Manual:IP/IPsec
Summary
Sub-menu: /ip ipsec
Package required: security
Standards: RFC 4301
Internet Protocol Security (IPsec) is a set of protocols defined by the Internet Engineering Task Force (IETF) to secure packet exchange over IP network.
IpSec protocol suite can be divided in following groups:
- Authentication Header (AH) RFC 4302
- Encapsulating Security Payload (ESP) RFC 4303
- Internet Key Exchange (IKE) protocols. Dynamically generates and distributes cryptographic keys for AH and ESP.
- Manual Keys. ESP and AH cryptography keys are static and manually distributed. Manual keys should be used when remote peer does not IKE.
Authentication Header (AH)
AH is a protocol that provides authentication of either all or part of the contents of a datagram through the addition of a header that is calculated based on the values in the datagram. What parts of the datagram are used for the calculation, and the placement of the header, depends whether tunnel or transport mode is used.
The presence of the AH header allows to verify the integrity of the message, but doesn't encrypt it. Thus, AH provides authentication but not privacy (Another protocol ESP is used to provide encryption).
RouterOS supports the following authentication algorithms for AH:
- SHA1
- MD5
Transport mode
In transport mode AH header is inserted after IP header. IP data and header is used to calculate authentication value. IP fields that might change during transit, like TTL and hop count, are set to zero values before authentication.
Tunnel mode
In tunnel mode original IP packet is encapsulated within a new IP packet. All of the original IP packet is authenticated.
Encapsulating Security Payload (ESP)
Encapsulating Security Payload (ESP) uses shared key encryption to provide data privacy. ESP also supports its own authentication scheme like that used in AH, or can be used in conjunction with AH.
ESP packages its fields in a very different way than AS. Instead of having just a header, it divides its fields into three components:
- ESP Header - Comes before the encrypted data and its placement depends on whether ESP is used in transport mode or tunnel mode.
- ESP Trailer - This section is placed after the encrypted data. It contains padding that is used to align the encrypted data.
- ESP Authentication Data - This field contains an Integrity Check Value (ICV), computed in a manner similar to how the AH protocol works, for when ESP's optional authentication feature is used.
Transport mode
In transport mode ESP header is inserted after original IP header. ESP traler and authentication value is added to the end of the packet. In this mode only IP payload is encrypted and authenticated, IP header is not secured.
Tunnel mode
In tunnel mode original IP packet is encapsulated within a new IP packet thus securing IP payload and IP header.
Encryption algorithms
RouterOS ESP supports various encryption and authentication algorithms.
Authentication:
- SHA1
- MD5
Encryption:
- DES - 56-bit DES-CBC encryption algorithm;
- 3DES - 168-bit DES encryption algorithm;
- AES - 128, 192 and 256-bit key AES-CBC encryption algorithm;
- Blowfish - added since v4.5
- Twofish - added since v4.5
- Camellia - 128, 192 and 256-bit key Camellia encryption algorithm added since v4.5
Internet Key Exchange (IKE)
The Internet Key Exchange (IKE) is a protocol that provides authenticated keying material for Internet Security Association and Key Management Protocol (ISAKMP) framework. There are other key exchange schemes that work with ISAKMP, but IKE is the most widely used one. Together they provide means for authentication of hosts and automatic management of security associations (SA).
Most of the time IKE daemon is doing nothing. There are two possible situations when it is activated:
There is some traffic caught by a policy rule which needs to become encrypted or authenticated, but the policy doesn't have any SAs. The policy notifies IKE daemon about that, and IKE daemon initiates connection to remote host. IKE daemon responds to remote connection. In both cases, peers establish connection and execute 2 phases:
- Phase 1 - The peers agree upon algorithms they will use in the following IKE messages and authenticate. The keying material used to derive keys for all SAs and to protect following ISAKMP exchanges between hosts is generated also.
- Phase 2 - The peers establish one or more SAs that will be used by IPsec to encrypt data. All SAs established by IKE daemon will have lifetime values (either limiting time, after which SA will become invalid, or amount of data that can be encrypted by this SA, or both).
There are two lifetime values - soft and hard. When SA reaches it's soft lifetime treshold, the IKE daemon receives a notice and starts another phase 2 exchange to replace this SA with fresh one. If SA reaches hard lifetime, it is discarded.
IKE can optionally provide a Perfect Forward Secrecy (PFS), which is a property of key exchanges, that, in turn, means for IKE that compromising the long term phase 1 key will not allow to easily gain access to all IPsec data that is protected by SAs established through this phase 1. It means an additional keying material is generated for each phase 2.
Generation of keying material is computationally very expensive. Exempli gratia, the use of modp8192 group can take several seconds even on very fast computer. It usually takes place once per phase 1 exchange, which happens only once between any host pair and then is kept for long time. PFS adds this expensive operation also to each phase 2 exchange.
Diffie-Hellman Groups
Diffie-Hellman (DH) key exchange protocol allows two parties without any initial shared secret to create one securely. The following Modular Exponential (MODP) and Elliptic Curve (EC2N) Diffie-Hellman (also known as "Oakley") Groups are supported:
| Diffie-Hellman Group | Name | Reference |
| Group 1 | 768 bit MODP group | RFC 2409 |
| Group 2 | 1024 bits MODP group | RFC 2409 |
| Group 3 | EC2N group on GP(2^155) | RFC 2409 |
| Group 4 | EC2N group on GP(2^185) | RFC 2409 |
| Group 5 | 1536 bits MODP group | RFC 3526 |
IKE Traffic
To avoid problems with IKE packets hit some SPD rule and require to encrypt it with not yet established SA (that this packet perhaps is trying to establish), locally originated packets with UDP source port 500 are not processed with SPD. The same way packets with UDP destination port 500 that are to be delivered locally are not processed in incoming policy check.
Setup Procedure
To get IPsec to work with automatic keying using IKE-ISAKMP you will have to configure policy, peer and proposal (optional) entries.
For manual keying you will have to configure policy and manual-sa entries.
Warning: Ipsec is very sensitive to time changes. If both ends of the IpSec tunnel are not synchronizing time equally(for example, different NTP servers not updating time with the same timestamp), tunnels will break and will have to be established again.
Peer configuration
Sub-menu: /ip ipsec peer
Peer configuration settings are used to establish connections between IKE daemons (phase 1 configuration). This connection then will be used to negotiate keys and algorithms for SAs.
| Property | Description |
|---|---|
| address (IP[/Netmask]:port; Default: 0.0.0.0/32:500) | Address prefix. If remote peer's address matches this prefix, then this peer configuration is used in authentication and establishment of phase 1. If several peer's addresses match several configuration entries, the most specific one (i.e. the one with largest netmask) will be used. |
| auth-method (pre-shared-key | rsa-signature; Default: pre-shared-key) | Authentication method:
|
| certificate (string; Default: ) | Name of a certificate on the local side (signing packets; the certificate must have private key). Applicable if RSA signature authentication method is used. |
| dh-group (ec2n155 | ec2n185 | modp1024 | modp1536 | modp768; Default: modp1024) | Diffie-Hellman group (cipher strength) |
| dpd-interval (disable-dpd | time; Default: disable-dpd) | Dead peer detection interval. If set to disable-dpd, dead peer detection will not be used. |
| dpd-maximum-failures (integer: 1..100; Default: 5) | Maximum count of failures until peer is considered to be dead. |
| enc-algorithm (3des | aes-128 | aes-192 | aes-256 | des | blowfish | camellia-128 | camellia-192 | camellia-256; Default: 3des) | Encryption algorithm. blowfish, camellia algorithms are supported starting from v4.5. |
| exchange-mode (aggressive | base | main; Default: main) | Different ISAKMP phase 1 exchange modes according to RFC 2408. Do not use other modes then main unless you know what you are doing. |
| generate-policy (yes | no; Default: no) | Allow this peer to establish SA for non-existing policies. Such policies are created dynamically for the lifetime of SA. This way it is possible, for example, to create IPsec secured L2TP tunnels, or any other setup where remote peer's IP address is not known at the configuration time. |
| hash-algorithm (md5 | sha1; Default: md5) | Hashing algorithm. SHA (Secure Hash Algorithm) is stronger, but slower. |
| lifebytes (Integer: 0..4294967295; Default: 0) | Phase 1 lifetime: specifies how much bytes can be transferred before SA is discarded. If set to 0, SA will not be discarded due to byte count excess. |
| lifetime (time; Default: 1d) | Phase 1 lifetime: specifies how long the SA will be valid |
| nat-traversal (yes | no; Default: no) | Use Linux NAT-T mechanism to solve IPsec incompatibility with NAT routers inbetween IPsec peers. This can only be used with ESP protocol (AH is not supported by design, as it signes the complete packet, including IP header, which is changed by NAT, rendering AH signature invalid). The method encapsulates IPsec ESP traffic into UDP streams in order to overcome some minor issues that made ESP incompatible with NAT. |
| proposal-check (claim | exact | obey | strict; Default: obey) | Phase 2 lifetime check logic:
|
| remote-certificate (string; Default: ) | Name of a certificate for authenticating the remote side (validating packets; no private key required). Applicable if RSA signature authentication method is used |
| secret (string; Default: "") | Secret string (in case pre-shared key authentication is used). If it starts with '0x', it is parsed as a hexadecimal value |
| send-initial-contact (yes | no; Default: yes) | Specifies whether to send initial IKE information or wait for remote side. |
Note: IPSec phase information is erased, when /ip ipsec peer configuration is modified on the fly (for example remote-peers information is erased, when peer configuration is modified.
Policy
Sub-menu: /ip ipsec policy
Policy table is needed to determine whether security settings should be applied to a packet.
| Property | Description |
|---|---|
| action (discard | encrypt | none; Default: encrypt) | Specifies what to do with packet matched by the policy.
|
| dst-address (IP/Mask:Port; Default: 0.0.0.0/32:any) | Destination prefix and port. |
| ipsec-protocols (ah|esp; Default: esp) | Specifies what combination of Authentication Header and Encapsulating Security Payload protocols you want to apply to matched traffic. |
| level (require | unique | use; Default: require) | Specifies what to do if some of the SAs for this policy cannot be found:
|
| manual-sa (string | none; Default: none) | Name of manual-sa template that will be used to create SAs for this policy. If set to none, manual keys are not used. |
| priority (Integer: -2147483646..2147483647; Default: 0) | Policy ordering classificator (signed integer). Larger number means higher priority. |
| proposal (string; Default: default) | Name of proposal information that will be sent by IKE daemon to establish SAs for this policy |
| protocol (all | egp | ggp | icmp | igmp | ...; Default: all) | IP packet protocol to match. |
| sa-dst-address (IP; Default: 0.0.0.0) | SA destination IP address (remote peer). |
| sa-src-address (IP; Default: 0.0.0.0) | SA source IP address (local peer). |
| src-address (IP/Mask:Port; Default: 0.0.0.0/32:any) | Source IP prefix |
| tunnel (yes | no; Default: no) | Specifies whether to use tunnel mode |
Command /ip ipsec policy print stats will show current status of the policy. Additional read-only parameters will be printed.
| Property | Description |
|---|---|
| in-accepted (integer) | How many incoming packets were passed by the policy without an attempt to decrypt. |
| in-dropped (integer) | How many incoming packets were dropped by the policy without an attempt to decrypt |
| in-transformed (integer) | How many incoming packets were decrypted (ESP) and/or verified (AH) by the policy |
| out-accepted (integer) | How many outgoing packets were passed by the policy without an attempt to encrypt |
| out-dropped (integer) | How many outgoing packets were dropped by the policy without an attempt to encrypt |
| out-transformed (integer) | How many outgoing packets were encrypted (ESP) and/or verified (AH) by the policy |
| ph2-state (expired | no-phase2 | established) | Indication of the progress of key establishing. |
Note: All packets are IPIP encapsulated in tunnel mode, and their new IP header's src-address and dst-address are set to sa-src-address and sa-dst-address values of this policy. If you do not use tunnel mode (id est you use transport mode), then only packets whose source and destination addresses are the same as sa-src-address and sa-dst-address can be processed by this policy. Transport mode can only work with packets that originate at and are destined for IPsec peers (hosts that established security associations). To encrypt traffic between networks (or a network and a host) you have to use tunnel mode.
Proposal settings
Sub-menu: /ip ipsec proposal
Proposal information that will be sent by IKE daemon to establish SAs for this policy. Configured proposals are set in policy configuration.
| Property | Description |
|---|---|
| auth-algorithms (md5|sha1|null; Default: sha1) | Allowed algorithms for authorization. |
| enc-algorithms (null|des|3des|aes-128|aes-192|aes-256|blowfish|camellia-128 | camellia-192 | camellia-256 | twofish; Default: 3des) | Allowed algorithms and key lengths to use for SAs. |
| lifetime (time; Default: 30m) | How long to use SA before throwing it out. |
| pfs-group (ec2n155 | ec2n185 | modp1024 | modp1536 | modp768 | ...; Default: modp1024) | Diffie-Helman group used for Perfect Forward Secrecy. |
Manual SA
Sub-menu: /ip ipsec manual-sa
Installed SA
Sub-menu: /ip ipsec installed-sa
This facility provides information about installed security associations including the keys.
Flushing SAs
Sometimes after incorrect/incomplete negotiations took place, it is required to flush manually the installed SA table so that SA could be renegotiated. This option is provided by the /ip ipsec installed-sa flush command.
This command accepts only one property:
| Property | Description |
|---|---|
| sa-type (ah | all | esp; Default: all) | Specifies SA types to flush.
|
Remote Peers
Sub-menu: /ip ipsec remote-peers
This submenu provides you with various statistics about remote peers that currently have established phase 1 connections with this router. Note that if peer doesn't show up here, it doesn't mean that no IPsec traffic is being exchanged with it. For example, manually configured SAs is used, then remote peer will not show up here.
Read only properties:
| Property | Description |
|---|---|
| local-address (IP) | Local ISAKMP SA address. |
| remote-address (IP) | Peer's IP address. |
| side (initiator | responder) | Shows which side initiated the Phase1 negotiation. |
| state (string) | State of phase 1 negotiation with the peer. |
Statistics
Sub-menu: /ip ipsec statistics
(needs editing)
Application Examples
Site to Site IpSec Tunnel
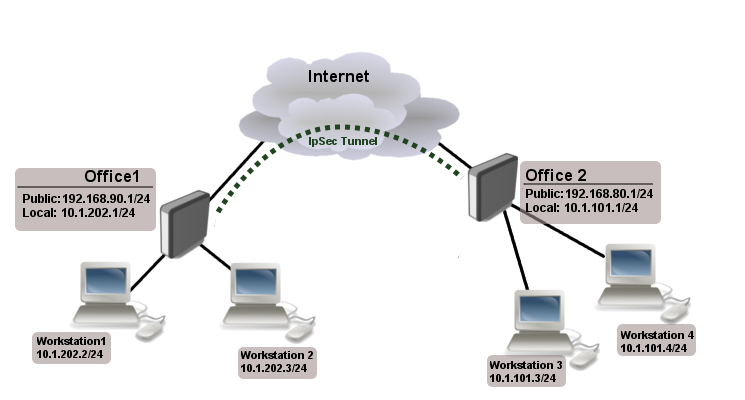
Consider setup as illustrated below
Two remote office routers are connected to internet and office workstations behind routers are NATed. Each office has its own local subnet, 10.1.202.0/24 for Office1 and 10.1.101.0/24 for Office2. Both remote offices needs secure tunnel to local networks behind routers.
IP Connectivity
On both routers ether1 is used as wan port and ether2 is used to connect workstations. Also NAT rules are set tu masquerade local networks.
Office1 router:
/ip address add address=192.168.90.1/24 interface=ether1 add address=10.1.202.1/24 interface=ether2 /ip route add gateway=192.168.90.254 /ip firewall nat add chain=srcnat out-interface=ether1 action=masquerade
Office2 router:
/ip address add address=192.168.80.1/24 interface=ether1 add address=10.1.101.1/24 interface=ether2 /ip route add gateway=192.168.80.254 /ip firewall nat add chain=srcnat out-interface=ether1 action=masquerade
IpSec Peer's config
Next step is to add peer's configuration. We need to specify peers address and port and pre-shared-key. Other parameters are left to default values.
Office1 router:
/ip ipsec peer add address=192.168.80.1/32:500 auth-method=pre-shared-key secret="test"
Office2 router:
/ip ipsec peer add address=192.168.90.1/32:500 auth-method=pre-shared-key secret="test"
Policy and proposal
It is important that proposed authentication and encryption algorithms match on both routers. In this example we can use predefined "default" proposal
[admin@MikroTik] /ip ipsec proposal> print
Flags: X - disabled
0 name="default" auth-algorithms=sha1 enc-algorithms=3des lifetime=30m
pfs-group=modp1024
As we already have proposal as a next step we need correct IpSec policy. We want to encrypt traffic coming form 10.1.202.0/24 to 10.1.101.0/24 and vice versa.
Office1 router:
/ip ipsec policy add src-address=10.1.202.0/24:any dst-address=10.1.101.0/24:any \ sa-src-address=192.168.90.1 sa-dst-address=192.168.80.1 \ tunnel=yes action=encrypt proposal=default
Office2 router:
/ip ipsec policy add src-address=10.1.101.0/24:any dst-address=10.1.202.0/24:any \ sa-src-address=192.168.80.1 sa-dst-address=192.168.90.1 \ tunnel=yes action=encrypt proposal=default
Note that we configured tunnel mode instead of transport, as this is site to site encryption.
NAT Bypass
At this point if you will try to establish IpSec tunnel it will not work, packets will be rejected. This is because both routers have NAT rules that is changing source address after packet is encrypted. Remote router reiceves encrypted packet but is unable to decrypt it because source address do not match address specified in policy configuration.
To fix this we need to set up NAT bypass rule.
Office1 router:
/ip firewall nat add chain=srcnat action=accept place-before=0 \ src-address=10.1.202.0/24 dst-address=10.1.101.0/24
Office2 router:
/ip firewall nat add chain=srcnat action=accept place-before=0 \ src-address=10.1.101.0/24 dst-address=10.1.202.0/24
It is very important that bypass rule is placed at the top of all other NAT rules.
Note: If you previously tried to establish tunnel before NAT bypass rule was added, you have to clear connection table from existing connection or restart the routers
[ Top | Back to Content ]