Manual:Virtual Routing and Forwarding: Difference between revisions
m (Protected "Virtual Routing and Forwarding": will be in manual [edit=sysop:move=sysop]) |
mNo edit summary |
||
| Line 24: | Line 24: | ||
=== Configuration === | === Configuration === | ||
'''Mikrotik''': | '''Mikrotik''': | ||
Addresses are like this: | Addresses are like this: | ||
| Line 39: | Line 39: | ||
/ip route vrf add interfaces=ether2 route-distinguisher=1.1.1.1:111 export-route-targets=1.1.1.1:111 \ | /ip route vrf add interfaces=ether2 route-distinguisher=1.1.1.1:111 export-route-targets=1.1.1.1:111 \ | ||
import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-one | import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-one | ||
| |||
/ip route vrf add interfaces=ether3 route-distinguisher=2.2.2.2:222 export-route-targets=2.2.2.2:222 \ | /ip route vrf add interfaces=ether3 route-distinguisher=2.2.2.2:222 export-route-targets=2.2.2.2:222 \ | ||
import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-two | import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-two | ||
| Line 46: | Line 47: | ||
/routing bgp peer add remote-address=10.0.11.202 remote-as=64550 instance=default address-families=vpnv4 | /routing bgp peer add remote-address=10.0.11.202 remote-as=64550 instance=default address-families=vpnv4 | ||
'''Cisco''': | '''Cisco''': (note that VRF names are not important, they are the same on both MT and Cisco only by convention) | ||
interface FastEthernet0/0 | interface FastEthernet0/0 | ||
ip address 10.0.11.202 255.255.255.0 | ip address 10.0.11.202 255.255.255.0 | ||
| |||
ip vrf cust-one | ip vrf cust-one | ||
rd 1.1.1.1:111 | rd 1.1.1.1:111 | ||
| Line 55: | Line 57: | ||
route-target import 2.2.2.2:222 | route-target import 2.2.2.2:222 | ||
exit | exit | ||
| |||
ip vrf cust-two | ip vrf cust-two | ||
rd 2.2.2.2:222 | rd 2.2.2.2:222 | ||
| Line 61: | Line 64: | ||
route-target import 2.2.2.2:222 | route-target import 2.2.2.2:222 | ||
exit | exit | ||
| |||
interface Tunnel1 | interface Tunnel1 | ||
ip vrf forwarding cust-one | ip vrf forwarding cust-one | ||
| Line 66: | Line 70: | ||
tunnel source 10.0.11.202 | tunnel source 10.0.11.202 | ||
tunnel destination X.X.X.X | tunnel destination X.X.X.X | ||
| |||
interface Tunnel2 | interface Tunnel2 | ||
ip vrf forwarding cust-two | ip vrf forwarding cust-two | ||
ip address 3.3.3.3 255.255.255.0 | ip address 3.3.3.3 255.255.255.0 | ||
tunnel source 10.0.11.202 | tunnel source 10.0.11.202 | ||
tunnel destination | tunnel destination Y.Y.Y.Y | ||
| |||
router bgp 64550 | router bgp 64550 | ||
neighbor 10.0.0.131 remote-as 64550 | neighbor 10.0.0.131 remote-as 64550 | ||
| Line 86: | Line 92: | ||
=== Results === | === Results === | ||
''' | ==== Cisco ==== | ||
'''VPNv4 routing table:''' | |||
C7200#show ip bgp vpnv4 all | C7200#show ip bgp vpnv4 all | ||
BGP table version is 20, local router ID is 10.0.11.202 | BGP table version is 20, local router ID is 10.0.11.202 | ||
| Line 101: | Line 110: | ||
*> 2.2.2.0/24 0.0.0.0 0 32768 ? | *> 2.2.2.0/24 0.0.0.0 0 32768 ? | ||
*> 3.3.3.0/24 0.0.0.0 0 32768 ? | *> 3.3.3.0/24 0.0.0.0 0 32768 ? | ||
'''Routing table for customer one:''' | |||
C7200#show ip route vrf cust-one | C7200#show ip route vrf cust-one | ||
| Line 119: | Line 130: | ||
B 3.3.3.0 is directly connected, 00:01:20, Tunnel2 | B 3.3.3.0 is directly connected, 00:01:20, Tunnel2 | ||
''' | ==== Mikrotik ==== | ||
[admin@MikroTik] | |||
'''VPNv4 routing table:''' | |||
[admin@MikroTik] > vpnv4-route print detail | |||
Flags: N - no label | Flags: N - no label | ||
0 route-distinguisher=1.1.1.1:111 dst-address=2.2.2.0/24 gateway=10.0.11.202 | 0 route-distinguisher=1.1.1.1:111 dst-address=2.2.2.0/24 gateway=10.0.11.202 | ||
interface=ether1 in-label=17 out-label=16 bgp-local-pref=100 bgp-med=0 | interface=ether1 in-label=17 out-label=16 bgp-local-pref=100 bgp-med=0 | ||
bgp-origin=incomplete bgp-ext-communities="RT:1.1.1.1:111" | bgp-origin=incomplete bgp-ext-communities="RT:1.1.1.1:111" | ||
| |||
1 route-distinguisher=2.2.2.2:222 dst-address=3.3.3.0/24 gateway=10.0.11.202 | 1 route-distinguisher=2.2.2.2:222 dst-address=3.3.3.0/24 gateway=10.0.11.202 | ||
interface=ether1 in-label=18 out-label=17 bgp-local-pref=100 bgp-med=0 | interface=ether1 in-label=18 out-label=17 bgp-local-pref=100 bgp-med=0 | ||
bgp-origin=incomplete bgp-ext-communities="RT:2.2.2.2:222" | bgp-origin=incomplete bgp-ext-communities="RT:2.2.2.2:222" | ||
| |||
2 route-distinguisher=1.1.1.1:111 dst-address=1.1.1.0/24 interface=ether2 | 2 route-distinguisher=1.1.1.1:111 dst-address=1.1.1.0/24 interface=ether2 | ||
in-label=16 bgp-ext-communities="RT:1.1.1.1:111" | in-label=16 bgp-ext-communities="RT:1.1.1.1:111" | ||
[admin@MikroTik] | '''All IP routing tables:''' | ||
[admin@MikroTik] > /ip route p detail | |||
Flags: X - disabled, A - active, D - dynamic, | Flags: X - disabled, A - active, D - dynamic, | ||
C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, | C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme, | ||
B - blackhole, U - unreachable, P - prohibit | B - blackhole, U - unreachable, P - prohibit | ||
| |||
# ---------------------- routes for customer 1 -------------------------- | |||
# a connected route that is bound to a particular VRF | |||
0 ADC dst-address=1.1.1.0/24 pref-src=1.1.1.1 interface=ether2 distance=0 scope=10 | 0 ADC dst-address=1.1.1.0/24 pref-src=1.1.1.1 interface=ether2 distance=0 scope=10 | ||
routing-mark=cust-one | routing-mark=cust-one | ||
| |||
# this route is received from Cisco and imported to customer's 1 VRF | |||
1 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | 1 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | ||
gateway-state=recursive distance=20 scope=40 target-scope=30 | gateway-state=recursive distance=20 scope=40 target-scope=30 | ||
routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | ||
bgp-ext-communities="RT:1.1.1.1:111" | bgp-ext-communities="RT:1.1.1.1:111" | ||
| |||
# from Cisco | |||
2 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | 2 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | ||
gateway-state=recursive distance=20 scope=40 target-scope=30 | gateway-state=recursive distance=20 scope=40 target-scope=30 | ||
routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | ||
bgp-ext-communities="RT:2.2.2.2:222" | bgp-ext-communities="RT:2.2.2.2:222" | ||
| |||
# ---------------------- routes for customer 2 -------------------------- | |||
# "locally" reimported via bgp to a different table | |||
3 ADb dst-address=1.1.1.0/24 distance=20 routing-mark=cust-two | 3 ADb dst-address=1.1.1.0/24 distance=20 routing-mark=cust-two | ||
bgp-ext-communities="RT:1.1.1.1:111" | bgp-ext-communities="RT:1.1.1.1:111" | ||
| |||
# from Cisco and imported to customer's 2 VRF | |||
4 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | 4 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | ||
gateway-state=recursive distance=20 scope=40 target-scope=30 | gateway-state=recursive distance=20 scope=40 target-scope=30 | ||
routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | ||
bgp-ext-communities="RT:1.1.1.1:111" | bgp-ext-communities="RT:1.1.1.1:111" | ||
| |||
# from Cisco | |||
5 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | 5 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main | ||
gateway-state=recursive distance=20 scope=40 target-scope=30 | gateway-state=recursive distance=20 scope=40 target-scope=30 | ||
routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete | ||
bgp-ext-communities="RT:2.2.2.2:222" | bgp-ext-communities="RT:2.2.2.2:222" | ||
| |||
# ------------------------- "main" table ------------------------------ | |||
6 A S dst-address=0.0.0.0/0 gateway=10.0.0.1 interface=ether1 gateway-table=main | 6 A S dst-address=0.0.0.0/0 gateway=10.0.0.1 interface=ether1 gateway-table=main | ||
gateway-state=reachable distance=1 scope=30 target-scope=10 | gateway-state=reachable distance=1 scope=30 target-scope=10 | ||
| |||
7 ADC dst-address=10.0.0.0/24 pref-src=10.0.0.131 interface=ether1 distance=0 | 7 ADC dst-address=10.0.0.0/24 pref-src=10.0.0.131 interface=ether1 distance=0 | ||
scope=10 | scope=10 | ||
Revision as of 11:16, 2 June 2008
Preliminary version - will be expanded!
Description
New routing-test package in version 3.x allows to create multiple Virtual Routing and Forwarding instances on a single router. This is useful for BGP based MPLS VPNs. Unlike MPLS BGP VPLS, which is OSI Layer 2 technology, BGP VPNs works in Layer 3 and as such exchanges IP prefixes between routers. VRFs solves the problem of overlapping IP prefixes, and provides the required privacy (via separated routing for different VPNs).
To create a VRF, configure it under /ip route vrf. You can now add routes to that VRF - simply specify routing-mark attribute. Connected routes from interfaces belonging to a VRF will be installed in right routing table automatically.
Technically VRFs are based on policy routing. There is exactly one policy routing table for each active VRF. Note that existing policy routing support will not be changed, but you will not be able to have policy routing within a VRF. The main difference between VRF tables and simple policy routing is that routes in VRF tables resolve nexthops in their own routing table by default, while policy routes always use main routing table. Read-only route attribute gateway-table displays information about which table is used for a particular route (default is main).
The real fun begins when you start to configure BGP. You can use multiprotocol BGP to distribute those routes - not only to other routers, but also to different routing tables in the router itself. Route installation in VRF tables is controlled by BGP extended communities attribute. Configure import and export lists under /ip route vrf, import-route-target and export-route-target. Export route target list for a VRF should contained at least the route distinguisher for that VRF.
Active multiprotocol BGP routes are installed in a separate routing table, which can be observed at /routing bgp vpnv4-route. These so called VPNv4 routes has prefix that consists of route-distinguisher and an IPv4 route prefix. This way you can have overlapping IPv4 prefixes distributed in BGP. route-distinguisher can be configured under /ip route vrf. There should be one-to-one correspondence between route-distinguishers and VRFs.
Please note that a VPNv4 route will be distributed only if it has a valid MPLS label. You need to install mpls package and configure valid label range (default is OK) for this to work.
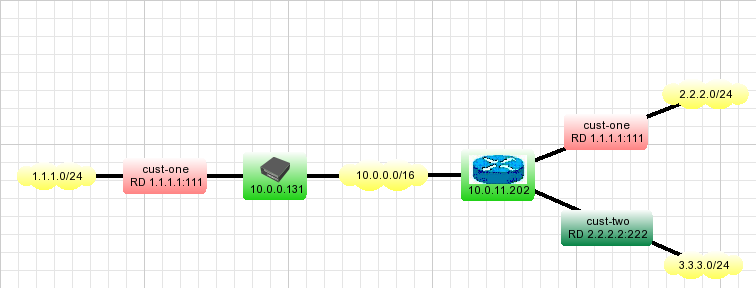
An example with Cisco
In this example we create two VPNs for cust-one and cust-two, and exchange all routes between them.
Configuration
Mikrotik:
Addresses are like this:
[admin@MikroTik] > /ip address p Flags: X - disabled, I - invalid, D - dynamic # ADDRESS NETWORK BROADCAST INTERFACE 0 10.0.0.131/24 10.0.0.0 10.0.0.255 ether1 1 1.1.1.1/24 1.1.1.0 1.1.1.255 ether2
Add default route:
/ip route add gateway=10.0.0.1
Configure VRFs:
/ip route vrf add interfaces=ether2 route-distinguisher=1.1.1.1:111 export-route-targets=1.1.1.1:111 \ import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-one /ip route vrf add interfaces=ether3 route-distinguisher=2.2.2.2:222 export-route-targets=2.2.2.2:222 \ import-route-targets=1.1.1.1:111,2.2.2.2:222 routing-mark=cust-two
Configure VPNv4 redistribution and multiprotocol BGP:
/routing bgp instance set default as=64550 redistribute-connected=yes vrf=cust-one,cust-two /routing bgp peer add remote-address=10.0.11.202 remote-as=64550 instance=default address-families=vpnv4
Cisco: (note that VRF names are not important, they are the same on both MT and Cisco only by convention)
interface FastEthernet0/0 ip address 10.0.11.202 255.255.255.0 ip vrf cust-one rd 1.1.1.1:111 route-target export 1.1.1.1:111 route-target import 1.1.1.1:111 route-target import 2.2.2.2:222 exit ip vrf cust-two rd 2.2.2.2:222 route-target export 2.2.2.2:222 route-target import 1.1.1.1:111 route-target import 2.2.2.2:222 exit interface Tunnel1 ip vrf forwarding cust-one ip address 2.2.2.2 255.255.255.0 tunnel source 10.0.11.202 tunnel destination X.X.X.X interface Tunnel2 ip vrf forwarding cust-two ip address 3.3.3.3 255.255.255.0 tunnel source 10.0.11.202 tunnel destination Y.Y.Y.Y router bgp 64550 neighbor 10.0.0.131 remote-as 64550 address-family vpnv4 neighbor 10.0.0.131 activate neighbor 10.0.0.131 send-community both exit-address-family address-family ipv4 vrf cust-one redistribute connected exit-address-family address-family ipv4 vrf cust-two redistribute connected exit-address-family
Results
Cisco
VPNv4 routing table:
C7200#show ip bgp vpnv4 all
BGP table version is 20, local router ID is 10.0.11.202
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale
Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 1.1.1.1:111 (default for vrf cust-one)
*>i1.1.1.0/24 10.0.0.131 100 0 ?
*> 2.2.2.0/24 0.0.0.0 0 32768 ?
*> 3.3.3.0/24 0.0.0.0 0 32768 ?
Route Distinguisher: 2.2.2.2:222 (default for vrf cust-two)
*>i1.1.1.0/24 10.0.0.131 100 0 ?
*> 2.2.2.0/24 0.0.0.0 0 32768 ?
*> 3.3.3.0/24 0.0.0.0 0 32768 ?
Routing table for customer one:
C7200#show ip route vrf cust-one
Routing Table: cust-one
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is not set
1.0.0.0/24 is subnetted, 1 subnets
B 1.1.1.0 [200/0] via 10.0.0.131, 00:02:51
2.0.0.0/24 is subnetted, 1 subnets
C 2.2.2.0 is directly connected, Tunnel1
3.0.0.0/24 is subnetted, 1 subnets
B 3.3.3.0 is directly connected, 00:01:20, Tunnel2
Mikrotik
VPNv4 routing table:
[admin@MikroTik] > vpnv4-route print detail
Flags: N - no label
0 route-distinguisher=1.1.1.1:111 dst-address=2.2.2.0/24 gateway=10.0.11.202
interface=ether1 in-label=17 out-label=16 bgp-local-pref=100 bgp-med=0
bgp-origin=incomplete bgp-ext-communities="RT:1.1.1.1:111"
1 route-distinguisher=2.2.2.2:222 dst-address=3.3.3.0/24 gateway=10.0.11.202
interface=ether1 in-label=18 out-label=17 bgp-local-pref=100 bgp-med=0
bgp-origin=incomplete bgp-ext-communities="RT:2.2.2.2:222"
2 route-distinguisher=1.1.1.1:111 dst-address=1.1.1.0/24 interface=ether2
in-label=16 bgp-ext-communities="RT:1.1.1.1:111"
All IP routing tables:
[admin@MikroTik] > /ip route p detail
Flags: X - disabled, A - active, D - dynamic,
C - connect, S - static, r - rip, b - bgp, o - ospf, m - mme,
B - blackhole, U - unreachable, P - prohibit
# ---------------------- routes for customer 1 --------------------------
# a connected route that is bound to a particular VRF
0 ADC dst-address=1.1.1.0/24 pref-src=1.1.1.1 interface=ether2 distance=0 scope=10
routing-mark=cust-one
# this route is received from Cisco and imported to customer's 1 VRF
1 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main
gateway-state=recursive distance=20 scope=40 target-scope=30
routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete
bgp-ext-communities="RT:1.1.1.1:111"
# from Cisco
2 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main
gateway-state=recursive distance=20 scope=40 target-scope=30
routing-mark=cust-one bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete
bgp-ext-communities="RT:2.2.2.2:222"
# ---------------------- routes for customer 2 --------------------------
# "locally" reimported via bgp to a different table
3 ADb dst-address=1.1.1.0/24 distance=20 routing-mark=cust-two
bgp-ext-communities="RT:1.1.1.1:111"
# from Cisco and imported to customer's 2 VRF
4 ADb dst-address=2.2.2.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main
gateway-state=recursive distance=20 scope=40 target-scope=30
routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete
bgp-ext-communities="RT:1.1.1.1:111"
# from Cisco
5 ADb dst-address=3.3.3.0/24 gateway=10.0.11.202 interface=ether1 gateway-table=main
gateway-state=recursive distance=20 scope=40 target-scope=30
routing-mark=cust-two bgp-local-pref=100 bgp-med=0 bgp-origin=incomplete
bgp-ext-communities="RT:2.2.2.2:222"
# ------------------------- "main" table ------------------------------
6 A S dst-address=0.0.0.0/0 gateway=10.0.0.1 interface=ether1 gateway-table=main
gateway-state=reachable distance=1 scope=30 target-scope=10
7 ADC dst-address=10.0.0.0/24 pref-src=10.0.0.131 interface=ether1 distance=0
scope=10
References
RFC 4364: BGP/MPLS IP Virtual Private Networks (VPNs)
MPLS Fundamentals, chapter 7, Luc De Ghein, Cisco Press 2006