched together (except for ports that are going to be part of a bonding interface). Use these commands on SwitchA and SwitchC:
/interface bridge add name=bridge vlan-filtering=no /interface bridge port add bridge=bridge hw=yes interface=ether1 add bridge=bridge hw=yes interface=ether2 add bridge=bridge hw=yes interface=ether3 add bridge=bridge hw=yes interface=ether4 add bridge=bridge hw=yes interface=ether5 add bridge=bridge hw=yes interface=ether6 add bridge=bridge hw=yes interface=ether7 add bridge=bridge hw=yes interface=ether8 add bridge=bridge hw=yes interface=ether9 add bridge=bridge hw=yes interface=ether10 add bridge=bridge hw=yes interface=ether11 add bridge=bridge hw=yes interface=ether12 add bridge=bridge hw=yes interface=ether13 add bridge=bridge hw=yes interface=ether14 add bridge=bridge hw=yes interface=ether15 add bridge=bridge hw=yes interface=ether16 add bridge=bridge hw=yes interface=ether17 add bridge=bridge hw=yes interface=ether18 add bridge=bridge hw=yes interface=ether19 add bridge=bridge hw=yes interface=ether20 add bridge=bridge hw=yes interface=ether21 add bridge=bridge hw=yes interface=ether22 add bridge=bridge hw=yes interface=ether23 add bridge=bridge hw=yes interface=ether24

Note: If required, it is possible to use STP/RSTP/MSTP and IGMP Snooping with hardware offloading, make sure your device supports it.
Bonding
Bonding interfaces are used when a larger amount of bandwidth is required, this is done by creating a link aggregation group, which also provides hardware automatic failover and load balancing for CRS3xx series switches. By adding two 10Gbps interfaces to a bonding, you can increase the theoretical bandwidth limit to 20Gbps. Make sure that all bonded interfaces are linked to the same speed rates.

Note: CRS3xx series switches aggregate traffic using the built-in Switch Chip without using CPU resources, to route the traffic a router with a powerful CPU is required to handle the aggregated traffic.
To create a 20Gbps bonding interface from sfp-sfpplus1 and sfp-sfpplus2 between SwitchA to SwitchB and between SwitchC to SwitchB, use these commands on SwitchA and SwitchC:
/interface bonding add mode=802.3ad name=bond_1-2 slaves=sfp-sfpplus1,sfp-sfpplus2
To create a 40Gbps bonding interface between SwitchB and the Router and 20Gbps bonding interfaces between SwitchA and SwitchC, use these commands on SwitchB:
/interface bonding add mode=802.3ad name=bond_1-2 slaves=sfp-sfpplus1,sfp-sfpplus2 add mode=802.3ad name=bond_3-4 slaves=sfp-sfpplus3,sfp-sfpplus4 add mode=802.3ad name=bond_5-6-7-8 slaves=sfp-sfpplus5,sfp-sfpplus6,sfp-sfpplus7,sfp-sfpplus8
When all the bonding interfaces are create, they must be added as a bridge port. Use these commands on SwitchA and SwitchB:
/interface bridge port add bridge=bridge interface=bond_1-2
Add all bonding interfaces to a single bridge on SwitchB by using these commands on SwitchB:
/interface bridge port add bridge=bridge interface=bond_1-2 add bridge=bridge interface=bond_3-4 add bridge=bridge interface=bond_5-6-7-8
In our case the Router needs a software based bonding interface, use these commands on Router:
/interface bonding add mode=802.3ad name=bond_1-2-3-4 slaves=sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3,sfp-sfpplus4
Management IP
It is very useful to create a management interface and assign an IP address to it in order to preserve access to the switch. This is also very useful when updating your switches since such traffic to the switch will be blocked when enabling invalid VLAN filtering.
Create a VLAN interface on SwitchA, SwitchB, SwitchC:
/interface vlan add interface=ether1 name=Vlan99 vlan-id=99

Note: VLAN interface must be created on the master-port interface since it is the only interface that will be able to communicate the CPU.
For this guide we are going to use these addresses for each device:
| Address | Device |
|---|---|
| 192.168.99.1 | Router |
| 192.168.99.2 | SwitchA |
| 192.168.99.3 | SwitchB |
| 192.168.99.4 | SwitchC |
Add an IP address for each device on the VLAN interface (change X to appropriate number):
/ip address add address=192.168.99.X/24 interface=Vlan99
Don't forget to add the default gateway and specify a DNS server:
/ip route add gateway=192.168.99.1 /ip dns set servers=192.168.99.1
Add the IP address on the Router:
/ip address add address=192.168.99.1/24 interface=Vlan99
Port based VLAN
When using port trunks, the main difference is that access ports are now trunk ports and they should be used in the Egress VLAN tag table, Ingress VLAN translation table and VLAN table instead of physical Ethernet interfaces.
To create each trunk port as access port, use these commands on SwitchA and SwitchC:
/interface ethernet switch egress-vlan-tag add tagged-ports=trunk-1-2 vlan-id=10 add tagged-ports=trunk-1-2 vlan-id=20 add tagged-ports=trunk-1-2 vlan-id=30 add tagged-ports=trunk-1-2 vlan-id=40
Similarly add entries to the Egress VLAN tag table for SwitchB, use these commands on SwitchB:
/interface ethernet switch egress-vlan-tag add tagged-ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8 vlan-id=10 add tagged-ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8 vlan-id=20 add tagged-ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8 vlan-id=30 add tagged-ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8 vlan-id=40

Note: Management VLAN ID is not addedd to Egress VLAN tag table since a VLAN interface has been already created that will only send out tagged traffic either way.
Specify for each Ethernet interface a VLAN ID that will be assigned for a device that uses the port, use these commands for SwitchA and SwitchC:
/interface ethernet switch ingress-vlan-translation add new-customer-vid=10 ports=ether3,ether4,ether5,ether6 add new-customer-vid=20 ports=ether7,ether8,ether9,ether10,ether11,ether12 add new-customer-vid=30 ports=ether13,ether14,ether15,ether16,ether17,ether18 add new-customer-vid=40 ports=ether19,ether20,ether21,ether22,ether23,ether24
Similarly specify a VLAN ID for each Ethernet interface on SwitchB, use these commands on SwitchB:
/interface ethernet switch ingress-vlan-translation add new-customer-vid=10 ports=ether9,ether10,ether11,ether12 add new-customer-vid=20 ports=ether13,ether14,ether15,ether16 add new-customer-vid=30 ports=ether17,ether18,ether19,ether20 add new-customer-vid=40 ports=ether21,ether22,ether23,ether24
It is required add allowed VLAN IDs to the VLAN table in order for VLAN filtering to work properly. Specify each VLAN ID and each port that is allowed to forward a certain VLAN ID. Use trunk ports instead of physical Ethernet interfaces. Use these commands on SwitchA and SwitchC:
/interface ethernet switch vlan add ports=trunk-1-2,ether3,ether4,ether5,ether6 vlan-id=10 add ports=trunk-1-2,ether7,ether8,ether9,ether10,ether11,ether12 vlan-id=20 add ports=trunk-1-2,ether13,ether14,ether15,ether16,ether17,ether18 vlan-id=30 add ports=trunk-1-2,ether19,ether20,ether21,ether22,ether23,ether24 vlan-id=40 add ports=trunk-1-2,switch1-cpu vlan-id=99
Similarly add entries to the VLAN table for SwitchB, use the commands on SwitchB:
/interface ethernet switch vlan add ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8,ether9,ether10,ether11,ether12 vlan-id=10 add ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8,ether13,ether14,ether15,ether16 vlan-id=20 add ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8,ether17,ether18,ether19,ether20 vlan-id=30 add ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8,ether21,ether22,ether23,ether24 vlan-id=40 add ports=trunk-1-2-3-4,trunk-5-6,trunk-7-8,switch1-cpu vlan-id=99

Note: It is required to specify switch1-cpu port in the VLAN table in order to allow access the the previously created VLAN interface for management purposes.
Invalid VLAN filtering
If ingress VLAN translation table, egress VLAN tag table and VLAN table is properly set, invalid VLAN filtering can be enabled, which will drop any other packet that does not a suitable entry in the VLAN table.

Warning: Double check if port based VLAN is set up properly. If a mistake was made, you might loose access to the switch and can only be regained by resetting configuration or using the serial console.
To enable invalid VLAN filtering, use these commands on SwitchA, SwitchB, SwitchC:
/interface ethernet switch set drop-if-invalid-or-src-port-not-member-of-vlan-on-ports="ether1,ether2,ether3,ether4\ ,ether5,ether6,ether7,ether8,ether9,ether10,ether11,ether12,ether13\ ,ether14,ether15,ether16,ether17,ether18,ether19,ether20,ether21,ether22,ether23,ether24"
InterVLAN routing
To create InterVLAN routing, VLAN interface for each customer VLAN ID must be created on the router and must have an IP address assigned to it. The VLAN interface must be created on the bonding interface created previously.
Use these commands on the Router:
/interface vlan add interface=bond1 name=Vlan10 vlan-id=10 add interface=bond1 name=Vlan20 vlan-id=20 add interface=bond1 name=Vlan30 vlan-id=30 add interface=bond1 name=Vlan40 vlan-id=40 /ip address add address=192.168.10.1/24 interface=Vlan10 add address=192.168.20.1/24 interface=Vlan20 add address=192.168.30.1/24 interface=Vlan30 add address=192.168.40.1/24 interface=Vlan40

Note: These commands are required for DHCP-Server. In case interVLAN routing is not desired but a DHCP-Server on a single router is required, then use Firewall Filter to block access between different subnets.
DHCP-Server
To get the DHCP-Server working for each VLAN ID, the server must be set up on the previously created VLAN interfaces (one server for each VLAN ID). Preferably each VLAN ID should have its own subnet and its own IP pool. DNS Server could be specified as the router's IP address for particular VLAN ID or a global DNS Server could be used, but this address must be reachable.
To set up the DHCP-Server, use these commands on the Router:
/ip pool add name=Vlan10_pool ranges=192.168.10.100-192.168.10.200 add name=Vlan20_pool ranges=192.168.20.100-192.168.20.200 add name=Vlan30_pool ranges=192.168.30.100-192.168.30.200 add name=Vlan40_pool ranges=192.168.40.100-192.168.40.200 /ip dhcp-server add address-pool=Vlan10_pool disabled=no interface=Vlan10 name=Vlan10_DHCP add address-pool=Vlan20_pool disabled=no interface=Vlan20 name=Vlan20_DHCP add address-pool=Vlan30_pool disabled=no interface=Vlan30 name=Vlan30_DHCP add address-pool=Vlan40_pool disabled=no interface=Vlan40 name=Vlan40_DHCP /ip dhcp-server network add address=192.168.10.0/24 dns-server=192.168.10.1 gateway=192.168.10.1 add address=192.168.20.0/24 dns-server=192.168.20.1 gateway=192.168.20.1 add address=192.168.30.0/24 dns-server=192.168.30.1 gateway=192.168.30.1 add address=192.168.40.0/24 dns-server=192.168.40.1 gateway=192.168.40.1
In case the router's DNS Server is being used, don't forget to allow remote requests and make sure DNS Servers are configured on the router. Use these commands on the Router:
/ip dns set allow-remote-requests=yes servers=8.8.8.8

Warning: Make sure to secure your local DNS Server with Firewall from the outside when using allow-remote-requests set to yes since your DNS Server can be used for DDoS attacks if it is accessible from the Internet by anyone.
Don't forget to create NAT, assuming that sfp-sfpplus1 is used as WAN port, use these commands on the Router:
/ip firewall nat add action=masquerade chain=srcnat out-interface=sfp-sfpplus1
Jumbo frames
One can increase the total throughput in such a setup by enabling jumbo frames. This reduces the packet overhead by increasing the Maximum Transmission Unit (MTU). If a device in your network does not support jumbo frames, then it will not benefit from a larger MTU. Usually the whole network does not support jumbo frames, but you can still benefit when sending data between devices that support jumbo frames, including all switches in the path.
In this case, if clients behind SwitchA and client behind SwitchC supports jumbo frames, then enabling jumbo frames will be beneficial. Before enabling jumbo frames, determine the MAX-L2MTU by using this command:
[admin@MikroTik] > /interface> print Flags: D - dynamic, X - disabled, R - running, S - slave # NAME TYPE ACTUAL-MTU L2MTU MAX-L2MTU 0 R ether1 ether 1500 1580 4064

Note: More information can be found in MTU manual page.
When MAX-L2MTU is determined, choose the MTU size depending on the traffic on your network, use this command on SwitchA, SwitchB and SwitchC:
/interface ethernet set [ find ] l2mtu=4064 mtu=4040

Note: Don't forget to change the MTU on your client devices too, otherwise above mentioned settings will not have any effect.
